In modern cyber incidents, attackers don’t always start with malware or zero-days — sometimes, they start … Windows 11 Security Feature Strengthens System File ProtectionRead more
Johnson Controls SQL Injection Vulnerability: Risk & Defense Guide
In early 2026, security teams were alerted to a critical industrial control system (ICS) vulnerability affecting … Johnson Controls SQL Injection Vulnerability: Risk & Defense GuideRead more
European Email Alternatives: Secure Options Beyond Big Tech
Email is still the backbone of digital identity. From SaaS logins to password resets and enterprise … European Email Alternatives: Secure Options Beyond Big TechRead more
Threat Actor Collaboration: Why Defenders Are Falling Behind
Threat actor collaboration is no longer theoretical — it’s actively reshaping the global cyber threat landscape. … Threat Actor Collaboration: Why Defenders Are Falling BehindRead more
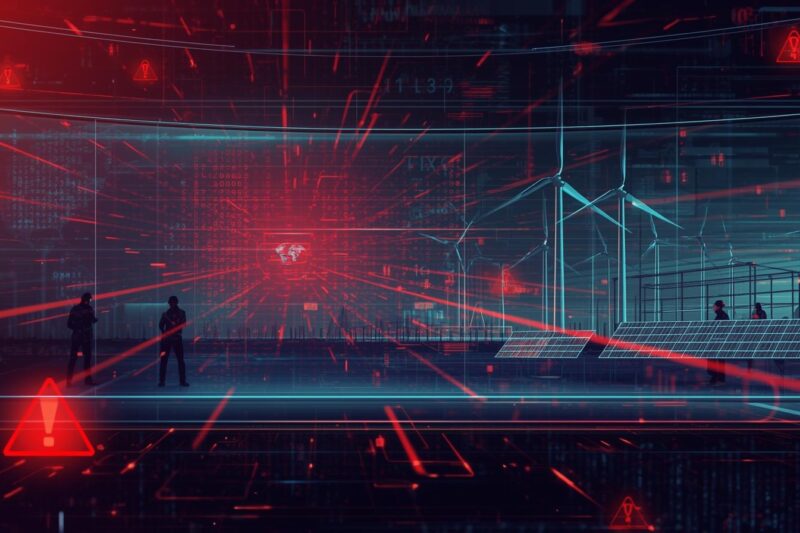
Cyber Attacks on Energy Infrastructure: Lessons from CERT Polska’s Renewable Energy Incident
On December 29, 2025, coordinated cyber attacks on energy infrastructure quietly unfolded across Poland—targeting more than … Cyber Attacks on Energy Infrastructure: Lessons from CERT Polska’s Renewable Energy IncidentRead more
Vishing Attacks on SaaS Platforms: How ShinyHunters Is Bypassing MFA at Scale
In early 2026, Google-owned Mandiant identified a sharp escalation in vishing attacks on SaaS platforms, where … Vishing Attacks on SaaS Platforms: How ShinyHunters Is Bypassing MFA at ScaleRead more
Iran-Linked RedKitten Cyber Campaign Targets Human Rights NGOs
Nation-state cyber operations increasingly blur the line between espionage, psychological manipulation, and digital repression. A newly … Iran-Linked RedKitten Cyber Campaign Targets Human Rights NGOsRead more
Metasploit Framework Update Exposes Critical RCE Risks in Enterprise Apps
In modern enterprise environments, attackers no longer rely on single vulnerabilities—they chain them. That reality is … Metasploit Framework Update Exposes Critical RCE Risks in Enterprise AppsRead more
LLMjacking Exposed: How Attackers Hijack and Monetize AI Endpoints
Large Language Models (LLMs) are rapidly becoming core enterprise infrastructure—but attackers are already exploiting the weakest … LLMjacking Exposed: How Attackers Hijack and Monetize AI EndpointsRead more
Google Disrupts Massive Residential Proxy Networks Abusing User Devices
Residential proxy networks have quietly become one of the most abused infrastructures in modern cybercrime—and most … Google Disrupts Massive Residential Proxy Networks Abusing User DevicesRead more