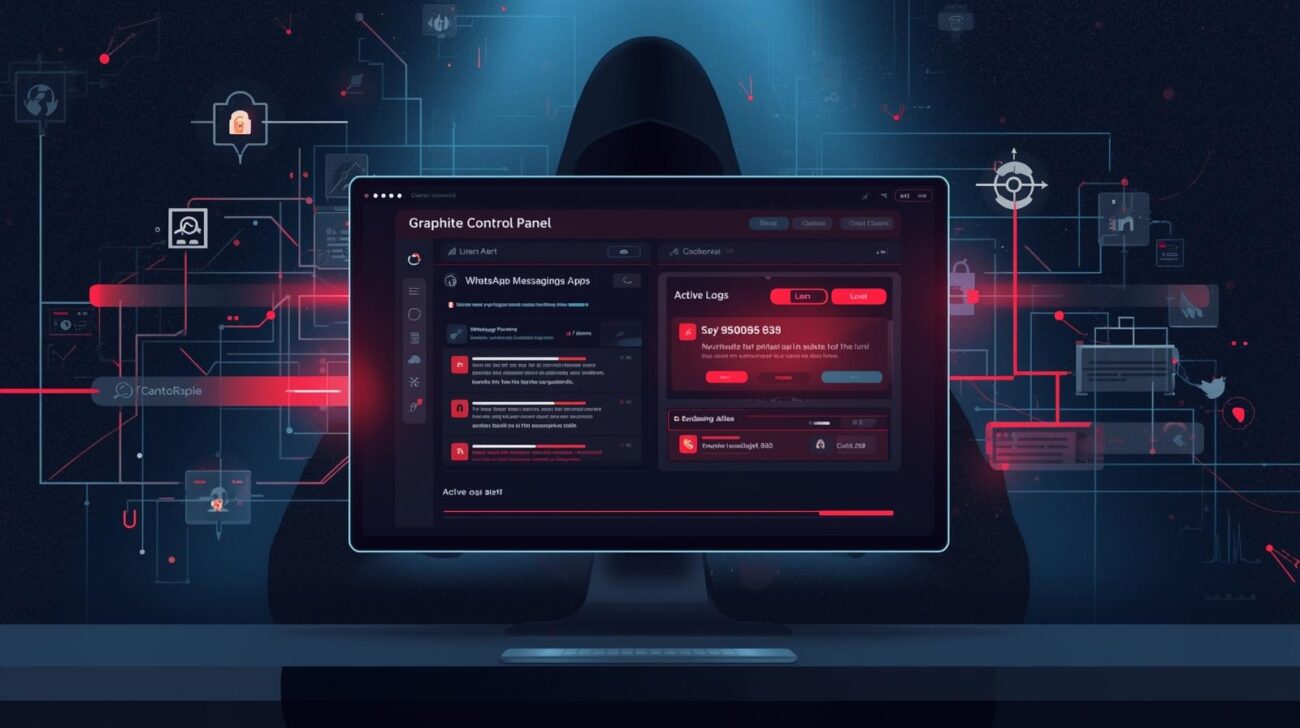
In a rare operational security mishap, Israeli spyware firm Paragon Solutions accidentally exposed its Graphite control panel in a LinkedIn post on February 11, 2026. This slip provided cybersecurity researchers and the public with unprecedented insight into a tool designed for remote surveillance of encrypted communications.
This article explores what was revealed, the implications for OPSEC in the spyware industry, and the broader cybersecurity and human rights concerns tied to Graphite.
What Happened
Cybersecurity researcher Jurre van Bergen identified the LinkedIn post by Paragon’s general counsel. The screenshot showcased:
- A dashboard with active interception logs dated February 10, 2026
- Monitoring of encrypted messaging apps like WhatsApp via zero-click exploits
- A Czech phone number labeled “Valentina” under surveillance
Citizen Lab researcher John Scott-Railton described it as an “epic OPSEC fail”, highlighting the risks of operational missteps even in a secretive spyware industry.
The image was quickly deleted, but its circulation online intensified scrutiny on Paragon and its practices.
