Job seekers are the latest target of sophisticated phishing campaigns. Attackers are using fake Google Forms websites to harvest Google login credentials, exploiting trust in legitimate services.
This campaign highlights how threat actors leverage domain impersonation and realistic user interfaces to trick victims into handing over sensitive information. For CISOs, IT managers, and security professionals, understanding these tactics is critical for preventing credential theft and protecting organizational accounts.
In this article, you’ll learn:
- How attackers mimic Google Forms
- Technical infrastructure behind the campaign
- Risk implications for individuals and enterprises
- Indicators of compromise (IOCs)
- Mitigation strategies and best practices
How the Phishing Campaign Works
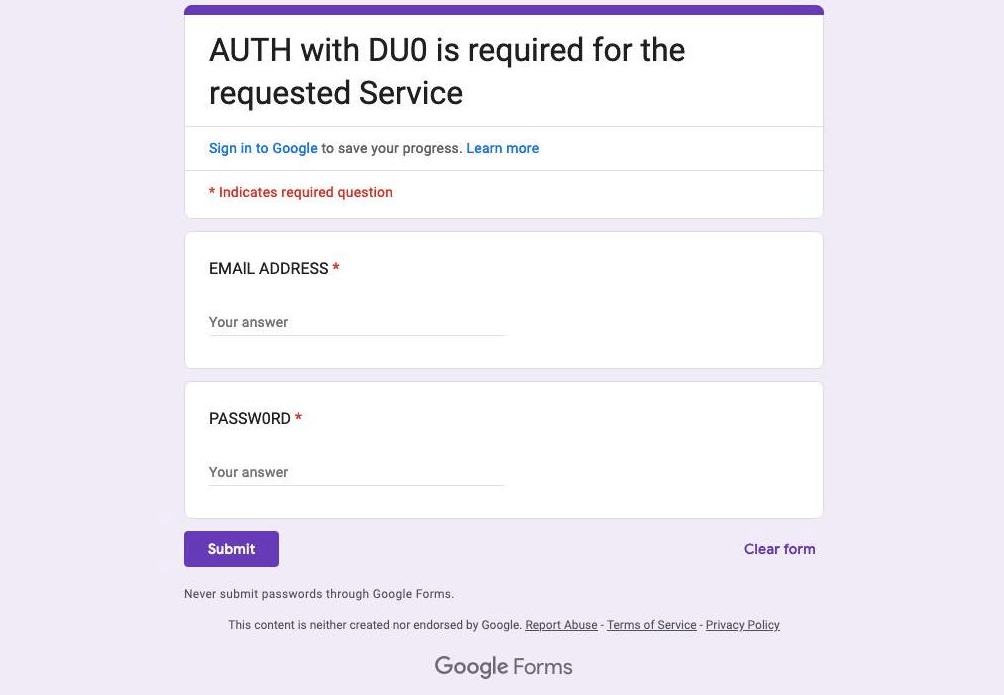
The phishing campaign primarily targets job seekers, using convincing fake job applications to trick victims into revealing Google credentials.
