A potential data exposure involving Adobe has raised serious concerns about third-party vendor security and access … Adobe Breach Allegation: 13M Support Tickets Exposed Read more
RAT malware
SEO Poisoning Campaign Impersonates 25+ Apps to Deliver AsyncRAT
A long-running SEO poisoning campaign has been targeting Windows users by impersonating popular software downloads and … SEO Poisoning Campaign Impersonates 25+ Apps to Deliver AsyncRATRead more
Phishing-Led Agent Tesla Campaign Evades Detection
Cybercriminals don’t always need zero-day exploits to succeed. In fact, many of today’s most damaging breaches … Phishing-Led Agent Tesla Campaign Evades DetectionRead more
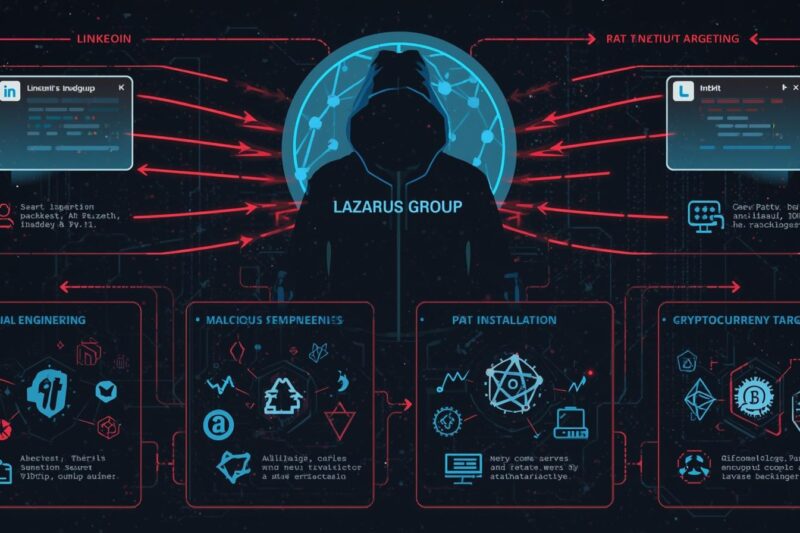
Lazarus Group’s ‘Graphalgo’ Fake Recruiter Campaign Targets Crypto Developers
Since May 2025, the North Korean state-sponsored hacking team, Lazarus Group, has been running a highly … Lazarus Group’s ‘Graphalgo’ Fake Recruiter Campaign Targets Crypto DevelopersRead more