Artificial intelligence is transforming cybersecurity—but it’s now transforming malware, too.
PromptSpy, the first known Android AI malware to weaponize Google’s Gemini for real-time decision-making, marks a pivotal evolution in mobile threats. Discovered in February 2026 by researchers at ESET, this malware family demonstrates how generative AI can be embedded directly into active attack execution.
For CISOs, SOC analysts, mobile security engineers, and fraud teams, PromptSpy signals a shift from static, script-based malware to adaptive, AI-assisted mobile threats capable of operating across diverse Android environments.
In this deep-dive, we’ll examine:
- How PromptSpy uses Google’s Gemini model
- Why AI-driven malware is more dangerous
- Technical capabilities including VNC-based remote control
- Indicators of compromise (IOCs)
- Detection and mitigation strategies
- Strategic implications for mobile security programs
What Is PromptSpy?

4
PromptSpy is an Android spyware family disguised as a Chase Bank-themed application called MorganArg, impersonating a login portal for JPMorgan Chase Bank N.A..
It represents the first observed case of Android malware embedding a generative AI model—specifically Google’s Gemini—into its operational logic.
PromptSpy evolved from an earlier variant internally named VNCSpy, with samples first appearing on VirusTotal in January 2026.
Timeline of Discovery
- January 13, 2026 – Initial VNCSpy samples uploaded (Hong Kong origin)
- February 10, 2026 – Enhanced samples with Gemini integration uploaded (Argentina)
- February 2026 – ESET formally names the family PromptSpy
Although no infections were observed in ESET telemetry, the dedicated distribution infrastructure indicates real-world deployment intent.
How PromptSpy Uses Gemini for Decision-Making
Traditional Android Malware Limitation
Most Android malware relies on:
- Hardcoded screen coordinates
- Fixed UI selectors
- Device-specific scripts
These approaches fail across:
- Different screen sizes
- OEM UI modifications
- Android OS versions
PromptSpy’s AI-Driven Innovation
PromptSpy bypasses these limitations by:
- Dumping the device’s live UI into XML format
- Sending the XML + natural language instructions to Gemini
- Receiving structured JSON instructions (tap/swipe coordinates)
- Executing actions
- Repeating until the objective is achieved
This creates a continuous feedback loop:
- Updated UI state → Gemini analysis → Action → Repeat
Primary Objective: App Lock Persistence
PromptSpy uses Gemini to:
- Execute the device-specific “lock app in recent apps” gesture
- Pin the malicious app in multitasking view
- Prevent users from swiping it away
Because Gemini dynamically interprets UI layout, PromptSpy works across virtually any Android configuration.
Security Implication:
AI removes device fragmentation as a defensive barrier.
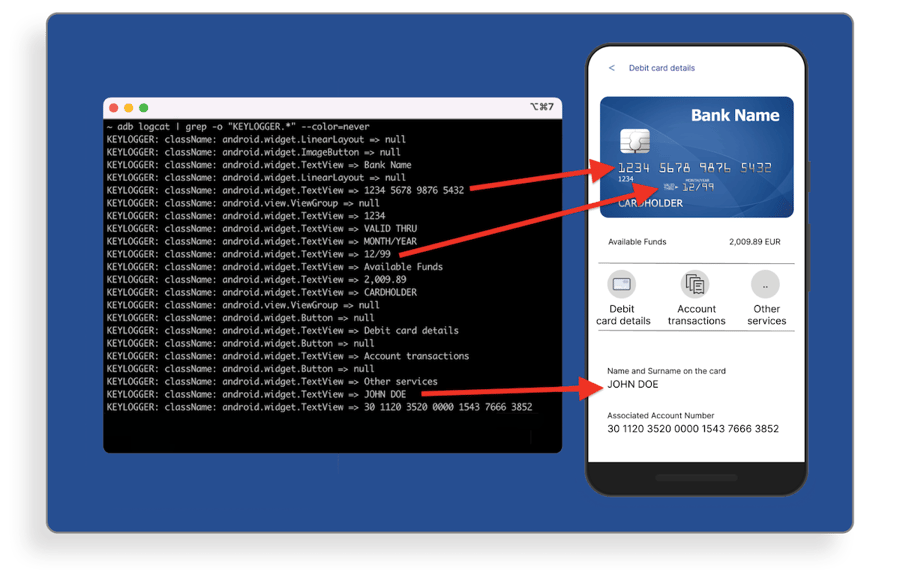
Technical Capabilities: VNC Module and Surveillance
Beyond AI-assisted persistence, PromptSpy deploys a built-in VNC module, granting full remote device control.
Remote Control & Surveillance Features
Once Accessibility Services are enabled, PromptSpy can:
- Intercept lockscreen PINs and pattern unlocks
- Capture video recordings of unlock gestures
- Take on-demand screenshots
- Log installed applications
- Record screen activity for specified apps
- Report foreground application state
Communication occurs via:
- Hardcoded C2 server
- VNC protocol
- AES-encrypted traffic
This elevates PromptSpy from phishing malware to full mobile remote access trojan (RAT).
