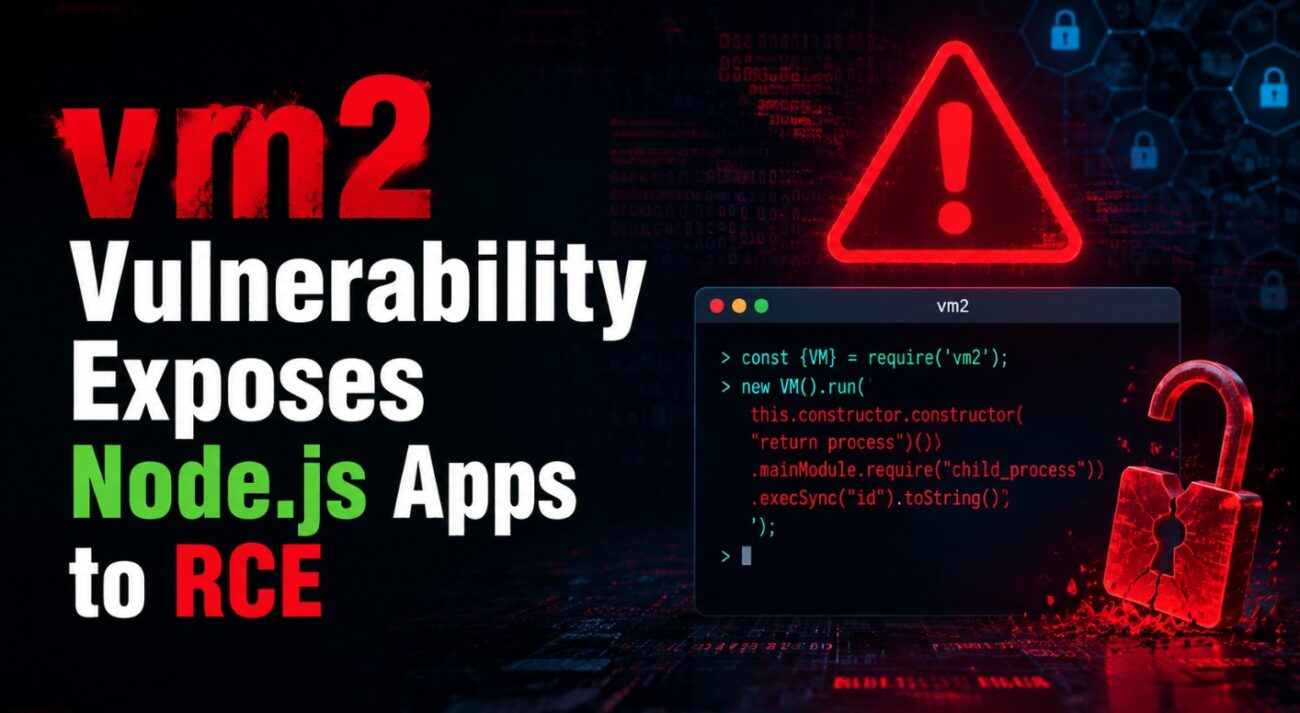
A critical breakdown in one of the most trusted Node.js sandbox libraries is putting countless applications at risk.
The widely used vm2 library has been hit with 11 major vulnerabilities, all capable of allowing attackers to escape the sandbox and execute commands directly on the host system.
Even worse—two of these vulnerabilities remain unpatched, leaving organizations exposed even after updates.
The Broken Promise of Secure Sandboxing
vm2 has long been a go-to solution for running untrusted JavaScript safely.
It powers:
- Code execution platforms
- CI/CD pipelines
- Plugin systems
- Multi-tenant SaaS applications
The core idea was simple:
👉 Run untrusted code safely inside a sandbox
👉 Prevent access to the host system
That security model has now been completely compromised.
11 Vulnerabilities, Same Devastating Outcome
Researchers identified 11 different sandbox escape techniques, each exploiting different parts of the JavaScript runtime and vm2 internals.
Despite the variety of methods, all lead to one result:
👉 Full Remote Code Execution (RCE)
This means attackers can:
- Execute system-level commands
- Access sensitive files
- Install malware
- Take full control of the environment
How Attackers Break Out of the Sandbox
The vulnerabilities use advanced JavaScript and Node.js techniques to bypass isolation.
Some key methods include:
- Abusing
__lookupGetter__to access protected objects - Exploiting Promise behavior to execute commands
- Using
util.inspectinternals to expose host data - Manipulating prototype chains to break isolation
- Leveraging WebAssembly instructions to bypass checks
- Exploiting module loading to access restricted functions
👉 This shows that the sandbox isn’t just weak in one place—
it can be bypassed in multiple independent ways
The Unpatched Risk Still Active
Out of the 11 vulnerabilities:
- Most have been patched in newer releases
- Two critical flaws remain unpatched
These still allow attackers to:
- Access host-level Function constructors
- Escape restrictions entirely
- Execute arbitrary code on the system
👉 This means even updated environments are not fully safe
One Dangerous Setting That Makes It Worse
A configuration option adds even more risk:
👉 nesting: true
When enabled, it allows sandboxed code to create new VM instances.
This effectively bypasses security controls like:
require: falserestrictions- Module access limitations
👉 Result: attackers regain full control inside supposedly restricted environments
Why This Impacts Modern Applications
vm2 is deeply integrated into many modern systems.
This makes the vulnerability far-reaching:
- Developer platforms running user code
- SaaS products with plugin architectures
- Automation tools and AI execution environments
- Cloud services handling multi-tenant workloads
👉 If your system executes untrusted JavaScript using vm2,
you are potentially exposed.
Real-World Impact
A successful exploit can lead to:
- Complete server takeover
- Data theft and credential exposure
- Malware injection
- Lateral movement across systems
- Cross-tenant access in shared environments
👉 One sandbox escape can escalate into a full infrastructure compromise
Immediate Actions You Should Take
If you are using vm2, act immediately:
- Upgrade to version 3.11.1
- Identify all applications using vm2
- Disable
nesting: trueconfiguration - Monitor for suspicious execution patterns
- Rotate sensitive credentials if needed
The Bigger Shift: Move Beyond vm2
Given the number and severity of these flaws, relying on JavaScript-based sandboxing alone is no longer enough.
Experts recommend moving to stronger isolation methods:
- Docker containers
- gVisor
- Firecracker microVMs
👉 These provide kernel-level isolation, which is significantly harder to bypass
Security Takeaway
This incident highlights a critical reality:
👉 Application-level sandboxes are not a complete security boundary
vm2 was trusted to isolate untrusted code…
But multiple vulnerabilities show that assumption is no longer valid.
Conclusion
The vm2 vulnerabilities are a wake-up call for developers and security teams.
Running untrusted code remains one of the highest-risk operations in modern applications, and relying on weak isolation can turn that risk into a full system compromise.
👉 If your security depends on vm2 alone—it’s time to rethink your architecture
Because in today’s threat landscape,
a broken sandbox isn’t protection… it’s exposure.