The Booking.com data breach has sent shockwaves across the travel and cybersecurity industries after the platform confirmed unauthorized access to customer booking information. As one of the world’s largest travel platforms, Booking.com processes millions of reservations across more than 28 million listings globally—making it a high-value target for cybercriminals.
In this Booking.com data breach, attackers gained access to sensitive personal information including names, email addresses, phone numbers, and reservation details. While no confirmed financial data theft has been reported, the exposure of personal and behavioral travel data introduces a severe risk of phishing, impersonation, and social engineering attacks.
This article breaks down:
- What happened in the Booking.com cyberattack
- How attackers exploit stolen travel data
- Real-world phishing campaigns already linked to the breach
- Security frameworks and defensive strategies
- Actionable steps for travelers and organizations
What Is the Booking.com Data Breach?
The Booking.com data breach refers to a cyber incident where unauthorized third parties accessed customer reservation data from Booking.com systems.
According to official disclosures, attackers were able to view:
- Full customer names
- Email addresses
- Phone numbers
- Physical addresses
- Reservation and accommodation details
- Additional user-provided booking notes
The company stated that financial data such as credit card information was not confirmed to be accessed, though investigations into data isolation remain ongoing.
Security researchers believe the breach is part of a broader trend targeting travel and hospitality platforms due to their rich troves of personal and behavioral data.
How the Booking.com Cyberattack Happened
While full technical details have not been disclosed, the attack pattern aligns with modern identity-based intrusion methods rather than traditional infrastructure breaches.
Likely Attack Vectors
Cybersecurity analysts suspect one or more of the following:
- Credential stuffing attacks
- Compromised hotel partner portals
- API abuse targeting booking systems
- Phishing-based credential theft
- Third-party integration exploitation
Historically, attackers have targeted hotel admin systems connected to Booking.com to send fraudulent payment requests directly to guests.
Threat Context: Why Booking Platforms Are High-Value Targets
Travel platforms store a unique combination of data that is extremely valuable on the cybercrime market:
- Identity data (names, contact details)
- Behavioral data (travel plans, destinations)
- Financial signals (payment intent, booking history)
- Timing intelligence (future travel dates)
This makes platforms like Booking.com ideal for:
- Targeted phishing campaigns
- Business Email Compromise (BEC)
- Identity theft
- Travel-related fraud
Real-World Impact: How Attackers Are Using Stolen Data
Evidence suggests that attackers are already operationalizing stolen data from the Booking.com data breach.
Observed Attack Patterns
Reports include:
- WhatsApp phishing messages referencing real bookings
- Fraudulent payment requests sent via email
- Impersonation of hotel staff
- Urgent “payment confirmation” scams
A key concern is precision social engineering—attackers use legitimate booking details to build trust before launching scams.
Example Attack Flow
- Attacker obtains reservation data
- Crafts a message impersonating hotel or Booking.com
- Includes real booking details (dates, names, hotel)
- Requests urgent payment or verification
- Victim unknowingly transfers money or shares credentials
Malware and Credential Theft Ecosystem Behind the Breach
This incident aligns with broader attack campaigns observed across the hospitality sector.
Security firms have previously identified:
- Vidar infostealer used to harvest credentials from hotel systems
- ClickFix malware used in phishing workflows
- PureRAT enabling remote system access and data exfiltration
These tools are often distributed through phishing emails, fake booking portals, or compromised hospitality dashboards.
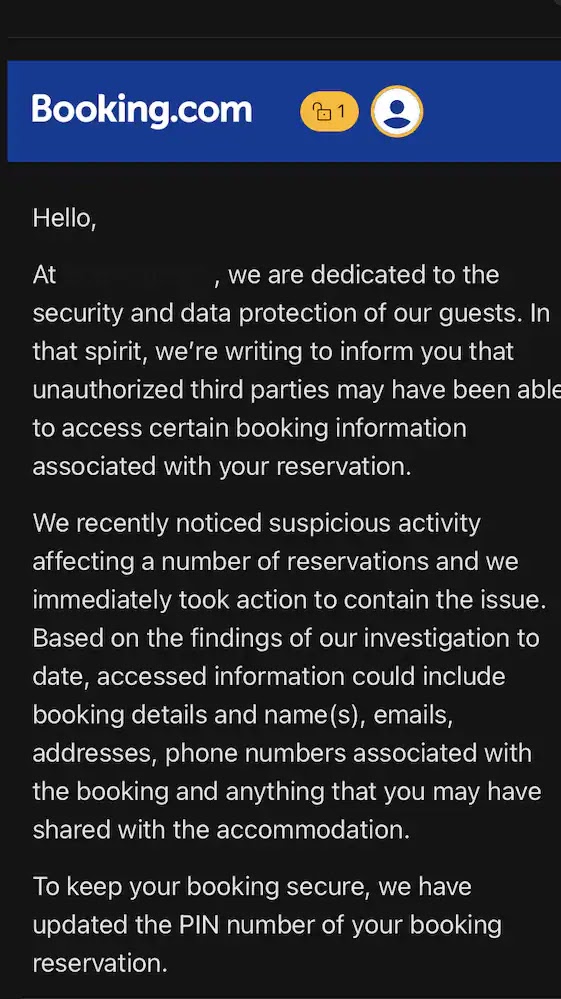
Booking.com’s Response to the Cyber Incident
Following detection of suspicious activity, Booking.com implemented several containment measures:
Immediate Actions Taken
- Reset PINs for affected reservations
- Notified impacted customers via email
- Blocked unauthorized access pathways
- Initiated internal forensic investigation
Security Statement Highlights
The company confirmed:
- No confirmed financial data theft
- Unauthorized access was limited to booking-related data
- Customers should ignore unsolicited payment requests
However, the lack of clarity around scope, geography, and timeline has raised concerns among security experts.
