Operational Relay Box (ORB) networks have emerged as one of the most sophisticated tools used by cybercriminals to obscure attacks from security teams. These networks leverage compromised IoT devices, small office/home office (SOHO) routers, and virtual private servers (VPS) to relay malicious traffic, making it nearly impossible for defenders to trace the source.
The threat became alarmingly clear in February 2026, when Singapore’s Cyber Security Agency revealed that the state-sponsored group UNC3886 targeted all four major telecommunications operators — M1, SIMBA Telecom, Singtel, and StarHub — exploiting zero-day vulnerabilities and advanced rootkits to maintain persistent access to critical infrastructure.
This article explores:
- How ORB networks operate
- Attack infrastructure and pre-positioning tactics
- Risks to organizations
- Best practices for detection and mitigation
What Are ORB Networks?
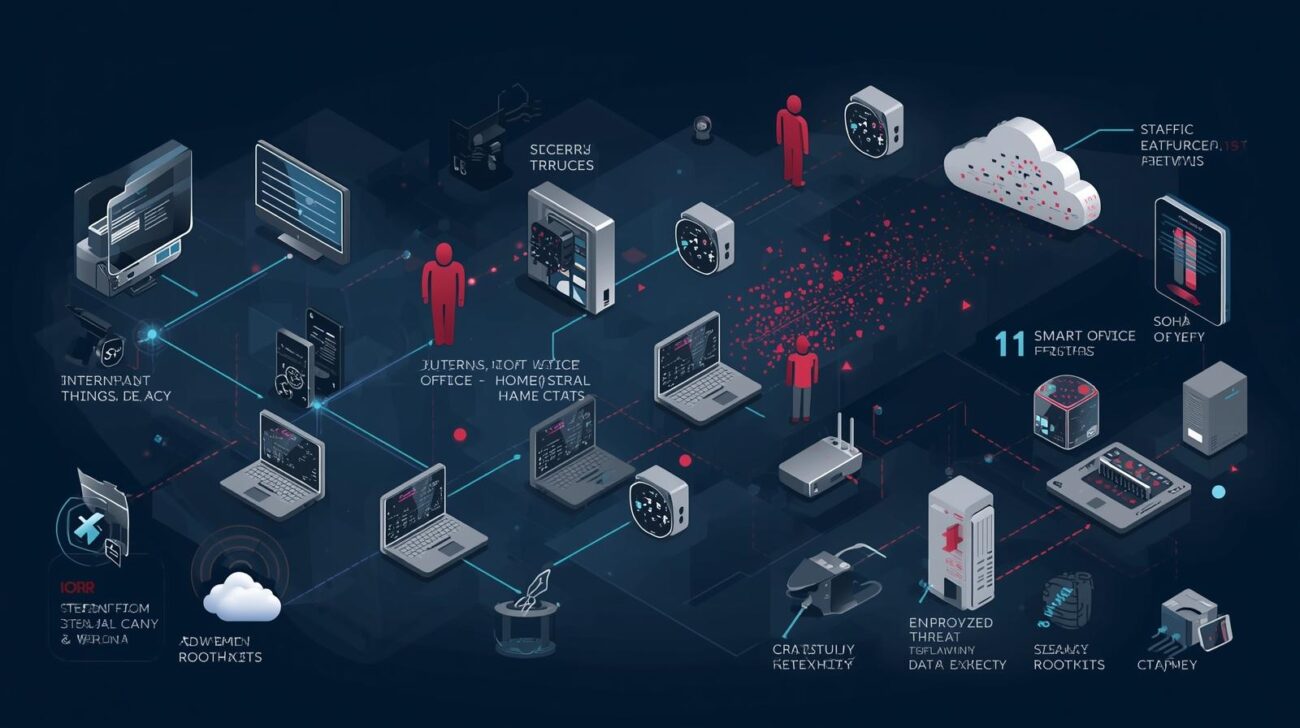
ORB networks consist of:
- Compromised IoT devices (smart cameras, printers, appliances)
- SOHO routers used in homes and small offices
- Virtual Private Servers (VPS) to manage traffic
These networks act like private residential proxy services, allowing malicious activity to blend seamlessly with legitimate traffic.
Key advantage: Attackers can hide the true origin of their attacks, making detection and attribution extremely difficult.
How ORB Networks Mask Cyberattacks
- Distributed Relay Architecture
- Attack traffic is routed through multiple compromised nodes
- Nodes can be rapidly replaced if blocked, ensuring operational continuity
- Traffic Blending
- Malicious traffic mimics normal home and business broadband activity
- Security teams risk disrupting legitimate services if they block nodes
- Pre-Positioning for Future Attacks
- Adversaries deploy relay nodes months in advance
- Enables reconnaissance and perimeter probing without triggering alerts
- Geofencing Evasion
- Attackers route traffic through nodes close to the target
- Makes malicious activity appear local and legitimate to monitoring systems
Case Study: Singapore Telecom Attacks
In February 2026, the UNC3886 group exploited ORB networks to target:
- M1
- SIMBA Telecom
- Singtel
- StarHub
Tactics observed:
- Exploitation of zero-day vulnerabilities in perimeter firewalls
- Deployment of advanced rootkits to evade intrusion detection systems
- Persistent access maintained while blending in with normal network traffic
This attack demonstrates how ORB networks allow state-sponsored groups to operate stealthily, complicating detection and mitigation.
Risks and Strategic Advantages for Attackers
- Resilience and scalability: Compromised devices can be swapped quickly
- Operational security: Early infrastructure deployment allows months of reconnaissance
- Detection evasion: Traffic appears legitimate, bypassing standard monitoring
- Geographically aware targeting: Circumvents geofencing and network segmentation
For organizations, these factors make traditional defensive approaches insufficient.
Detection and Mitigation Strategies
1. Proactive Threat Hunting
- Continuously scan networks for anomalous outbound traffic
- Use sandboxed honeypots to detect suspicious device behaviors
2. Behavioral Analytics
- Identify deviations in IoT and router traffic patterns
- Correlate activity across devices to detect relay networks
3. Zero Trust Security Model
- Implement strict access controls regardless of network location
- Segment networks to limit lateral movement
4. Regular Router and Device Updates
- Patch vulnerabilities promptly
- Disable unnecessary remote management features
5. Advanced Threat Intelligence Integration
- Subscribe to feeds identifying compromised devices and emerging ORB tactics
- Share threat intelligence across industry peers
Conclusion
ORB networks represent a new frontier in cyberattack stealth. By leveraging compromised IoT devices, SOHO routers, and VPS infrastructure, attackers can maintain persistence, evade detection, and pre-position for future attacks.
Key takeaways for organizations:
- Adopt Zero Trust models and proactive threat hunting
- Monitor IoT and router traffic for anomalous behavior
- Ensure devices are regularly patched and properly configured
- Integrate advanced threat intelligence for early detection
Staying ahead of ORB networks requires continuous vigilance, layered defenses, and behavioral analytics, as traditional perimeter-based security alone is no longer sufficient.