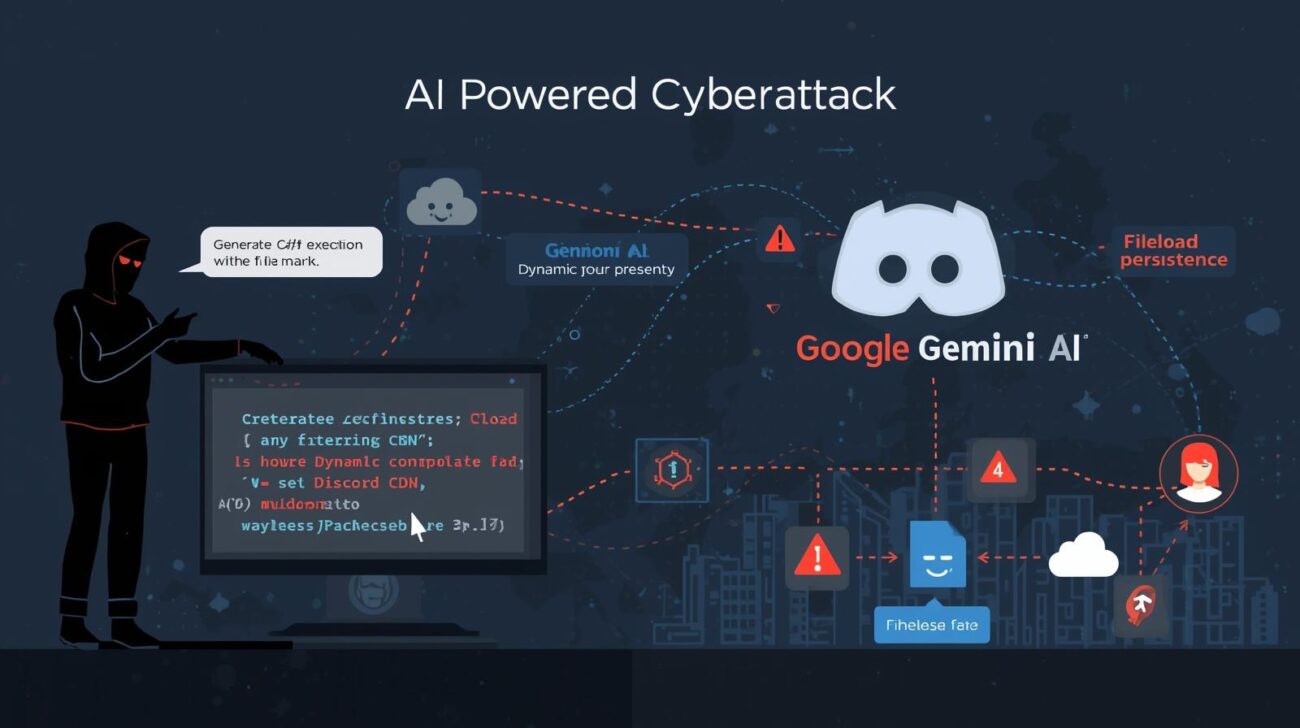
Google’s Threat Intelligence Group (GTIG) has revealed that threat actors are abusing Gemini AI to automate malware creation, accelerating multi-stage cyberattacks while evading traditional detection methods.
Dubbed HONESTCUE, this malware framework uses Google’s Gemini API to dynamically generate C# code, which is compiled and executed entirely in memory, leaving no files on disk. By doing so, attackers avoid static analysis and endpoint detection, creating significant challenges for cybersecurity teams.
This article explores how HONESTCUE works, the groups leveraging it, and recommended mitigation strategies for defenders.
How Attackers Leverage Gemini AI
Stage 1: API-Based Code Generation
HONESTCUE initiates its attack by sending carefully crafted prompts to the Gemini API, which returns compilable C# source code. The requests appear benign and blend into normal developer activity, bypassing AI safeguards.
Stage 2: In-Memory Compilation
Using .NET’s CSharpCodeProvider, the malware compiles the received code directly in memory. This approach:
- Eliminates disk artifacts
- Evades signature-based antivirus
- Makes behavioral detection extremely difficult
Stage 3: Payload Delivery
Once compiled, the malware downloads a secondary payload from attacker-controlled URLs, often hosted on trusted CDNs like Discord. Stage-two execution is performed in memory or via reflection, maintaining fileless persistence.
Stage 4: Multi-Stage Exploitation
The downloaded payload can:
- Perform reconnaissance on the target network
- Launch tools for credential theft, vulnerability probing, or lateral movement
- Maintain persistence while avoiding detection
This just-in-time malware generation mirrors prior techniques like PROMPTFLUX but leverages AI externally, outsourcing code creation to Google’s API.
Threat Actors and Use Cases
GTIG has observed nation-state APTs experimenting with Gemini AI:
- DPRK, Iranian (APT42), PRC (APT31, UNC795, APT41), and Russian groups
- Activities include phishing campaigns, vulnerability research, and C2 scripting
- APT31 role-played “security researchers” to probe remote code execution and bypass WAFs
Tests show the groups have modest capabilities, relying on automated code generation to accelerate operations, rather than fully sophisticated malware development.
Key Detection Challenges
HONESTCUE leverages several evasion techniques:
| Phase | Evasion Tactic | Detection Hurdle |
|---|---|---|
| Stage 1 | Gemini API query | Legitimate traffic to googleapis.com |
| Stage 2 | In-memory compile | No disk I/O, evades endpoint detection |
| Stage 3 | CDN payload | Trusted domains like Discord mask malicious activity |
Behavioral detection rules can include monitoring:
- CSharpCodeProvider usage for unusual compilation activity
- Unexpected Discord CDN fetches from endpoints
- High-volume API queries to Gemini outside normal development patterns
Mitigation and Defensive Measures
Security teams should implement hybrid defenses that combine network telemetry and runtime inspection:
- Monitor for anomalous Gemini API usage
- Block or alert on high-volume code generation requests
- Inspect in-memory .NET assemblies for unexpected behavior
- Leverage threat intelligence feeds, like GTI Collections, for IOCs
By adopting proactive monitoring and runtime analysis, organizations can detect fileless malware even when AI-generated.
Expert Perspective
Dr. Ilia Kolochenko, CEO of ImmuniWeb, emphasizes caution:
“Even if APTs utilize GenAI, it does not mean AI alone can create sophisticated malware. It accelerates simple processes but cannot replace skilled threat actors.”
He also highlights legal and ethical considerations for cloud AI providers like Google, given that nation-state actors actively exploit AI platforms for cyberattacks.
Conclusion
The emergence of HONESTCUE underscores a new era where AI is weaponized in cyberattacks, from reconnaissance to multi-stage payload delivery. Organizations must adapt by:
- Monitoring API and runtime behavior
- Blocking anomalous AI-generated activity
- Integrating threat intelligence into defense workflows
As AI tooling proliferates, defenders face a growing need for hybrid approaches combining behavioral monitoring, network inspection, and endpoint analysis to stay ahead of fileless, AI-powered threats.