Role of Cybersecurity Firms and Threat Intelligence
Independent researchers and firms such as Secureworks and Sekoia.io have previously documented similar campaigns targeting travel platforms.
Key Observations from Threat Intelligence
- Attackers frequently reuse stolen credentials across platforms
- Hotel admin panels are common entry points
- Phishing kits are increasingly automated
- AI-generated phishing messages improve credibility
These findings suggest the Booking.com breach is part of a larger ecosystem of hospitality-targeted cybercrime.
Mapping the Attack to MITRE ATT&CK Framework
The Booking.com data breach aligns with several tactics in the MITRE ATT&CK framework:
Initial Access
- Phishing (T1566)
- Valid Accounts (T1078)
Credential Access
- Credential dumping (T1003)
- Brute force attacks (T1110)
Exfiltration
- Exfiltration over web services (T1567)
Impact
- Data exposure leading to fraud and impersonation
Understanding these mappings helps SOC teams build stronger detection rules.
Common Misconceptions About the Booking.com Breach
1. “No financial data means no risk”
False. Personal and travel data can enable highly convincing fraud.
2. “Only high-profile users are targeted”
Incorrect. Attackers often target mass datasets for scalable phishing.
3. “Password resets solve the issue”
Not sufficient. Stolen contextual data remains exploitable.
Cybersecurity Risks Emerging from the Incident
The Booking.com data breach introduces multiple downstream risks:
1. Phishing Attacks
Highly personalized scams using real booking details.
2. Identity Theft
Use of personal data for account creation or fraud.
3. Business Email Compromise
Targeting corporate travelers for financial fraud.
4. Secondary Credential Attacks
Reusing leaked emails across other platforms.
Best Practices: How to Protect Yourself
For Travelers
- Verify all payment requests via official app or website
- Never send payments via WhatsApp or SMS links
- Monitor email for spoofed Booking.com messages
- Use unique passwords for travel platforms
- Enable multi-factor authentication (MFA)
For Enterprises & Hotels
- Secure API integrations with strong authentication
- Monitor admin portals for abnormal access
- Implement zero trust principles
- Conduct phishing simulation training
- Log and analyze all guest communication channels
Zero Trust and Modern Defense Strategies
Organizations connected to platforms like Booking.com should adopt a Zero Trust security model, which assumes no implicit trust across systems.
Key Principles
- Continuous authentication
- Least privilege access
- Micro-segmentation
- Real-time monitoring
Framework Alignment
- NIST Cybersecurity Framework (Identify, Protect, Detect, Respond, Recover)
- ISO/IEC 27001 controls for access management
- MITRE ATT&CK for adversary simulation
Expert Insight: Why This Breach Matters
From a cybersecurity perspective, this incident highlights a shift toward data-driven social engineering attacks.
Key Insights
- Attackers no longer need financial data—behavioral data is enough
- Travel datasets are extremely time-sensitive and exploitable
- Human trust remains the weakest security layer
The combination of real booking data + timing context makes these attacks significantly more effective than traditional phishing.
FAQs About the Booking.com Data Breach
1. What happened in the Booking.com data breach?
Unauthorized attackers accessed customer booking information, including names, emails, and reservation details.
2. Was financial data stolen in the Booking.com breach?
No confirmed evidence suggests credit card data was accessed, but investigations are ongoing.
3. How are attackers using the stolen data?
They are launching phishing attacks via email, SMS, and WhatsApp using real booking details.
4. What should I do if I used Booking.com?
Monitor messages carefully, avoid unsolicited payment requests, and verify all communication via official channels.
5. Is my password at risk in the Booking.com data breach?
There is no confirmation of password theft, but users should still update passwords as a precaution.
6. How can companies prevent similar breaches?
By implementing Zero Trust architecture, MFA, secure APIs, and continuous threat monitoring.
Conclusion: Lessons from the Booking.com Data Breach
The Booking.com data breach demonstrates how modern cyberattacks increasingly rely on personal and contextual data rather than just financial credentials. Even without direct financial theft, the exposure of travel data creates significant opportunities for phishing, impersonation, and fraud.
For organizations, this incident reinforces the urgency of adopting Zero Trust security models, robust API protection, and continuous threat intelligence monitoring. For users, vigilance and verification remain the strongest defenses.
As cybercriminal tactics continue to evolve, the travel industry must prioritize security as much as convenience.
