Microsoft is strengthening Windows kernel security by removing trust for legacy cross-signed kernel drivers. Starting with the April 2026 update, Windows 11 and Windows Server 2025 will block these drivers by default. 
This change ensures only drivers certified through the Windows Hardware Compatibility Program can automatically load, significantly reducing kernel-level attack risks.
Closing a Long-Standing Security Gap
The cross-signed root program was introduced in the early 2000s to allow third-party certificate authorities to issue trusted code-signing certificates for drivers.
However, the program created several security weaknesses:
- No verification of driver security
- Developers controlled private keys
- Certificates frequently targeted by attackers
- Rootkits loaded using stolen credentials
Because of these risks, Microsoft deprecated the program in 2021.
Why This Matters
Even after deprecation, Windows continued trusting these legacy certificates to maintain compatibility with older hardware.
This left systems vulnerable to:
- Kernel-level malware
- Rootkit deployment
- Privilege escalation attacks
- Driver-based persistence
The April 2026 update removes this lingering trust.
New Driver Trust Model
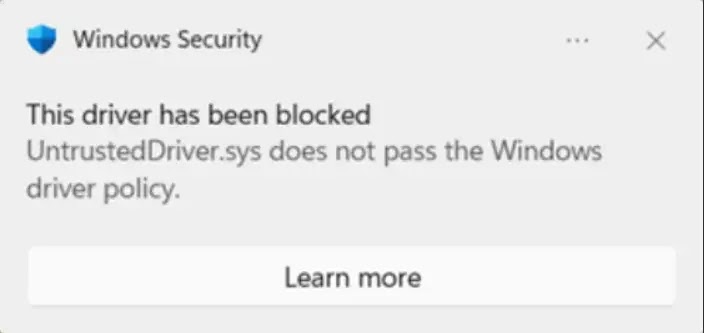
Under the new policy, only drivers that:
- Pass Microsoft identity verification
- Undergo compatibility testing
- Complete malware scanning
- Receive Microsoft-signed certificates
will be allowed to load automatically.
This greatly reduces the kernel attack surface.
Safe Rollout Strategy
Microsoft is implementing the change in phases to avoid system instability.
The rollout includes:
- Evaluation mode monitoring
- Driver load auditing
- Runtime threshold checks
- Restart-based enforcement
If unsupported drivers are detected, enforcement is delayed to prevent disruption.
Allow List for Critical Drivers
To maintain compatibility, Microsoft is introducing an allow list for:
- Widely used legacy drivers
- Trusted vendor drivers
- Critical hardware components
This prevents essential systems from breaking.
Enterprise Environment Considerations
Organizations using custom kernel drivers are not left without options.
Enterprises can:
- Use Application Control for Business policies
- Sign policies with UEFI Secure Boot authority
- Explicitly trust internal drivers
This ensures legitimate operations continue securely.
Security Benefits
Blocking cross-signed drivers helps prevent:
- Rootkit installation
- Kernel privilege escalation
- Driver-based malware persistence
- Unauthorized kernel access
Kernel-level attacks are among the most dangerous threats, making this change significant.
What Administrators Should Do
IT teams should:
- Audit existing kernel drivers
- Identify legacy cross-signed drivers
- Update hardware vendor drivers
- Test enterprise applications
- Prepare Application Control policies
Key Takeaways
- Windows will block cross-signed drivers by default
- Change begins April 2026
- Applies to Windows 11 and Server 2025
- Legacy rootkit attack vector removed
- Enterprises can allow trusted custom drivers
Conclusion
Microsoft’s decision to block untrusted cross-signed kernel drivers marks a major step in strengthening Windows kernel security. By enforcing modern driver signing requirements, the company is closing a long-standing attack vector used by rootkits and advanced malware. Organizations should review their driver dependencies and prepare for enforcement to ensure a smooth transition.