A new Linux botnet campaign, dubbed SSHStalker, has been uncovered exploiting weak SSH credentials to compromise servers at scale. Unlike stealthy modern malware, this operation prioritizes automation, uptime, and repeatability, reviving the IRC-controlled botnet model for modern Linux environments.
Organizations running exposed SSH servers are at risk of having systems enrolled into this botnet, which can then scan, infect, and persist across networks, making mitigation challenging.
In this article, we explore SSHStalker’s attack methodology, persistence mechanisms, and actionable defense strategies for system administrators and security teams.
SSHStalker Overview
- Type: Linux IRC botnet
- Target: SSH servers with weak or reused credentials
- Primary Goal: Compromise Linux hosts to create a botnet at scale
- Automation Tools: Golang binaries, C and Perl IRC bots, GCC compilation pipelines
- Persistence: Cron jobs, watchdog scripts, redundant servers
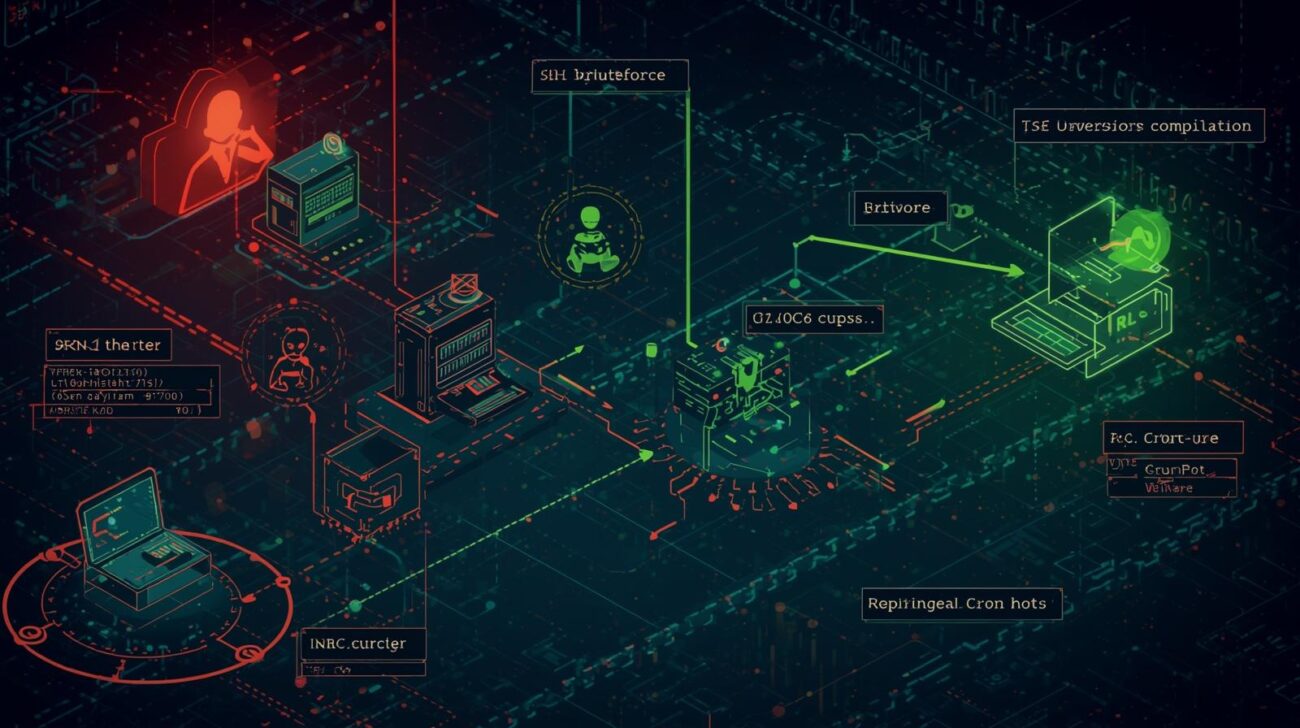
SSHStalker operates in a scale-first approach, prioritizing speed, uptime, and low cost over stealth. In early 2026, honeypot analysis revealed attackers using a Golang binary called “nmap” to probe SSH (port 22) for potential targets.
