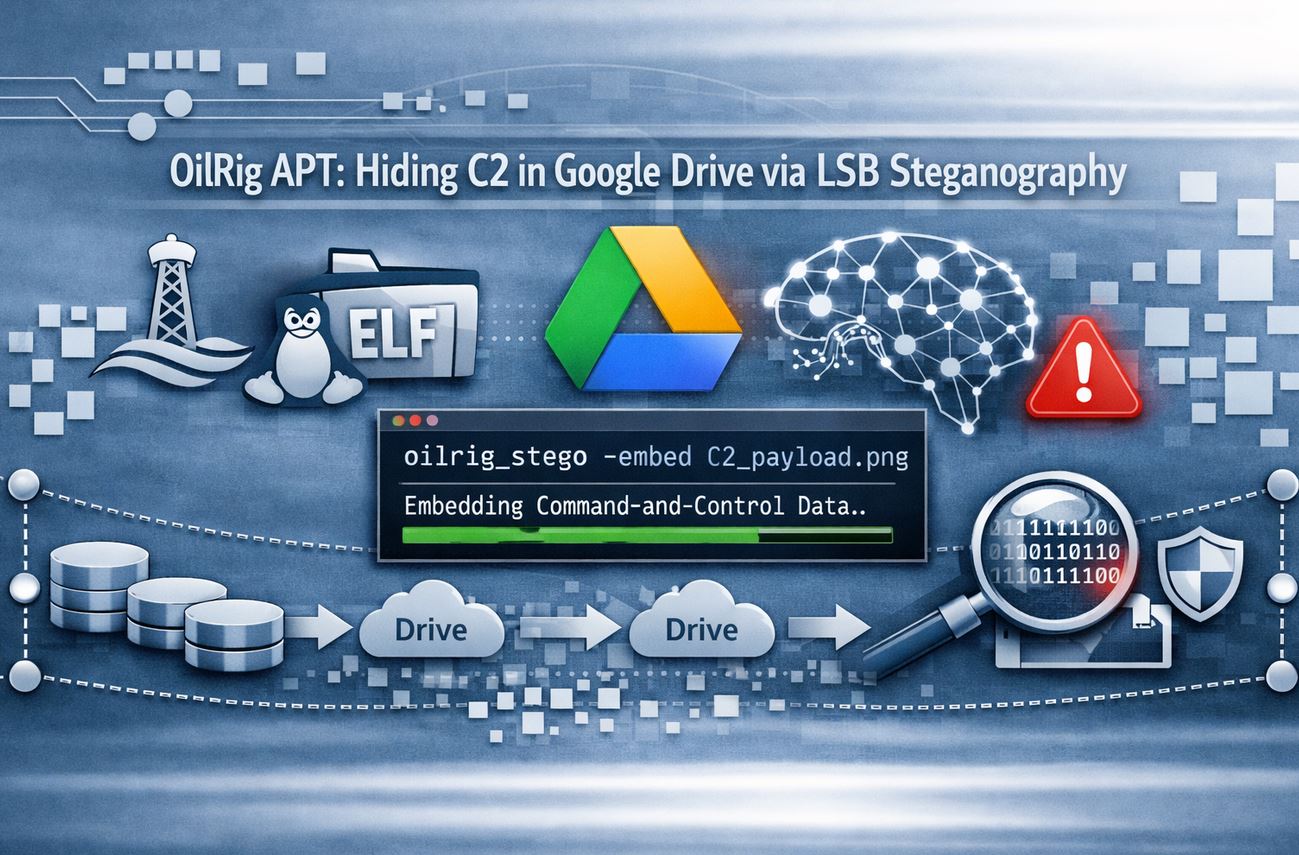
State-sponsored cyberespionage is moving away from overt malware delivery toward “living off the cloud” and hiding in plain sight. In a sophisticated new campaign, the Iranian threat group OilRig (also known as APT34 or Helix Kitten) has been observed using LSB (Least Significant Bit) steganography to embed command-and-control (C2) configurations within seemingly harmless images hosted on Google Drive.
By abusing trusted platforms like GitHub, Google Drive, and Telegram, OilRig has created a communication pipeline that bypasses traditional network security filters. This campaign, discovered by analysts at the 360 Advanced Threat Research Institute, highlights the group’s evolving tactical maturity in late 2025 and early 2026.
Who is OilRig?
Active since at least 2016, OilRig is a prominent Iranian state-sponsored group focused on high-value targets across the Middle East, the U.S., and Europe. Their primary mission is the exfiltration of geostrategic, military, and political intelligence from:
- Government & Military Agencies
- Financial & Energy Sectors
- Telecom & Chemical Infrastructure
The Attack Chain: From Social Unrest to System Compromise
The campaign leverages real-world geopolitical tension as a psychological “hook.” The attackers utilized a malicious Excel file titled “Final List_Tehran.xlsm,” themed around Iranian social protests.
