The latest FinCEN analysis reveals a staggering reality: ransomware payments reported under the Bank Secrecy Act (BSA) have surpassed $4.5 billion by 2024, signaling an escalating cybercrime crisis.
Record-Breaking Year for Ransomware
From January 2022 to February 2025, organizations filed 4,194 ransomware-related reports, totaling $2.1 billion in payments. Compare that to 2013–2021, which saw 3,075 reports and $2.4 billion in losses.
The peak? 2023, with:
- 1,512 incidents
- $1.1 billion paid (a 77% jump from 2022)
In 2024, incidents dipped slightly to 1,476, with payments dropping to $734 million—but the threat remains severe.
Median Payments & Targeted Sectors
Median ransomware payments shifted:
- 2022: $124,097
- 2023: $175,000
- 2024: $155,257
Most payments stayed under $250,000, but the cumulative impact is massive. Financial services, manufacturing, and healthcare bore the brunt of attacks.
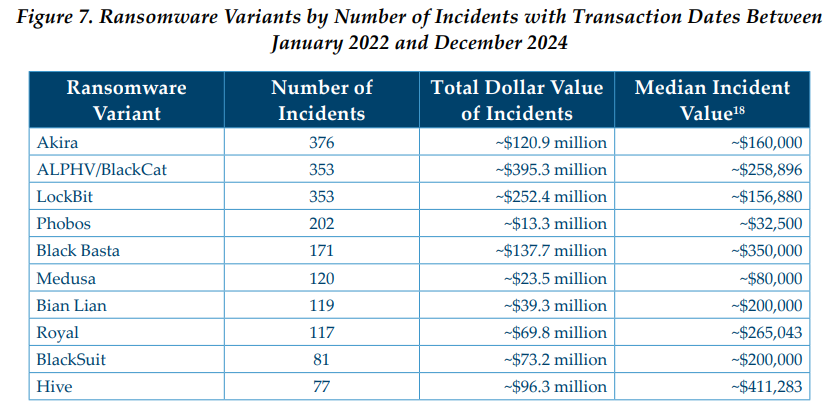
Top Ransomware Variants
FinCEN identified 267 ransomware strains, with these leading the pack:
- Akira – Highest number of incidents (376)
- ALPHV/BlackCat – Largest total payout ($395.3M)
Other major players: LockBit, Phobos, Black Basta.
How Attackers Operate
- Communication Channels:
- TOR (67%)
- Email (28%)
- Payment Methods:
- Bitcoin dominates (97%)
- Money Laundering:
- Unhosted crypto wallets
- Convertible Virtual Currency (CVC) exchanges
Cybersecurity Implications
FinCEN warns:
“Ransomware is a complex cybersecurity problem requiring preventive, protective, and preparatory best practices.”
Resources like CISA’s StopRansomware.gov offer alerts, guides, and training to help organizations reduce risk.
Key Takeaways
- Ransomware payments exceeded $4.5B by 2024
- 2023 was the worst year on record: $1.1B paid
- Akira and ALPHV/BlackCat dominate the threat landscape
- Bitcoin remains the primary payment channel
- Critical sectors like finance and healthcare are prime targets
