The latest Booking.com phishing campaign is a stark reminder that attackers don’t just target individuals—they weaponize trusted global brands to scale financial fraud.
In early 2026, researchers observed a renewed, financially motivated operation targeting hotel partners and guests in a sophisticated multi-stage attack chain. What begins as a seemingly harmless “complaint” email sent to hotel staff can quickly escalate into:
- Credential theft
- Partner account takeover
- Guest payment fraud
- Card data exposure
For CISOs, SOC teams, IT managers, and hospitality operators, this campaign highlights a critical risk: supply chain phishing combined with social engineering and payment fraud.
In this article, you’ll learn:
- How the multi-stage phishing chain works
- The technical tactics used (IDN homographs, phishing kits, CAPTCHA gating)
- Risk impact analysis for hotels and customers
- Defensive best practices aligned with NIST and Zero Trust principles
- How to detect and stop similar attacks early
What Is the Booking.com Phishing Campaign?
The Booking.com phishing campaign is a coordinated, multi-stage financial fraud scheme targeting:
- Hotel partners (first-stage victims)
- Customers/guests (second-stage victims)
Unlike simple phishing emails that attempt to steal credentials immediately, this operation uses:
- Look-alike domains
- IDN homograph attacks
- Redirect chains
- Tokenized URLs
- Cloudflare CAPTCHA gating
- Defense evasion mechanisms
The goal is clear: monetize trust in the Booking.com ecosystem.
How the Multi-Stage Fraud Chain Works
Stage 1: Phishing Email to Hotel Staff


4
Attackers begin by targeting:
- Reservation mailboxes
- Support inboxes
- Front-desk administrative emails
The lure typically references:
- A guest complaint
- Room availability issue
