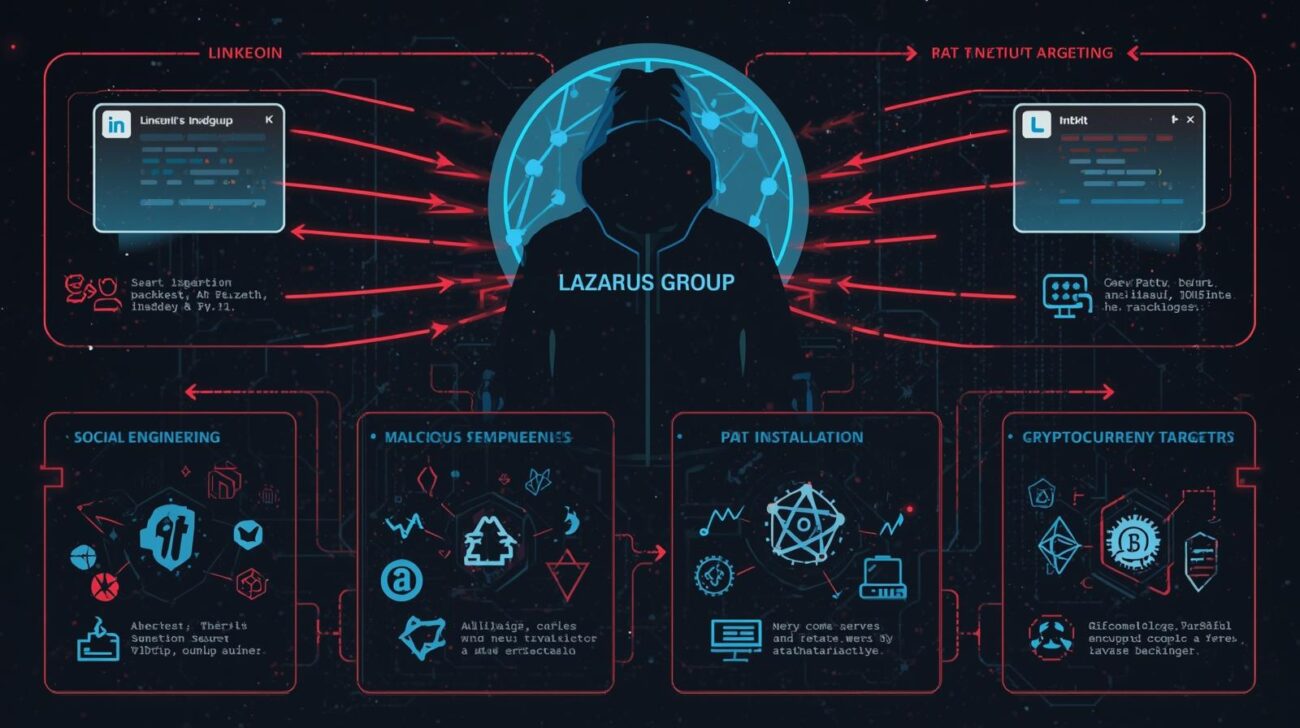
Since May 2025, the North Korean state-sponsored hacking team, Lazarus Group, has been running a highly sophisticated campaign known as “Graphalgo.”
This operation targets cryptocurrency developers using fake recruiter schemes and weaponized open-source repositories, including GitHub, npm, and PyPI. By combining social engineering with malware distribution, the attackers turn legitimate developer workflows into infection vectors.
This article explores the Graphalgo campaign, infection methods, multi-stage payloads, and mitigation strategies for developers and organizations in the crypto space.
The Graphalgo Fake Recruiter Campaign
Social Engineering Tactics
The attackers actively engage targets through:
- Professional networking platforms: LinkedIn, Facebook
- Developer forums: Reddit, Stack Overflow
- Fake company websites: “Veltrix Capital”
Victims are lured with job offers in blockchain and cryptocurrency development, followed by coding test assignments that seem legitimate but contain hidden malicious dependencies.
Exploiting Trusted Repositories
Graphalgo leverages open-source infrastructure to hide its malware:
- GitHub repositories host coding tasks and assignments
- npm and PyPI packages contain obfuscated dependencies that deliver malware
- Packages like “bigmathutils” accumulated over 10,000 downloads before a malicious version was released
This approach ensures that developers unwittingly execute malware during normal development activities, such as installing dependencies or running tests.
Infection Mechanism and Multi-Stage Malware
- Initial Contact: Victims receive interview assignments through GitHub repositories managed by fake recruiters.
- Malicious Dependencies: The project files include dependencies pointing to compromised npm or PyPI packages.
- Automatic Installation: Package managers install these malicious components when the victim runs or debugs the code.
- Secondary Payload: The packages download second-stage malware from encrypted command-and-control servers.
- Remote Access Trojan (RAT): The final payload is a fully functional RAT, capable of:
- Executing arbitrary commands
- Uploading files and listing processes
- Checking for MetaMask browser extensions and other crypto wallets
The malware exists in three versions: JavaScript, Python, and Visual Basic Script, communicating with C2 servers via token-protected authentication, making reverse engineering extremely difficult.
Attribution to Lazarus Group
Several indicators point to North Korean origin:
- GMT+9 timezone in Git commits
- Focus on cryptocurrency-related social engineering
- Token-based C2 authentication, common in past Lazarus campaigns
- Consistent operational patience and modular malware design
Why Graphalgo is Particularly Dangerous
- Modular architecture allows operations to continue even if part of the campaign is exposed
- Exploits trusted workflows of crypto developers
- Multi-stage infection ensures malware survives initial detection
- RAT payload targets cryptocurrency assets, posing financial and operational risks
Mitigation Strategies
Developers and organizations can reduce risk by:
- Verifying packages before installation from npm or PyPI
- Using private mirrors or vetted registries for dependency management
- Running code in isolated sandboxes before execution
- Monitoring outgoing network connections for suspicious activity
- Educating developers about fake recruiter schemes and phishing attempts
Conclusion
The Graphalgo campaign highlights how state-sponsored actors weaponize open-source ecosystems and social engineering to compromise developers.
Cryptocurrency developers must adopt strict dependency hygiene, sandbox testing, and vigilance against social engineering. Organizations should also integrate threat intelligence and continuous monitoring to detect RATs or abnormal behaviors stemming from trusted repositories.