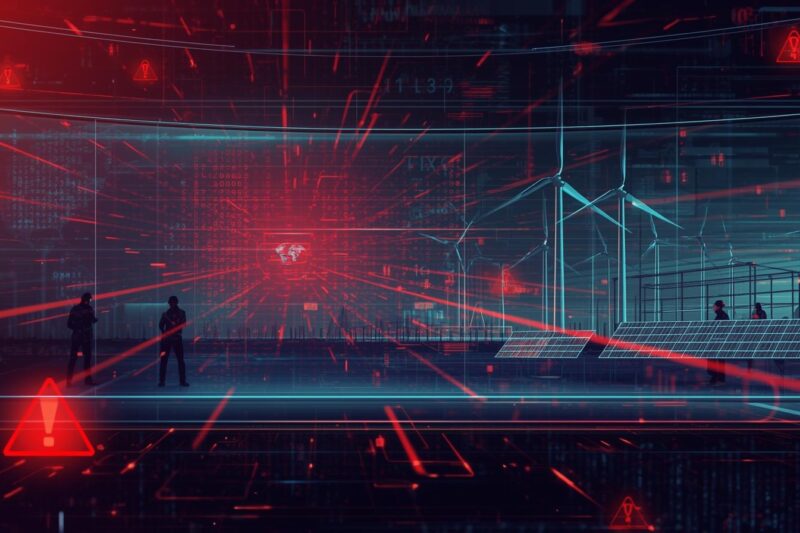
On December 29, 2025, coordinated cyber attacks on energy infrastructure quietly unfolded across Poland—targeting more than … Cyber Attacks on Energy Infrastructure: Lessons from CERT Polska’s Renewable Energy IncidentRead more
zero trust
Vishing Attacks on SaaS Platforms: How ShinyHunters Is Bypassing MFA at Scale
In early 2026, Google-owned Mandiant identified a sharp escalation in vishing attacks on SaaS platforms, where … Vishing Attacks on SaaS Platforms: How ShinyHunters Is Bypassing MFA at ScaleRead more
Google Disrupts Massive Residential Proxy Networks Abusing User Devices
Residential proxy networks have quietly become one of the most abused infrastructures in modern cybercrime—and most … Google Disrupts Massive Residential Proxy Networks Abusing User DevicesRead more
Dangerous TP-Link Bug Lets Attackers Seize VIGI Cameras
In early 2026, a major authentication bypass vulnerability surfaced in TP‑Link’s widely deployed VIGI camera series—putting … Dangerous TP-Link Bug Lets Attackers Seize VIGI CamerasRead more
ChatGPT Go Security: Risks, Controls & Enterprise Policy Guide
ChatGPT Go security is now a board-level conversation. With a global $8/month tier rolling out across … ChatGPT Go Security: Risks, Controls & Enterprise Policy GuideRead more
Malicious File Converter Apps: How Free Tools Infect Systems
In 2024 alone, initial access via trojanized software accounted for a growing share of enterprise malware … Malicious File Converter Apps: How Free Tools Infect SystemsRead more
ServiceNow AI Vulnerability Exposes Emerging Risks in Autonomous Agent Security
In late 2025, researchers uncovered a high‑severity ServiceNow AI vulnerability (CVE‑2025‑12420, CVSS 9.3) that exposed organizations … ServiceNow AI Vulnerability Exposes Emerging Risks in Autonomous Agent SecurityRead more
ANCHOR and the Future of Critical Infrastructure Security: How DHS Is Reshaping Public‑Private Cyber Threat Collaboration
In an era where ransomware attacks disrupt hospitals, state‑sponsored actors target energy grids, and supply-chain cyber … ANCHOR and the Future of Critical Infrastructure Security: How DHS Is Reshaping Public‑Private Cyber Threat CollaborationRead more
CrowdStrike Acquires Browser Security Startup Seraphic for $400 Million
CrowdStrike has announced the acquisition of Seraphic Security, an Israeli browser security startup, in a deal … CrowdStrike Acquires Browser Security Startup Seraphic for $400 MillionRead more
Trend Micro Apex Flaw Allows Silent RCE Attacks
Security management platforms are designed to centralize control, visibility, and trust. But when those platforms themselves … Trend Micro Apex Flaw Allows Silent RCE AttacksRead more