Cybercriminals are getting smarter, exploiting trusted platforms and legitimate channels to bypass traditional defenses. A recent campaign targeting macOS users demonstrates this trend, leveraging Claude AI artifacts and Google Ads to deliver the MacSync information stealer, affecting over 15,000 potential victims.
For CISOs, security engineers, and IT managers, this campaign is a stark reminder: even legitimate-looking resources can be weaponized. In this post, we’ll break down how this attack works, analyze its tactics, and provide practical steps for threat detection, mitigation, and compliance.
What is the Claude AI & Google Ads Malware Campaign?
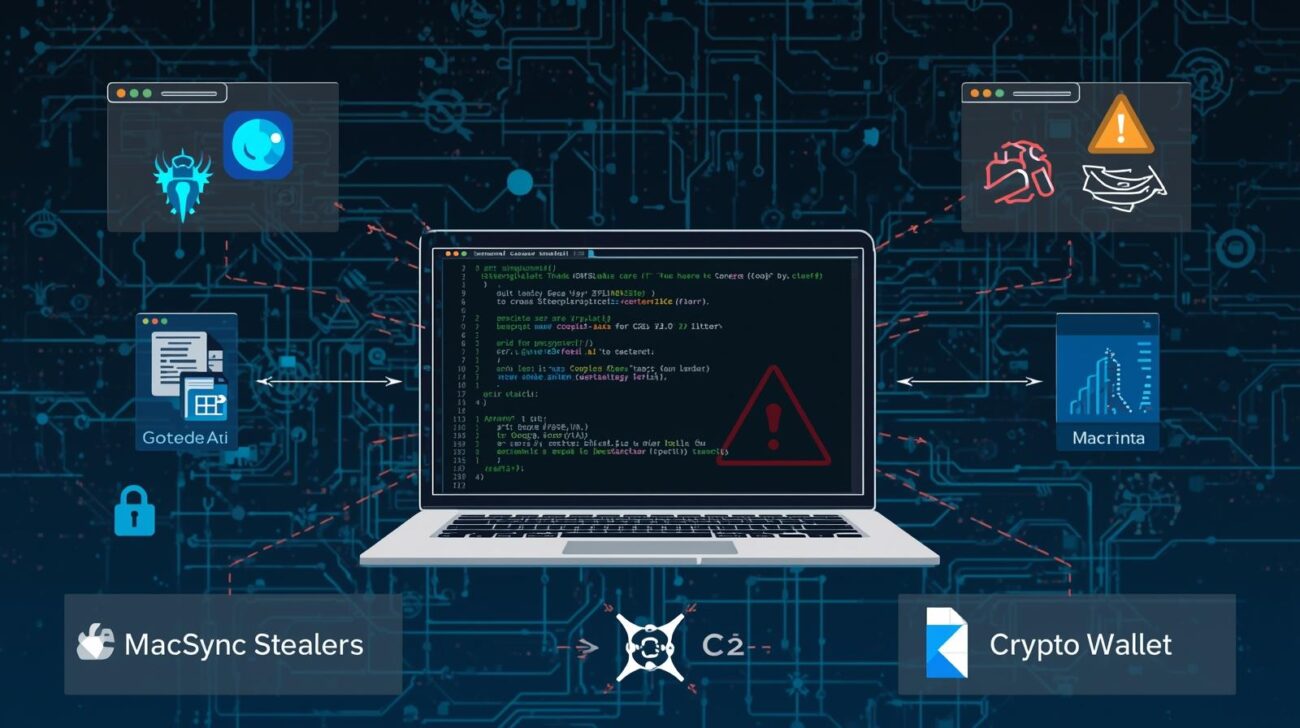
The attack combines social engineering, malware distribution, and platform abuse:
- Claude AI Artifacts: Publicly shared AI-generated content used as a lure.
- Google Ads: Sponsored search results drive traffic to malicious resources.
- MacSync Stealer: A macOS malware that exfiltrates sensitive data like keychain credentials, browser data, and cryptocurrency wallets.
By leveraging trusted platforms, threat actors make their malicious content appear legitimate, increasing the likelihood of execution.
How the Malware Campaign Works
The campaign has two primary variants, each using sophisticated evasion and execution techniques:
Variant 1: Sponsored Google Search for “Online DNS Resolver”
- Attack Vector:
- Users searching for DNS tools encounter a sponsored Google result pointing to a Claude AI artifact titled “macOS Secure Command Execution.”
- Social Engineering:
- The artifact presents itself as a security guide.
- Users are instructed to paste a base64-encoded command into Terminal.
- Malware Execution:
- The command downloads a loader from
/tmp/osalogging.zip. - MacSync establishes communication with its command-and-control server at
a2abotnet[.]com/dynamic. - Uses hardcoded API keys and a spoofed macOS browser User-Agent to evade detection.
- The command downloads a loader from
- Data Exfiltration:
- Data is piped through osascript for extraction.
- Sensitive data is packaged and uploaded via chunked HTTP POST with retries and exponential backoff.
