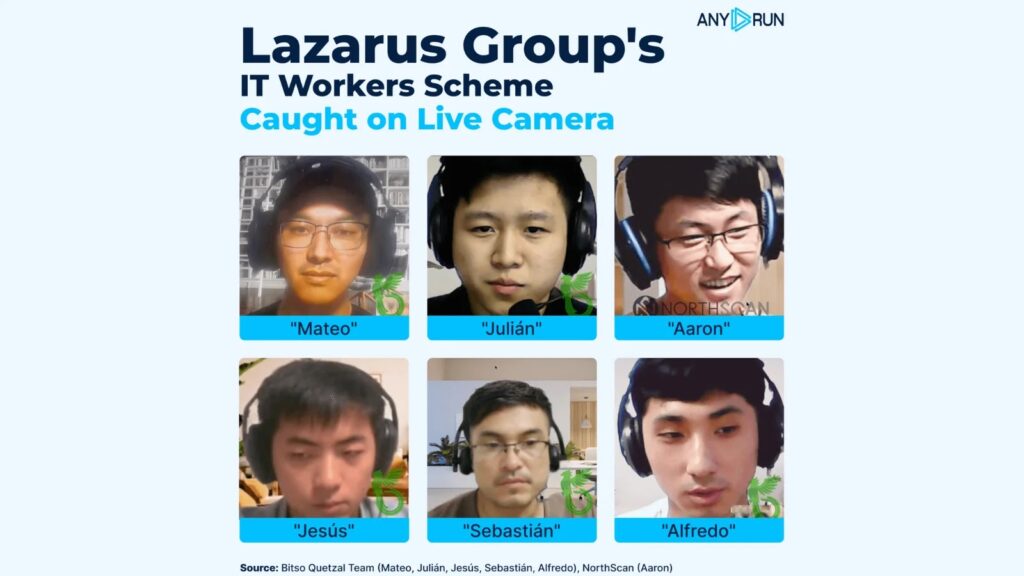
In a groundbreaking cybersecurity sting, researchers have exposed the Lazarus Group’s Famous Chollima unit running its notorious remote IT worker scheme—caught “live on camera” inside a controlled sandbox environment.
This unprecedented investigation reveals how North Korean cyber operatives infiltrate Western finance, crypto/Web3, healthcare, and engineering firms using identity theft, rented identities, and off-the-shelf tools to pose as legitimate remote developers.
The Setup: A Honeypot for Lazarus
The operation began when NorthScan’s Heiner García impersonated a U.S. developer targeted on GitHub by a recruiter calling himself “Aaron” or “Blaze.” Blaze pitched a shady “job hunting business,” offering a salary cut in exchange for full access to the victim’s laptop, Social Security Number, bank accounts, and identity documents—while his team secretly did the work.
This tactic aligns with a broader Famous Chollima pattern: stealing CVs or convincing junior engineers to “rent” their identities so DPRK operatives can embed themselves in sensitive industries.
The Trap: Virtual Laptop Farm
Instead of handing over real machines, BCA LTD’s Mauro Eldritch and sandbox provider ANY.RUN deployed a “laptop farm” of extended-runtime virtual machines, each mimicking a heavily used U.S. developer notebook. These environments ran Windows 10/11, pre-installed IDEs, browser profiles, and tunneled through U.S. residential proxies to pass recruiter checks.
Researchers monitored live screens, file operations, and network flows, while inducing crashes and network glitches to keep attackers contained.
Blaze Falls for the Honeypot
Once Blaze received AnyDesk credentials, he connected and ran DxDiag and systeminfo to verify hardware, then checked geolocation via browser. Traffic analysis linked his IP to Astrill VPN, a service long associated with Lazarus and DPRK IT worker activity.
As disruptions mounted, Blaze left pleading Notepad messages for “Andy,” pulled in a colleague named “Assassin,” and struggled with CAPTCHAs—all under full surveillance.
Inside Lazarus’ Toolkit
When Blaze synced his Chrome profile, investigators uncovered a toolkit focused on AI-driven job automation, not malware. Installed extensions included:
- Simplify Copilot, AiApply, Final Round AI – for auto-filling applications and generating interview answers.
- OTP.ee, Authenticator.cc – for capturing and replaying one-time passwords.
- Google Remote Desktop via PowerShell layered on AnyDesk – enabling persistent access disguised as normal remote-work tools.
Why This Matters
The sting comes amid U.S. law enforcement crackdowns on DPRK IT worker schemes. A June 2025 case revealed 100+ infiltrated companies, 80 stolen U.S. identities, and physical “laptop farms” on American soil. Later actions sought $15M in penalties, citing theft of crypto assets, source code, and defense data.
Experts say this honeypot demonstrates how sandboxing human-driven intrusions can expose full attack chains—from GitHub spam and Telegram recruiting to VPN abuse and remote-desktop layering. Employers must adopt stronger identity verification, device-control policies, and skepticism toward too-good-to-be-true remote offers.