- Booking modification request
The email contains a link that appears legitimate in the message body but redirects to an attacker-controlled infrastructure.
Common URL characteristics include:
complaint?optoken=
This tokenized structure increases legitimacy and bypasses simple URL filtering.
Stage 2: Look-Alike Domains and IDN Homograph Attacks
The campaign leverages IDN homograph techniques, where a Cyrillic character is substituted into the word “booking,” creating a domain visually indistinguishable from the real one.
Example techniques:
- “bookіng” (Cyrillic character swap)
- “bookling” subdomains
- Newly registered domains mimicking brand infrastructure
Once on the phishing portal, victims are prompted to log in.
Credentials are harvested and used to access legitimate Booking.com partner accounts.
Stage 3: Defense Evasion & Infrastructure Fingerprinting


4
One of the most sophisticated elements of this operation is visitor fingerprinting.
The phishing kit:
- Analyzes browser headers
- Detects security tools or sandbox environments
- Blocks security researchers
- Displays benign decoy “hotel cleaning” websites when checks fail
This evasion tactic complicates detection by automated scanners and threat intelligence platforms.
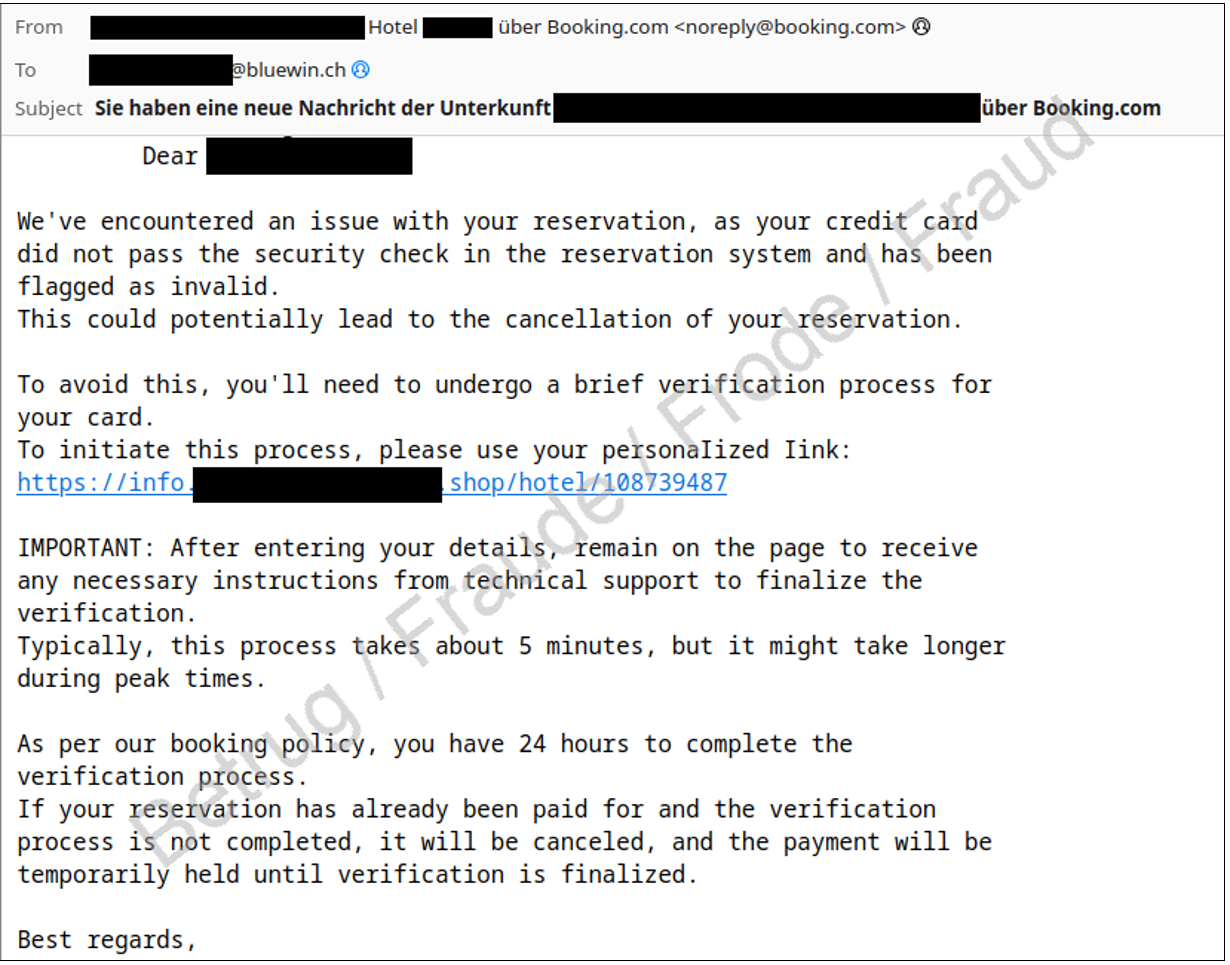
Stage 4: Guest Targeting via WhatsApp


4
After gaining access to hotel partner accounts, attackers pivot to guests.
Using stolen booking data, they send highly convincing WhatsApp messages that include:
- Accurate reservation details
- Urgent payment requests
- Cancellation threats
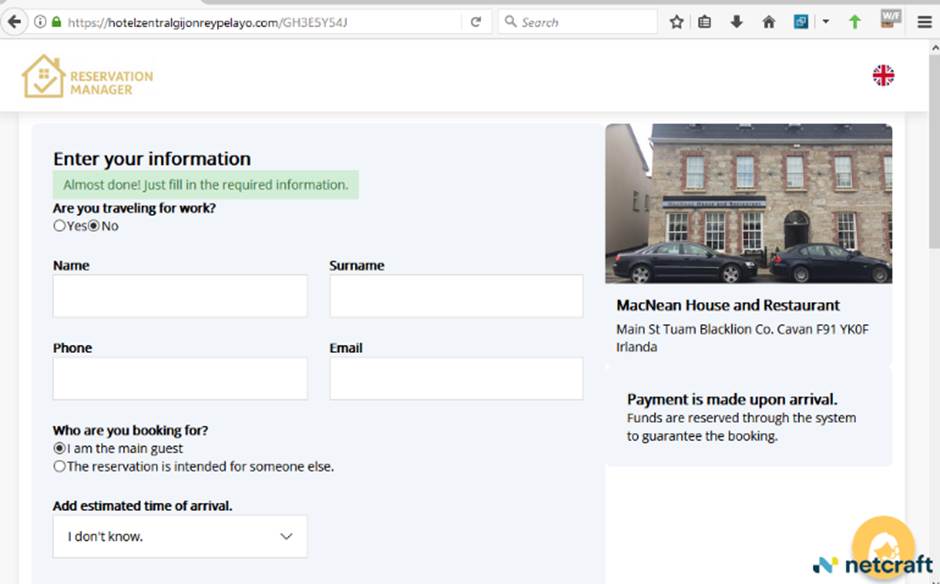
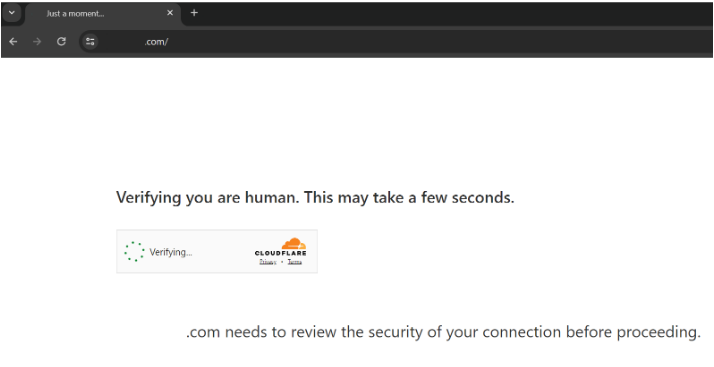
Victims are routed through:
- A Cloudflare CAPTCHA page (adds legitimacy)
- A Booking.com look-alike payment portal
At this point, payment fraud and card harvesting occur.
