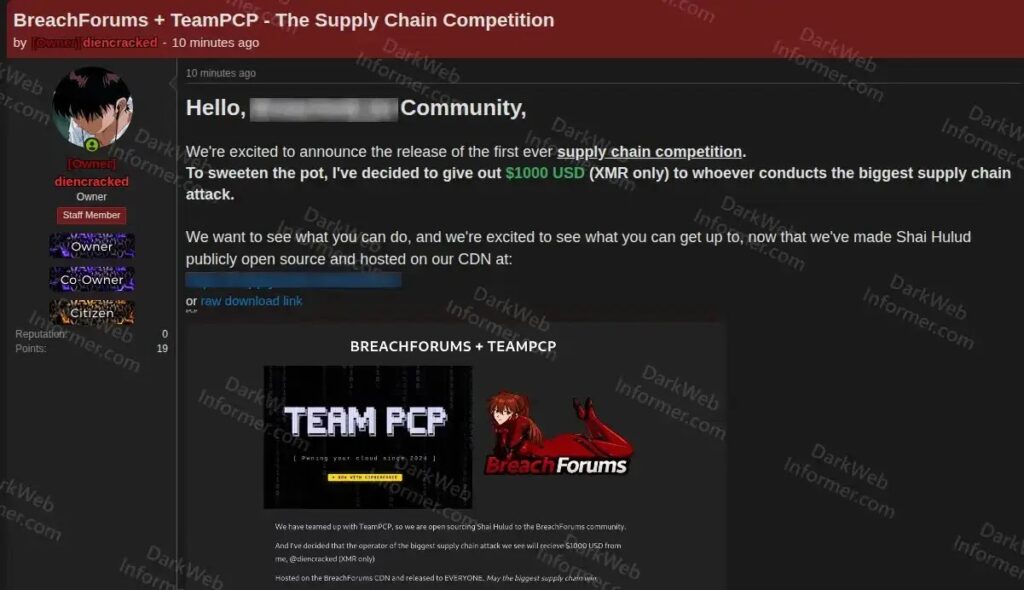
In a disturbing shift for global software security, the cybercrime group TeamPCP and the operators of BreachForums have officially gamified the destruction of software trust. On May 14, 2026, the groups launched a public competition that rewards hackers for successfully compromising open-source packages.
By offering a $1,000 prize in Monero (XMR) and prestigious “reputation points,” the contest incentivizes hackers to poison the very libraries that modern enterprises rely on every day. This isn’t just a quest for a payout; it’s an aggressive recruitment drive designed to flood the ecosystem with malicious code.
The Tool: Shai-Hulud and the Lowered Barrier to Entry
At the center of the competition is an attack tool called “Shai-Hulud.” TeamPCP has released this malware as an open-source resource on BreachForums infrastructure, effectively lowering the skill threshold for supply chain attacks.
- Weaponized Tooling: Features that once required advanced expertise are now “plug-and-play” for script kiddies and lower-tier actors.
- Worm-Like Propagation: The tool is designed for widespread, indiscriminate infection, mirroring the aggressive spread of a digital worm.
- Targeted Platforms: The contest encourages attacks across npm, PyPI, GitHub Actions, Docker images, and OpenVSX extensions.

The Scoring Model: Incentivizing Maximum Impact
The contest’s scoring system is uniquely dangerous because it rewards volume and reach over precision.
- The Popularity Multiplier: Points are awarded based on the weekly and monthly download counts of the compromised package. This pushes attackers to target widely used, “boring” utility libraries that are hidden deep within thousands of enterprise dependency trees.
- Stacking Compromises: Attackers can “stack” multiple smaller compromises. If a hacker can’t hit a “top 10” library, they are encouraged to infect dozens of smaller ones to reach the top of the leaderboard.
Beyond the Prize: The “Secret” Payout
Security analysts warn that the $1,000 reward is merely a distraction. The real value for the participants—and the threat to organizations—lies in what is harvested during the attack:
- CI/CD Secrets: Access to automated build pipelines.
- Cloud Credentials: AWS, Azure, and GCP tokens used by developers.
- Maintainer Tokens: Access to take over even more reputable open-source accounts.
- Enterprise Access: Footholds that can be sold to ransomware groups or initial access brokers (IABs) for tens of thousands of dollars.
Who is at Risk?
Previous campaigns linked to TeamPCP have already impacted AI development, manufacturing, financial services, and government cloud platforms. By attracting a fresh wave of reckless actors, the volume of attacks hitting open-source maintainers is expected to skyrocket.
Action Plan: Protecting Your Pipeline
To defend against this gamified threat, organizations must move beyond “trust” and implement strict verification:
- Pin Your Dependencies: Never use “latest” tags. Use specific versions and verify hashes (subresource integrity).
- Audit Your Lockfiles: Use tools to scan for “typosquatting” or newly suspicious packages that have sudden spikes in activity.
- Secret Management: Ensure that secrets (API keys, SSH keys) are never stored in plain text within your repositories or CI/CD environments.
- Monitor Outbound Traffic: Look for unusual connections from your build servers to unknown external domains, which may indicate a compromised package is “phoning home.”