Domain Impersonation
- Attackers registered the domain forms.google.ss-o[.]com, designed to appear like the legitimate forms.google.com
- The “ss-o” substring mimics single sign-on (SSO) authentication terminology, lending credibility to the fake site
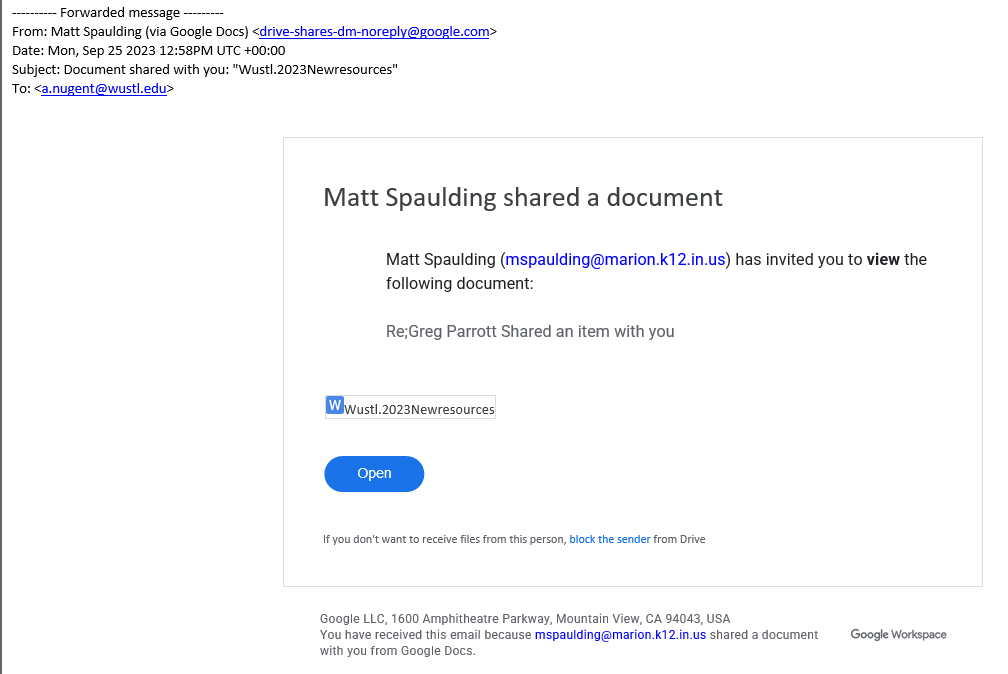
Lure Tactics
- Emails or LinkedIn messages advertise positions such as Customer Support Executive
- Victims are prompted to provide personal information: name, email, and job application responses
- The fake form uses authentic Google Forms elements: logos, color schemes, and disclaimers
Technical Infrastructure Behind the Attack
Malwarebytes researchers uncovered sophisticated mechanisms that enhance operational stealth:
- generation_form.php script generates personalized URLs for each victim
- Unique links allow tracking of individual targets
- Sign-in attempts redirect to id-v4[.]com/generation.php, a domain used in phishing campaigns for nearly a year
- Anti-analysis mechanisms redirect suspicious visitors (like researchers) to legitimate Google search pages
These tactics make the attack resilient against automated detection and security research.
Risk and Impact Analysis
Individual Risks
- Credential theft leading to account compromise
- Unauthorized access to personal emails, Drive files, and other Google services
- Potential for further phishing or identity theft
Enterprise Risks
- Compromised employee accounts may allow lateral movement into corporate resources
- Credential reuse can expose sensitive internal data
- Social engineering campaigns can exploit stolen information
Even a single compromised account could have cascading effects in corporate environments, especially if credentials are linked to business tools.
Indicators of Compromise (IOCs)
| Domain | Status | Notes |
|---|---|---|
| forms.google.ss-o[.]com | Active | Fake Google Forms phishing site |
| id-v4[.]com | Taken down | Credential harvesting endpoint |
Detection Tip: Monitor unusual login attempts, alert on suspicious domains, and enforce logging for third-party authentication events.
Prevention and Mitigation Strategies
1. End-User Awareness
- Never click links in unsolicited job offers or emails
- Verify job postings through official company channels
- Look carefully at URLs for subtle impersonation cues
2. Technical Protections
- Use password managers; they will not autofill credentials on fraudulent websites
- Enable multi-factor authentication (MFA) on Google accounts
- Deploy real-time anti-malware and web filtering solutions
- Monitor for suspicious outbound connections or credential misuse
3. Organizational Policies
- Educate employees on phishing awareness
- Implement URL and domain monitoring for impersonation attempts
- Enforce corporate MFA and single sign-on (SSO) security best practices
Conclusion
The fake Google Forms phishing campaign underscores the continuing evolution of social engineering attacks. By combining realistic UI design, domain impersonation, and personalized tracking, threat actors can target job seekers and employees with high precision.
For security teams, vigilance is key: educate users, monitor domains, enforce MFA, and use password managers. Even simple measures can prevent credential theft and mitigate potential enterprise risks.
Cyber hygiene and awareness remain the strongest defense against increasingly sophisticated phishing threats.