Attack Flow and Infection Pipeline
- SSH Credential Guessing – The botnet scans for servers with weak or reused passwords.
- Automated Deployment – Once a host is compromised, a layered payload is deployed:
- Golang binaries probe for new targets
- GCC compiles small C helper files
- Archives like
GSandbootbou.tgzunpack IRC bots and supporting tools
- IRC Bot Enrollment – Infected hosts join control channels using C and Perl IRC bot variants.
- Dormant Persistence – Hosts remain enrolled in control channels even with minimal operator activity.
- System Cleaning – Log cleaners remove shell history (
.bash_history) andutmp/wtmp/lastlogentries. - Legacy Exploits – Some attacks leverage older Linux 2.6.x vulnerabilities for forgotten systems.
Persistence Mechanisms
SSHStalker employs blunt but highly effective persistence strategies:
- Adds a cron job executing every minute to restart the bot if terminated
- Stores its working directory and maintains a watchdog process
- Quickly restores control within ~60 seconds if the main process is killed
Implication for defenders: Partial cleanup is ineffective; all components must be removed to prevent reinfection.
Indicators of Compromise (IoCs)
- Cron jobs running suspicious scripts every minute
- Bot directories often found in
/dev/shm - Unexpected GCC or
makeruns in/tmp,/dev/shm, or user directories - New binaries executing shortly after compilation
- IRC client registrations or unexpected channel joins
- Long-lived outbound TCP sessions to unknown IRC servers
Defensive Strategies
SSH Hardening
- Disable password authentication → enforce key-based SSH access
- Rate-limit login attempts → prevent brute-force scans
- Restrict SSH exposure → only allow trusted IPs to connect
Host-Level Monitoring
- Alert on unexpected GCC or
makeexecutions - Scan for cron jobs that run unknown scripts
- Monitor directories like
/dev/shmand/tmpfor suspicious binaries
Network-Level Controls
- Egress filtering → block servers from maintaining long-lived TCP connections to unknown IRC infrastructure
- Detect IRC client registration patterns and channel activity
Incident Response
- Remove one-minute cron entries
- Delete the full botnet kit directory
- Hunt for additional services or init scripts deployed by helper tools
Expert Insights
- Scale-first, not stealthy: SSHStalker demonstrates that botnets can remain highly effective even without stealth.
- Automation amplifies impact: The use of automated SSH scans, compilation pipelines, and IRC control channels allows rapid growth.
- Persistent threats: Blunt persistence mechanisms like cron-based watchdogs require complete eradication during remediation.
- Legacy vulnerabilities matter: Old Linux 2.6.x exploits can still affect forgotten hosts in cloud and enterprise environments.
FAQs
Q1: What is SSHStalker?
SSHStalker is a Linux IRC botnet that compromises SSH servers at scale, using automated credential guessing, IRC command-and-control, and persistent watchdog mechanisms.
Q2: How does it persist on infected hosts?
It installs a one-minute cron job, stores its working directory, and uses watchdog scripts to automatically restart processes.
Q3: What should organizations do to protect against SSHStalker?
- Disable password-based SSH authentication
- Use key-based access only
- Restrict SSH to trusted networks
- Monitor for unexpected compilation or cron activity
- Filter IRC traffic at the network edge
Q4: Which hosts are most vulnerable?
Any Linux host with exposed SSH ports, weak credentials, or outdated systems (including older 2.6.x kernels) is at risk.
Conclusion
The SSHStalker botnet highlights how legacy IRC control mechanisms combined with automation can still pose a significant threat to Linux infrastructure.
Key Takeaways:
- Enforce SSH best practices and key-based authentication
- Monitor for unusual GCC, make, and cron activity
- Implement network egress filtering for IRC connections
- Remove all components during incident response to prevent reinfection
By combining host-level monitoring, network defenses, and proper SSH hardening, organizations can mitigate the threat of SSHStalker and other automated botnet campaigns.