Cybercriminals are constantly innovating, and one of the most alarming phishing techniques gaining traction is the … Browser-in-the-Browser (BitB) Attacks: The New Phishing FrontierRead more
credential theft
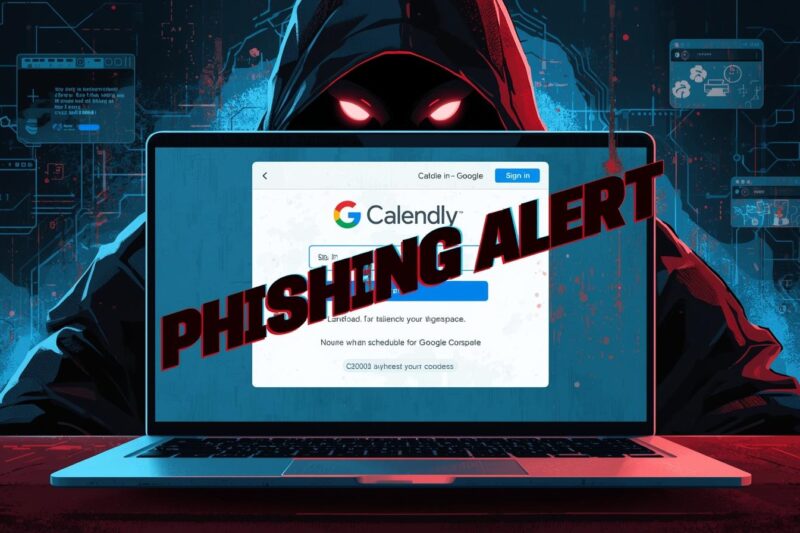
Cybercriminals Exploit Calendly Links in Advanced Phishing Scheme
A large-scale phishing campaign has been uncovered, targeting Google Workspace and Facebook Business account users through … Cybercriminals Exploit Calendly Links in Advanced Phishing SchemeRead more
ValleyRAT Malware Targets Job Seekers with Fake Job Offers
Cybercriminals have launched a sophisticated malware campaign called ValleyRAT, preying on job seekers through fake recruitment … ValleyRAT Malware Targets Job Seekers with Fake Job OffersRead more
18,000 Reasons to Stay Vigilant This Holiday Season!!!
The 2025 holiday shopping season is being hit by a perfect storm of cyber threats, as … 18,000 Reasons to Stay Vigilant This Holiday Season!!!Read more
GitHub Actions Exploited by Shai Hulud v2 to Steal Secrets
The software supply chain faces a new and sophisticated threat: Shai Hulud v2, a malware campaign … GitHub Actions Exploited by Shai Hulud v2 to Steal SecretsRead more