1. The Phishing Entry Point
The document references dates in the Iranian calendar corresponding to January 2026, making it highly relevant to local targets. Once the victim enables macros, a sophisticated VBA script triggers. Instead of downloading a payload directly—which might be flagged—it decodes C# source code hidden in the document’s CustomXMLParts.
2. Just-In-Time Compilation
The script uses the legitimate Windows compiler (csc.exe) to build a malicious loader locally on the machine: AppVStreamingUX_Multi_User.dll. This technique, known as Compile-on-Endpoint, is designed to evade signature-based antivirus tools that only look for pre-compiled malicious binaries.
Deep Dive: LSB Steganography and the Google Drive Payload
The most innovative stage of the attack involves how the malware retrieves its instructions.
What is LSB Steganography?
Digital images are made of pixels, each represented by bits (e.g., Red, Green, Blue values). Least Significant Bit (LSB) steganography involves replacing the last bit of a pixel’s color value with a bit of secret data.
- Changing the bit from a
0to a1alters the color so slightly that the human eye cannot detect the difference. - For an AI or security scanner, the file appears to be a standard, legitimate PNG.
The “MIO9.png” Execution
- The loader connects to a GitHub repository to find a hidden Google Drive link.
- It downloads an image named “MIO9.png” from Google Drive.
- Using a custom extraction algorithm, the malware “reads” the last bits of the pixels to reconstruct an encrypted C2 configuration.
- After Base64 and XOR decryption, the malware reveals its true C2 setup: a Telegram Bot token and a chat ID used for exfiltrating data and receiving commands.
In-Memory Persistence and Telegram C2
To maintain a “fileless” footprint, OilRig utilizes five distinct modules (m1-m5) that are loaded directly into memory. This prevents security software from scanning the files on the hard drive. These modules handle:
- Persistence (pr): Ensuring the malware survives a system reboot via Windows Scheduled Tasks.
- File Operations (up/do): Uploading and downloading sensitive documents.
- Execution (cm/runApp): Running remote commands or launching new applications.
The attackers use the Telegram Bot API as a heartbeat mechanism. Every time the infected machine wakes up, it sends an “is online” message to the attacker’s Telegram chat, providing real-time confirmation of the breach.
| Component | Function | Technical Detail |
|---|---|---|
| Initial Bait | Phishing | Macro-enabled Excel (.xlsm) |
| Configuration Host | Google Drive | LSB Steganographic PNG image |
| C2 Protocol | Telegram API | Stealthy outbound HTTPS traffic |
| Execution | In-Memory | DLL loading via AppVStreamingUX |
Export to Sheets
Expert Insights: Why This Attack is Difficult to Stop
As a senior analyst, I categorize this as a “High-Stealth” campaign. By routing traffic through Google, GitHub, and Telegram, OilRig ensures that network traffic looks like standard employee activity.
Risk-Impact Analysis: The use of LSB steganography means that even if a security tool inspects the downloaded image, it will find no malicious code—only “noisy” pixel data. This shifts the burden of detection from the Network (where traffic is encrypted and trusted) to the Endpoint (where behavioral anomalies must be caught).
FAQs
What is LSB steganography?
It is a method of hiding data inside an image by slightly altering the least significant bits of the pixels. It is virtually invisible to the naked eye and many automated scanners.
How does OilRig use Telegram in this attack?
Instead of a traditional server, they use a Telegram Bot. The malware communicates with the bot to report system status and receive commands, making the malicious traffic look like legitimate encrypted chat traffic.
Why did they use GitHub and Google Drive?
These are “Trusted Domains.” Most organizations do not block GitHub or Google Drive, allowing the malware to bypass firewall rules and domain reputation filters.
How can I detect if I’m infected?
Look for unusual processes calling csc.exe (the C# compiler) or unexpected outbound connections to Telegram APIs from non-chat applications.
Conclusion: Defending Against Living-Off-the-Cloud Tactics
The OilRig campaign proves that state-sponsored actors are prioritizing stealth over speed. By hiding C2 configurations in images and utilizing trusted cloud providers, they have created a highly resilient espionage infrastructure.
Actionable Recommendations:
- Disable Macros: Block Office macros by default via Group Policy for all external documents.
- Endpoint Visibility: Deploy EDR (Endpoint Detection and Response) solutions that can detect in-memory DLL loading and scheduled task manipulation.
- Network Anomalies: Monitor for persistent HTTPS connections to Telegram or GitHub from system processes (like
svchost.exeorcsc.exe) rather than user applications.
Are your cloud-trust policies too lenient? [Assess your APT Readiness] with our latest threat hunting guide to identify hidden steganographic threats in your network.