Industrial control systems are increasingly exposed to modern attack techniques once limited to traditional IT networks. In this case, selective thread emulation enabled researchers to uncover six high-severity denial-of-service (DoS) vulnerabilities in the Socomec DIRIS M-70 industrial gateway—a device widely deployed in critical infrastructure environments.
For CISOs, SOC analysts, and OT security engineers, this is more than just another vulnerability disclosure. It demonstrates how advanced fuzzing techniques can bypass hardware protections and expose exploitable flaws in industrial IoT (IIoT) firmware.
In this article, you’ll learn:
- How selective thread emulation works
- Why the Socomec DIRIS M-70 vulnerabilities are high risk
- Technical details behind the CVEs
- Real-world operational impact
- Practical mitigation and detection strategies
- Lessons for secure IIoT development and defense
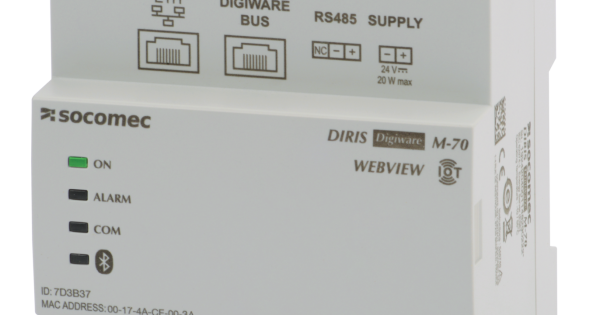
Understanding the Affected Device: Socomec DIRIS M-70


4
The Socomec DIRIS M-70 is an industrial gateway designed for:
- Power monitoring
- Energy management
- Data aggregation across industrial networks
It supports:
- Modbus RTU
- Modbus TCP
- BACnet IP
- SNMP
- RS485 and Ethernet communications
Where It’s Deployed
The M-70 is commonly used in:
- Data centers
- Healthcare facilities
- Manufacturing plants
- Utilities and energy providers
- Critical infrastructure sites
In many environments, this gateway acts as a central communication hub for energy telemetry. A disruption can directly impact operational continuity.
The Breakthrough: What Is Selective Thread Emulation?
Selective thread emulation is a targeted firmware analysis technique that emulates only a specific execution thread rather than an entire embedded system.
Why Full Emulation Is Difficult in OT Devices
Industrial devices often include:
- Proprietary hardware
- Custom peripherals
- MCU-level protections
- Hardware-based debug blocking
In this case, the device’s STM32 microcontroller enforced Code Read-Out Protection (RDP) Level 1, preventing traditional JTAG-based debugging.
When debugger access was detected, flash memory reads were blocked—effectively preventing live analysis.
The Research Approach
Researchers:
- Obtained an unencrypted firmware update file
- Extracted the firmware image
- Identified the Modbus processing thread
- Emulated only that specific thread using the Unicorn Engine
- Integrated coverage-guided fuzzing with AFL
- Transitioned to Qiling for improved debugging and coverage visualization
This dramatically reduced development time compared to full-system emulation.
Key Insight:
Focused emulation of a high-risk protocol handler can uncover exploitable vulnerabilities without modeling the entire hardware stack.
Why the Modbus Thread Was a High-Value Target
The Modbus processing thread supported:
- Over 700 unique message types
- Both Modbus TCP and Modbus RTU over TCP
- Complex parsing logic
Manual inspection of such a large message-handling surface would be impractical.
From a threat modeling perspective, Modbus is:
- Network-exposed
- Widely used in ICS/OT
- Often unauthenticated
- Frequently deployed in flat networks
This made it an ideal candidate for coverage-guided fuzzing.
Vulnerability Details
Six vulnerabilities were identified:
- CVE-2025-54848
- CVE-2025-54849
- CVE-2025-54850
- CVE-2025-54851
- CVE-2025-55221
- CVE-2025-55222
Each vulnerability carries:
- CVSS v3.1 Score: 7.5 (High)
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
Attack Mechanism
An unauthenticated attacker can:
- Send specially crafted Modbus TCP messages
- Trigger improper handling within the Modbus thread
- Cause a denial-of-service condition
- Render the gateway inoperable
This is particularly dangerous in OT environments where:
- Device reboots may require manual intervention
- Redundancy is limited
- Downtime affects physical processes
Risk Impact Analysis
Operational Impact
A compromised gateway could result in:
- Loss of energy monitoring
- Power management failures
- Inaccurate telemetry
- Cascading operational disruptions
In environments such as:
- Data centers → cooling and power anomalies
- Hospitals → equipment instability
- Manufacturing → process downtime
Cyber Risk Context
From a MITRE ATT&CK ICS perspective, this aligns with:
- Denial of Control
- Impair Process Control
- Loss of Availability
Even though the vulnerabilities are “only” DoS, availability is often the most critical pillar in industrial systems.
