Full-disk encryption is often considered the last line of defense against data breaches. But what happens … CryptoPro Secure Disk Vulnerabilities Enable Root AccessRead more
credential theft
ClickFix Infostealer Uses Fake CAPTCHA Lures to Compromise Victims
Imagine visiting a website and being asked to complete a CAPTCHA—only to unknowingly trigger a malware … ClickFix Infostealer Uses Fake CAPTCHA Lures to Compromise VictimsRead more
Diesel Vortex Cybercrime Group Targets Global Logistics Sector
In today’s interconnected supply chain, cybersecurity in logistics is more critical than ever. Between September 2025 … Diesel Vortex Cybercrime Group Targets Global Logistics SectorRead more
Malicious OpenClaw Skills Deliver AMOS macOS Stealer
The Atomic macOS Stealer (AMOS) campaign has entered a dangerous new phase. Instead of hiding inside … Malicious OpenClaw Skills Deliver AMOS macOS StealerRead more
CharlieKirk Grabber Stealer: How Windows Systems Are Targeted for Credential Theft
In February 2026, cybersecurity researchers uncovered a new Python-based infostealer, CharlieKirk Grabber, actively targeting Windows systems. … CharlieKirk Grabber Stealer: How Windows Systems Are Targeted for Credential TheftRead more
Booking.com Phishing Campaign: Multi-Stage Fraud Exposed
The latest Booking.com phishing campaign is a stark reminder that attackers don’t just target individuals—they weaponize … Booking.com Phishing Campaign: Multi-Stage Fraud ExposedRead more
AI-Driven Phishing Attacks: Detection and Defense Strategies
AI-Driven Phishing Attacks are rapidly becoming one of the most dangerous cyber threats facing enterprises and … AI-Driven Phishing Attacks: Detection and Defense StrategiesRead more
Microsoft Outlook Add-in Stolen 4,000 Accounts: Lessons for Cloud Security & Threat Detection
In a striking reminder of modern cyber risks, security researchers have uncovered the first documented case … Microsoft Outlook Add-in Stolen 4,000 Accounts: Lessons for Cloud Security & Threat DetectionRead more
Fake CAPTCHA Attacks Drive LummaStealer Malware Resurgence
LummaStealer, a notorious information-stealing malware, has resurfaced after a 2025 disruption by law enforcement. This renewed … Fake CAPTCHA Attacks Drive LummaStealer Malware ResurgenceRead more
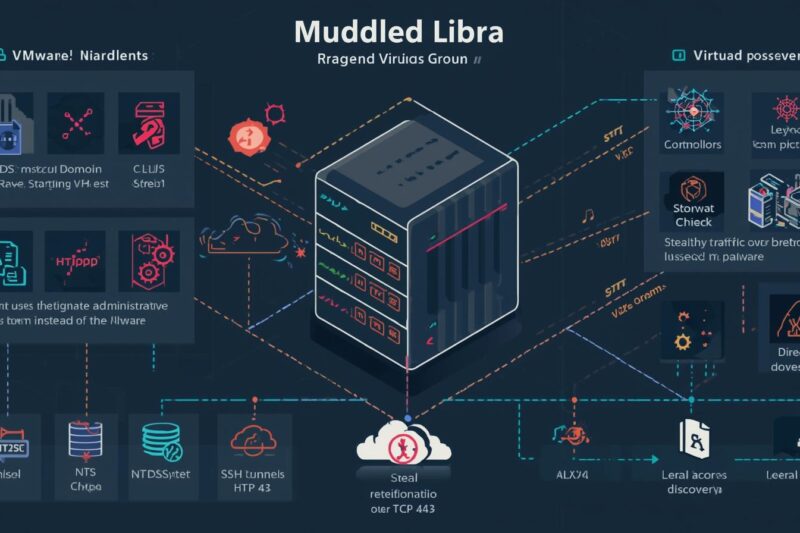
Rogue VM Reveals Muddled Libra Tactics in VMware vSphere Attack
In September 2025, investigators uncovered a rogue virtual machine inside a VMware vSphere environment, which was … Rogue VM Reveals Muddled Libra Tactics in VMware vSphere AttackRead more