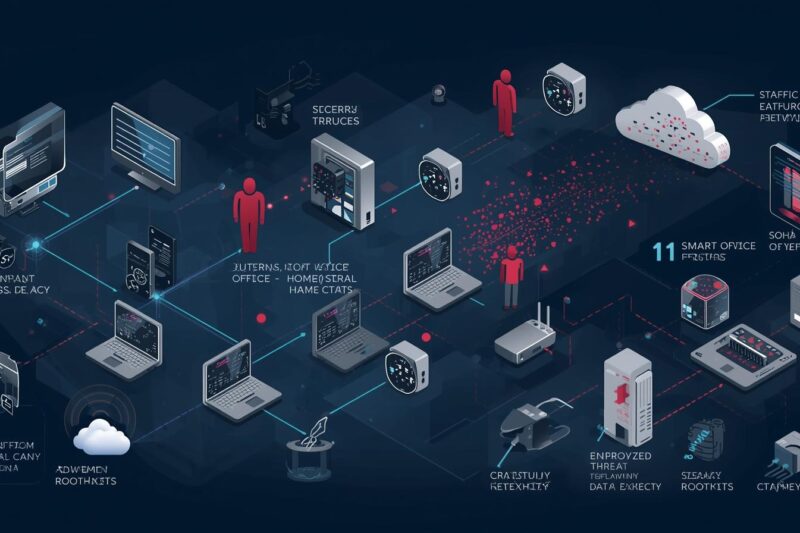
Operational Relay Box (ORB) networks have emerged as one of the most sophisticated tools used by … ORB Networks: How Compromised IoT Devices Mask CyberattacksRead more
zero trust
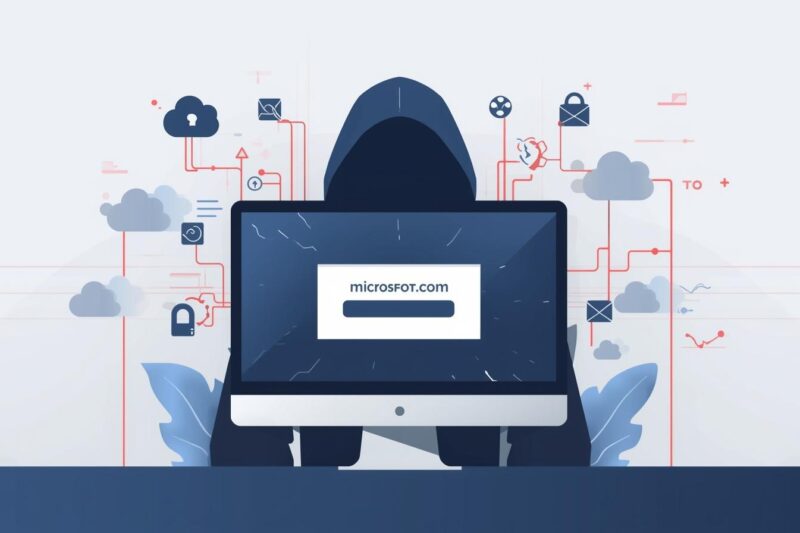
Digital Squatting Attacks: How Lookalike Domains Steal Credentials
In 2025 alone, more than 6,200 adversarial domain name cases were recorded, contributing to a 68% … Digital Squatting Attacks: How Lookalike Domains Steal CredentialsRead more
Defense Sector Cybersecurity: Rising Espionage and Supply Chain Threats
Modern warfare has transcended physical battlefields, increasingly targeting the digital infrastructure and supply chains critical to … Defense Sector Cybersecurity: Rising Espionage and Supply Chain ThreatsRead more
VoidLink Framework: The Next Evolution in Linux Malware Threats
The VoidLink Framework represents a new generation of modular malware designed for modern cloud and Linux … VoidLink Framework: The Next Evolution in Linux Malware ThreatsRead more
Apple Pay Phishing Attack: How to Detect and Stop Vishing Scams
The Apple Pay phishing attack is rapidly evolving — and it’s no longer just about fake … Apple Pay Phishing Attack: How to Detect and Stop Vishing ScamsRead more
Firebase Phishing Attacks: How Hackers Abuse Trusted Cloud Apps
In 2025, phishing remained the #1 initial access vector in enterprise breaches, and attackers are now … Firebase Phishing Attacks: How Hackers Abuse Trusted Cloud AppsRead more
Notepad++ Update Mechanism Hijacked: How Attackers Delivered Malware to Users
In a striking example of software supply chain compromise, the widely used text editor Notepad++ had … Notepad++ Update Mechanism Hijacked: How Attackers Delivered Malware to UsersRead more
Arsink RAT: Android Malware Enabling Remote Access & Data Theft
Mobile devices have become prime targets for cybercriminals. In recent threat intelligence reporting, Arsink RAT has … Arsink RAT: Android Malware Enabling Remote Access & Data TheftRead more
Windows 11 Security Feature Strengthens System File Protection
In modern cyber incidents, attackers don’t always start with malware or zero-days — sometimes, they start … Windows 11 Security Feature Strengthens System File ProtectionRead more
Johnson Controls SQL Injection Vulnerability: Risk & Defense Guide
In early 2026, security teams were alerted to a critical industrial control system (ICS) vulnerability affecting … Johnson Controls SQL Injection Vulnerability: Risk & Defense GuideRead more