In early February 2026, the Russian government attempted to block WhatsApp nationwide, affecting over 100 million … Russia Blocks WhatsApp for Over 100 Million UsersRead more
Threat Actors Exploit Employee Monitoring Tools for Ransomware
Cybercriminals are evolving their tactics. Instead of relying solely on traditional malware, they are now leveraging … Threat Actors Exploit Employee Monitoring Tools for RansomwareRead more
Palo Alto Firewall Vulnerability Forces Reboot Loops
Enterprise networks rely heavily on firewalls to protect against malicious traffic and DNS-based threats. However, a … Palo Alto Firewall Vulnerability Forces Reboot LoopsRead more
Evilmouse Attack: $44 Hardware Implant That Hacks Systems
Most security awareness training teaches employees one simple rule: never plug in unknown USB drives. But … Evilmouse Attack: $44 Hardware Implant That Hacks SystemsRead more
Promptware Attack: Hackers Can Use Google Calendar to Spy via Zoom
Imagine this: you check your Google Calendar, and a seemingly harmless meeting invite appears. You ask … Promptware Attack: Hackers Can Use Google Calendar to Spy via ZoomRead more
Microsoft Outlook Add-in Stolen 4,000 Accounts: Lessons for Cloud Security & Threat Detection
In a striking reminder of modern cyber risks, security researchers have uncovered the first documented case … Microsoft Outlook Add-in Stolen 4,000 Accounts: Lessons for Cloud Security & Threat DetectionRead more
Fake CAPTCHA Attacks Drive LummaStealer Malware Resurgence
LummaStealer, a notorious information-stealing malware, has resurfaced after a 2025 disruption by law enforcement. This renewed … Fake CAPTCHA Attacks Drive LummaStealer Malware ResurgenceRead more
AdBlock Filter Lists Can Expose Your Location Despite VPN
VPNs are widely trusted for protecting online privacy, but a new privacy risk is emerging. Even … AdBlock Filter Lists Can Expose Your Location Despite VPNRead more
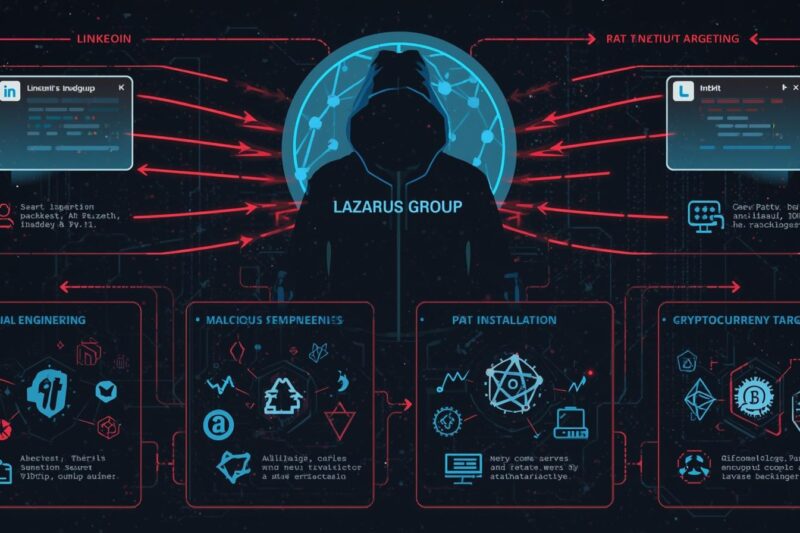
Lazarus Group’s ‘Graphalgo’ Fake Recruiter Campaign Targets Crypto Developers
Since May 2025, the North Korean state-sponsored hacking team, Lazarus Group, has been running a highly … Lazarus Group’s ‘Graphalgo’ Fake Recruiter Campaign Targets Crypto DevelopersRead more
Google Warns of Hackers Exploiting Gemini AI for Multi-Stage Malware
Google’s Threat Intelligence Group (GTIG) has revealed that threat actors are abusing Gemini AI to automate … Google Warns of Hackers Exploiting Gemini AI for Multi-Stage MalwareRead more