Why This Campaign Is So Effective
1. Supply Chain Trust Exploitation
Guests trust communications from hotels. Hotels trust communications from Booking.com.
Attackers exploit both.
2. Multi-Stage Social Engineering
Rather than attacking guests directly, adversaries compromise:
- Lower-security partner accounts
- Operational email inboxes
- Staff with limited security awareness
3. Defense Evasion
Fingerprinting and decoy content reduce exposure to:
- Automated crawlers
- Email security scanners
- Sandbox analysis
4. Use of Real Booking Data
This dramatically increases credibility and bypasses common phishing red flags.
Risk & Business Impact Analysis
| Impact Area | Risk Level | Description |
|---|---|---|
| Financial Loss | High | Direct payment fraud & chargebacks |
| Brand Reputation | High | Loss of customer trust |
| Compliance Exposure | Medium-High | PCI DSS implications if card data exposed |
| Operational Disruption | Medium | Account recovery & incident response workload |
For hospitality organizations, this is not just a phishing issue—it’s a third-party ecosystem security risk.
Common Mistakes Organizations Make
- ❌ No MFA on partner portals
- ❌ Shared inbox credentials
- ❌ No login anomaly detection
- ❌ Ignoring look-alike domain monitoring
- ❌ No staff phishing simulations
These gaps allow attackers to move laterally from inbox compromise to account takeover.
Defensive Best Practices (Aligned with NIST & Zero Trust)
1. Enforce Multi-Factor Authentication (MFA)
Mandatory MFA on all Booking.com partner accounts.
Prefer:
- Phishing-resistant MFA (FIDO2, hardware tokens)
2. Restrict Portal Access
- IP allowlisting where possible
- Conditional access policies
- Geo-velocity detection
3. Implement Advanced Email Security
- DMARC, DKIM, SPF enforcement
- Look-alike domain monitoring
- URL rewriting & sandboxing
- Blocking IDN homograph domains
4. Strengthen Logging & Monitoring
Monitor for:
- New sign-ins
- Password resets
- Account permission changes
- Unusual outbound redirects
- Guest message anomalies
Integrate alerts into your SIEM and map activity against MITRE ATT&CK tactics such as:
- Credential Access
- Initial Access (Phishing)
- Defense Evasion
- Collection
5. Guest Protection Controls
Hotels should:
- Prohibit payment collection via chat apps
- Use only verified in-platform payment methods
- Communicate security policy clearly in confirmation emails
What Customers Should Do
If you receive a payment link via WhatsApp:
- Do not click it
- Verify through the official Booking.com app
- Call the hotel using verified contact details
If you entered details:
- Change passwords immediately
- Contact your bank
- Monitor transactions
- Ask the hotel to confirm whether their partner account was accessed
FAQs
1. What is the Booking.com phishing campaign?
A multi-stage financial fraud scheme targeting hotel partners first, then guests using stolen booking data.
2. How does the attack begin?
With phishing emails sent to hotel reservation or support inboxes disguised as guest complaints.
3. What is an IDN homograph attack?
It uses visually similar Unicode characters to create domains that look identical to legitimate ones.
4. Why is this campaign more dangerous than normal phishing?
Because attackers use legitimate booking data, making scams highly convincing and harder to detect.
5. How can hotels prevent account takeover?
By enforcing MFA, restricting portal access, monitoring login anomalies, and blocking look-alike domains.
6. Can customers recover stolen money?
In many cases yes—if reported quickly to the bank and hotel. Prompt action is critical.
Conclusion
The Booking.com phishing campaign demonstrates how modern threat actors blend:
- Brand impersonation
- Credential harvesting
- Account takeover
- Payment fraud
- Defense evasion
For security leaders, this is a reminder that ecosystem security is business security.
Hotels must strengthen identity controls, monitoring, and staff awareness. Customers must verify payment requests through official channels.
If your organization depends on third-party platforms for revenue, now is the time to:
- Assess partner portal security
- Enforce phishing-resistant MFA
- Review logging and detection coverage
- Conduct targeted phishing simulations
Trust is a revenue asset. Protect it accordingly.