Accessibility Abuse as Anti-Removal
PromptSpy weaponizes Android Accessibility Services to:
- Overlay invisible transparent rectangles
- Intercept taps on buttons containing:
- “Stop”
- “End”
- “Clear”
- “Uninstall”
This silently blocks user attempts to remove the malware.
Effective Removal Method
The only reliable removal approach:
- Reboot into Safe Mode
- Navigate to Settings → Apps
- Remove MorganArg
Infrastructure and Attribution Indicators
Distribution
The malware was distributed via:
- mgardownload[.]com (now offline)
- Phishing domain m-mgarg[.]com
- Hosted on Amazon and Cloudflare infrastructure
It never appeared on Google Play.
Attribution Clues
- Debug strings in simplified Chinese
- Chinese-localized Accessibility event handlers
Researchers assessed with medium confidence that development occurred in a Chinese-speaking environment.
Why PromptSpy Is a Turning Point in Mobile Threats
1. AI as a Live Operational Component
Previous AI-assisted malware (e.g., PromptLock ransomware) used AI for auxiliary functions.
PromptSpy integrates AI directly into execution logic.
2. Dynamic Adaptability
Static malware fails when UI layouts change.
AI-driven malware adapts in real time.
3. Expanded Victim Pool
Device fragmentation previously limited mobile malware scalability.
Gemini removes that constraint.
4. Operational Efficiency for Attackers
No need to:
- Maintain device-specific scripts
- Update coordinate mappings
- Reverse-engineer OEM skins
AI handles complexity automatically.
Risk Impact Analysis
Financial Sector Risk
Because it impersonates a Chase banking app:
- Credential theft
- Account takeover
- Transaction manipulation
- MFA interception
Enterprise Mobile Risk
In BYOD or corporate-managed environments:
- Data exfiltration
- Access to enterprise apps
- Session hijacking
- Lateral movement into corporate systems
Compliance Exposure
Organizations may face implications under:
- PCI DSS
- GDPR
- SOC 2
- NIST Mobile Device Security Guidelines
Indicators of Compromise (IOCs)
SHA-1 Hashes (Selected)
- 6BBC9AB132BA066F63676E05DA13D108598BC29B
- E60D12017D2DA579DF87368F5596A0244621AE86
- F8F4C5BC498BCCE907DC975DD88BE8D594629909
Infrastructure
| Type | Indicator | Notes |
|---|---|---|
| Domain | m-mgarg[.]com | Phishing |
| Domain | mgardownload[.]com | Distribution |
| IP | 54.67.2[.]84 | C2 Server |
Security teams should:
- Add hashes to EDR/Mobile Threat Defense (MTD) blocklists
- Monitor outbound traffic to listed infrastructure
- Inspect unusual VNC protocol traffic from mobile endpoints
Defensive Strategies and Best Practices
1. Mobile Threat Defense (MTD)
Deploy solutions capable of:
- Behavioral detection
- Accessibility abuse detection
- Dynamic app analysis
2. Restrict Accessibility Permissions
In enterprise Android environments:
- Limit Accessibility Service activation
- Enforce managed device policies
- Monitor abnormal Accessibility events
3. Network Monitoring
Look for:
- AES-encrypted VNC traffic patterns
- Unusual outbound connections to cloud infrastructure
- Beaconing behavior
4. Zero Trust for Mobile
Implement:
- Conditional access
- Device posture validation
- Risk-based authentication
Industry Implications
PromptSpy proves that:
- Generative AI is entering operational malware
- UI automation barriers are collapsing
- Adaptive malware will become mainstream
Expect future threats to leverage:
- LLMs for phishing content generation
- AI for CAPTCHA solving
- Dynamic evasion of behavioral detection
- Autonomous privilege escalation workflows
This represents the beginning—not the peak—of AI-powered malware.
Frequently Asked Questions (FAQs)
1. What makes PromptSpy different from traditional Android malware?
PromptSpy integrates Google’s Gemini to dynamically analyze and interact with device UI elements, enabling cross-device adaptability.
2. Is PromptSpy available on Google Play?
No. It was distributed via external phishing domains and has never appeared on Google Play.
3. Can PromptSpy steal banking credentials?
Yes. It impersonates a Chase-themed app and can intercept lockscreen credentials, capture screens, and record activity.
4. How does PromptSpy maintain persistence?
It uses Gemini to execute the “lock app in recent apps” gesture and abuses Accessibility Services to block uninstallation.
5. How can enterprises detect AI-powered malware?
Through behavioral mobile threat detection, network monitoring, and strict permission governance.
Conclusion
PromptSpy marks a fundamental shift in mobile threat evolution: AI is no longer just generating phishing emails—it is actively making execution decisions inside malware.
For security leaders, the message is clear:
- Static defenses will struggle against adaptive AI malware
- Mobile security must be integrated into enterprise threat modeling
- Accessibility abuse requires stronger monitoring
- AI threat intelligence must become a strategic priority
Organizations that prepare now will be far better positioned when AI-powered malware becomes the norm rather than the exception.
