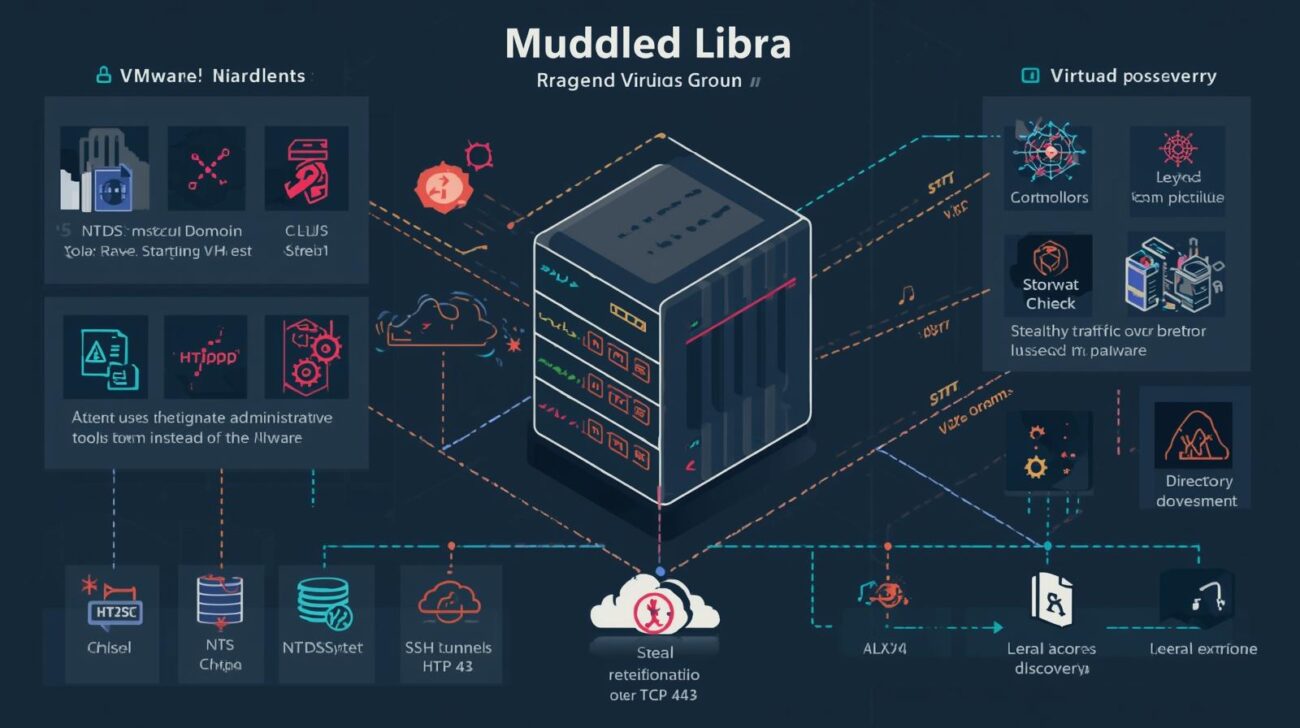
In September 2025, investigators uncovered a rogue virtual machine inside a VMware vSphere environment, which was tied with high confidence to the threat group Muddled Libra (also known as Scattered Spider or UNC3944).
This incident highlights how attackers can use a single virtual machine as a staging host to move laterally, access identity systems, and exfiltrate sensitive data—all while blending into normal infrastructure activity.
In this article, we’ll examine:
- How the rogue VM enabled Muddled Libra’s attack
- Tactics, techniques, and procedures (TTPs) used
- Steps defenders can take to reduce risk and detect living-off-the-land attacks
How the Attack Unfolded
Initial Access and VM Creation
- The attackers gained access to the vSphere environment and, within two hours, created a new VM named “New Virtual Machine.”
- This VM acted as a quiet staging host, allowing attackers to recon the network, download tools, and move laterally.
- Muddled Libra relies heavily on social engineering techniques like smishing, vishing, and impersonation, often convincing help desks to reset passwords or multi-factor authentication for legitimate accounts.
Exploitation of Existing Infrastructure
Unlike typical malware campaigns, this group often avoids heavy malware, instead leveraging legitimate admin utilities to remain undetected:
- Stolen certificates were used to forge Kerberos tickets for expanded access
- Virtualized domain controllers were powered down and VMDKs mounted to the rogue VM
- Critical files like NTDS.dit and SYSTEM were copied to the VM for credential harvesting
- Directory discovery was performed with ADRecon, reviewing service principal names for further lateral movement
Cloud Data Access and Exfiltration
- The attackers accessed the organization’s Snowflake environment and attempted to move mailbox data, including PST files, off-network via file-sharing sites and S3 Browser
- Persistent Chisel SSH tunnels were established, disguised as normal HTTPS traffic over TCP 443
- Files were delivered in a ZIP archive (
goon.zip) from an attacker-controlled AWS S3 bucket, maintaining stealth for approximately 15 hours
Tactics, Techniques, and Procedures (TTPs)
Key TTPs observed in this incident include:
- Living-Off-The-Land
- Using legitimate vSphere and admin tools rather than custom malware
- Social Engineering
- Smishing, vishing, and help desk impersonation for account takeover
- Credential Theft and Ticket Forging
- Extracting certificates, NTDS.dit, and SYSTEM to forge access tickets
- Stealthy Persistence
- Rogue VM with SSH tunnel using Chisel, hiding traffic as normal HTTPS
- Cloud Data Access
- Lateral movement into Snowflake and off-network file exfiltration
Defensive Measures
Organizations can mitigate similar attacks by focusing on identity, monitoring, and vSphere security controls:
- Identity and Access Management
- Enforce least privilege for vSphere and admin accounts
- Monitor for suspicious account activity and MFA bypass attempts
- VM and Infrastructure Monitoring
- Watch for unexpected VM creation, domain controller power-offs, and VMDK mounts
- Monitor unusual use of standard admin tools
- Network and Cloud Monitoring
- Detect anomalous TCP 443 traffic from newly created systems
- Monitor access to cloud platforms for unusual file downloads or exfiltration patterns
- Living-Off-The-Land Awareness
- Train security teams to detect misuse of legitimate admin utilities
- Implement behavioral analytics to identify anomalies early
Conclusion
This rogue VM incident demonstrates the risks of living-off-the-land attacks in VMware vSphere environments. Threat groups like Muddled Libra leverage legitimate infrastructure and social engineering to evade detection, gain credentials, and exfiltrate sensitive data.
Organizations should implement tight identity controls, continuous monitoring, and behavioral analytics to detect anomalous activity before it escalates into broader lateral movement or data theft.