About Paragon and Graphite Spyware
Founded in 2019 in Israel, Paragon Solutions markets Graphite as a sophisticated surveillance tool capable of:
- Remote access to cell phones
- Intercepting messages from apps like WhatsApp and Signal
- Extracting stored data and live communications
- Operating without user interaction, via zero-click exploits
Dubbed “mercenary spyware,” Graphite is positioned as a “cleaner” alternative to NSO Group’s Pegasus. Yet allegations persist of its use against journalists, civil society members, and activists.
Notable Incidents
- Early 2025: WhatsApp reported Graphite targeting 90 journalists and civil society figures, including Italian editor Francesco Cancellato.
- Citizen Lab analysis linked Graphite infrastructure to Israel and identified forensic markers like “BIGPRETZEL” on infected Android devices.
Global Client Base
Citizen Lab reports that Graphite’s clients include government entities in:
- Australia, Canada, Cyprus, Denmark, Israel, and Singapore
- U.S. government purchases noted by the Trump administration in January 2025, supporting ICE operations
Civil rights groups in Canada have documented Graphite deployments targeting activists, while other nations face scrutiny for contracts enabling state surveillance of critics.
OPSEC and Cybersecurity Implications
This LinkedIn exposure underscores persistent operational security (OPSEC) risks in the spyware industry:
- Even highly secretive firms can leak sensitive operational data
- Zero-click spyware targeting encrypted apps reveals critical cybersecurity vulnerabilities
- Missteps can amplify public and regulatory scrutiny, affecting contracts and reputation
For cybersecurity professionals, the incident highlights the need to:
- Monitor zero-day exploit usage
- Understand spyware lifecycle and deployment tactics
- Protect endpoints from sophisticated remote attacks
Human Rights and Ethical Concerns
Graphite’s capabilities raise significant ethical questions:
- Journalist and activist targeting: Surveillance of protected civil society figures
- Cross-border human rights impact: Governments using Graphite to monitor citizens beyond their jurisdiction
- Transparency and accountability gaps: Clients often remain undisclosed or justified under national security
These concerns underscore the broader debate on the mercenary spyware market and its regulation.
Best Practices for Individuals and Organizations
- Enable app security features:
- Update messaging apps to the latest versions to patch zero-click vulnerabilities.
- Use encrypted alternatives with caution:
- Even end-to-end encryption can be compromised by spyware on the device itself.
- Endpoint hygiene and monitoring:
- Deploy mobile threat detection solutions to flag suspicious apps or behaviors.
- Awareness for high-risk users:
- Journalists, activists, and political figures should maintain separate devices for sensitive communications.
- Regular forensic audits:
- Review device logs and network activity for signs of unauthorized surveillance.
Expert Insights
- Cybersecurity Takeaway: Accidental exposure demonstrates that even commercial spyware vendors are vulnerable to information leaks, which can compromise ongoing surveillance operations.
- Regulatory Perspective: Incidents like this fuel calls for stronger international oversight of mercenary spyware sales and export.
- Operational Security Lesson: Metadata, screenshots, and casual public posting can reveal critical operational details, putting both operators and targets at risk.
FAQs
Q1: What is Paragon Graphite spyware?
A: Graphite is Israeli-developed spyware capable of zero-click surveillance of phones and encrypted apps like WhatsApp and Signal.
Q2: How was it exposed?
A: The control panel was accidentally shared in a LinkedIn post by Paragon’s general counsel.
Q3: Who are the main targets?
A: Journalists, civil society members, activists, and in some cases, government-identified individuals.
Q4: Which countries use Graphite?
A: Reported clients include Australia, Canada, Cyprus, Denmark, Israel, Singapore, and the U.S. government.
Q5: How can users protect themselves?
A: Keep devices updated, use secure endpoints, avoid high-risk apps, and separate sensitive communications to minimize exposure.
Conclusion
The Paragon LinkedIn exposure provides a rare look behind the curtain of commercial spyware, revealing operational mistakes, zero-click surveillance capabilities, and ethical concerns surrounding its deployment.
Key Takeaways:
- Operational security lapses can expose surveillance infrastructure
- Graphite’s zero-click exploits highlight ongoing risks to encrypted communications
- Individuals and organizations must remain vigilant, especially high-risk users
Next Step: Strengthen endpoint security, patch messaging apps, and adopt practices to mitigate device-level spyware risks.