Real-World Scenario: Data Center Outage
Imagine:
- An attacker gains network access through a misconfigured firewall
- They scan for Modbus TCP services
- Identify exposed M-70 gateways
- Send crafted packets causing repeated crashes
Result:
- Monitoring systems fail
- Power load balancing degrades
- Failover systems misbehave
- Downtime escalates
In high-availability environments, even minutes of disruption can translate into:
- Financial losses
- SLA violations
- Regulatory scrutiny
Common Security Misconceptions in IIoT
1. “It’s Just Monitoring—Not Critical”
Energy monitoring systems are often assumed to be non-critical. In reality, they:
- Feed automation decisions
- Trigger alerts and failover
- Inform load balancing
2. “OT Devices Aren’t Internet-Exposed”
Increasingly false.
Cloud connectivity, remote management, and hybrid IT/OT networks introduce exposure risks.
3. “Firmware Protections Prevent Exploitation”
RDP Level 1 prevented debugging—not exploitation.
Attackers don’t need source code if input validation is weak.
Mitigation and Defensive Measures
1. Immediate Patch Management
Socomec has released firmware version 1.7 or later.
If running 1.6.9:
- Upgrade immediately
- Validate firmware integrity
- Perform change management logging
2. Network Segmentation
Implement:
- Zero trust architecture principles
- OT network isolation
- Strict Modbus access controls
- Firewall ACLs limiting TCP/502 exposure
3. Intrusion Detection
Deploy:
- SNORT rules from Snort.org
- ICS-aware IDS solutions
- Anomaly-based monitoring
4. Logging and Incident Response
Ensure:
- Centralized log aggregation
- SIEM integration
- ICS-specific playbooks
Map detection to NIST CSF functions:
| Function | Action |
|---|---|
| Identify | Asset inventory of OT gateways |
| Protect | Patch & segmentation |
| Detect | IDS rules & anomaly detection |
| Respond | ICS IR plan |
| Recover | Redundant monitoring architecture |
Lessons for Security Engineers and Vendors
For Security Teams
- Prioritize protocol parsing components
- Conduct fuzz testing during procurement validation
- Include IIoT devices in threat modeling exercises
For Vendors
- Integrate secure SDLC practices
- Perform coverage-guided fuzzing pre-release
- Harden protocol parsing logic
- Implement authentication for Modbus TCP
Why Selective Thread Emulation Matters for the Future
This case demonstrates a broader trend:
- Firmware reverse engineering is becoming more accessible
- Coverage-guided fuzzing is increasingly effective
- Hardware protections no longer guarantee security
Selective thread emulation reduces:
- Cost
- Time
- Complexity
While increasing:
- Vulnerability discovery efficiency
- Security research precision
- Risk exposure transparency
Expect this methodology to expand across:
- ICS devices
- Smart grid infrastructure
- Industrial gateways
- Embedded medical devices
Frequently Asked Questions (FAQs)
1. What is selective thread emulation in cybersecurity?
Selective thread emulation is a firmware analysis technique that emulates only a specific execution thread (e.g., a protocol handler) instead of the entire embedded system, improving efficiency in vulnerability discovery.
2. How severe are the DIRIS M-70 vulnerabilities?
Each vulnerability carries a CVSS score of 7.5 (High), allowing unauthenticated remote attackers to cause denial-of-service conditions.
3. Are Modbus TCP systems inherently insecure?
Modbus was not designed with modern security controls. Without network segmentation and access control, Modbus TCP services can be easily abused.
4. What firmware versions are affected?
Firmware version 1.6.9 is affected. Organizations should upgrade to version 1.7 or later.
5. Can these vulnerabilities lead to ransomware attacks?
Directly, they cause denial-of-service. However, availability disruption can be part of a broader ransomware or extortion strategy.
6. How can organizations detect exploitation attempts?
Deploy SNORT signatures, monitor unusual Modbus traffic, and use ICS-aware IDS systems with anomaly detection capabilities.
Conclusion
The discovery of these vulnerabilities highlights a critical shift in industrial cybersecurity: advanced emulation and fuzzing techniques can uncover serious flaws even in hardware-protected environments.
For CISOs and security leaders, the takeaway is clear:
- IIoT devices must be included in enterprise risk management
- Firmware security deserves the same scrutiny as cloud workloads
- Network segmentation and zero trust are no longer optional
If your organization relies on industrial gateways for power monitoring or energy management, now is the time to:
- Review firmware versions
- Audit network exposure
- Validate detection coverage
- Strengthen OT incident response readiness
Proactive OT security is not just about compliance—it’s about operational survival.