Variant 2: Fraudulent Medium Article for “macOS CLI Disk Space Analyzer”
- Attack Vector:
- Users find a Medium article impersonating Apple Support, hosted at
apple-mac-disk-space.medium[.]com.
- Users find a Medium article impersonating Apple Support, hosted at
- Payload Delivery:
- Similar ClickFix social engineering payload.
- Uses obfuscation techniques, like string concatenation (
cur""l), to bypass basic detection. - Payload hosted at
raxelpak[.]com.
- Evasion:
- Additional layers of obfuscation increase chances of bypassing pattern-matching and antivirus detection.
Real-World Impact & Case Study
According to researchers at Moonlock Lab, over 15,000 macOS users may have interacted with these malicious artifacts. The campaign demonstrates how attackers:
- Exploit trusted platforms (Claude AI, Medium).
- Use paid advertising networks to increase reach.
- Combine social engineering with advanced evasion techniques.
Potential consequences for organizations include:
- Credential theft (keychains, saved passwords)
- Loss of sensitive corporate data
- Exposure of cryptocurrency wallets
- Compliance violations under GDPR or CCPA
Common Mistakes Organizations Make
- Over-reliance on endpoint security: Signature-based antivirus often fails against obfuscated payloads.
- Ignoring public artifact platforms: Employees assume public AI guides are safe.
- Weak threat hunting practices: Organizations may not monitor unusual C2 traffic patterns.
- Limited user awareness: Lack of training on social engineering and phishing tactics.
Best Practices for Mitigation
1. Threat Detection & Monitoring
- Implement real-time C2 traffic monitoring for anomalous endpoints.
- Use sandbox analysis to safely inspect base64-encoded commands.
- Integrate threat intelligence feeds for domains like
a2abotnet[.]comandraxelpak[.]com.
2. Endpoint Security
- Deploy next-gen antivirus and EDR solutions capable of detecting script-based execution.
- Restrict
osascriptusage to trusted scripts. - Enforce least privilege for Terminal execution.
3. Cloud & Platform Security
- Monitor public artifact platforms (Claude AI, GitHub, Medium) for malicious uploads.
- Validate all content sources before execution.
- Enable zero trust policies for device interactions with unverified web content.
4. User Awareness & Training
- Train staff on ClickFix and other social engineering techniques.
- Conduct phishing simulations that mimic sponsored ad campaigns.
- Encourage reporting of suspicious commands or content.
Tools, Frameworks, and Standards
| Framework | Use Case | Relevance |
|---|---|---|
| MITRE ATT&CK | TTP mapping | Identifies techniques like spearphishing via service, obfuscated files |
| NIST CSF | Risk management | Guides detection, response, and mitigation planning |
| ISO 27001 | Security controls | Ensures governance around data protection and incident response |
| EDR Tools | Detection & response | Real-time telemetry and remediation for macOS endpoints |
Expert Insights
- Social Engineering Is Key: Even technical users are susceptible to trusted platform attacks.
- Obfuscation Evades Traditional Defenses: Base64 commands and string concatenation require behavior-based detection.
- Regulatory Impact Matters: Stolen sensitive data could trigger reporting obligations under GDPR, HIPAA, or CCPA.
- Defense in Depth Is Crucial: Combine endpoint protection, network monitoring, and user training to reduce attack surface.
Indicators of Compromise (IOCs)
| Indicator Type | Description |
|---|---|
| Domain | a2abotnet[.]com – C2 server |
| Domain | raxelpak[.]com – Payload hosting |
| Domain | apple-mac-disk-space.medium[.]com – Fake Apple support article |
| File Path | /tmp/osalogging.zip – Staging file |
| Malware | MacSync – Information stealer for macOS |
FAQs
Q1: How does MacSync spread on macOS?
MacSync spreads via social engineering, tricking users into executing malicious Terminal commands from trusted-looking guides or sponsored ads.
Q2: Can traditional antivirus detect this malware?
Basic signature-based antivirus may fail due to obfuscation and dynamic payloads. Behavioral and EDR monitoring is more effective.
Q3: What is ClickFix, and why is it dangerous?
ClickFix is a social engineering technique that convinces users to run commands in their system, often bypassing security checks.
Q4: How can organizations prevent exposure from public AI artifacts?
Implement zero trust policies, validate source content, and train users to avoid executing commands from unverified guides.
Q5: Which frameworks help in responding to these attacks?
MITRE ATT&CK for threat mapping, NIST CSF for risk management, and ISO 27001 for governance and controls.
Conclusion
The Claude AI and Google Ads macOS malware campaign underscores the evolving sophistication of cyberattacks. By abusing trusted platforms and leveraging social engineering, attackers increase their success while evading traditional controls.
Key takeaways:
- Always validate content from AI artifacts, sponsored ads, and third-party articles.
- Implement behavior-based endpoint detection and continuous threat monitoring.
- Train users on social engineering and command execution risks.
- Align mitigation strategies with industry frameworks (MITRE, NIST, ISO).
For organizations aiming to strengthen macOS security posture, proactive monitoring and user education are no longer optional—they’re essential. Download our macOS security assessment guide to evaluate your current defenses and prepare for emerging threats.