A rapidly expanding cryptocurrency scam targeting Asia is blending two highly effective fraud models — malvertising and pig butchering scams — into one scalable, automated operation.
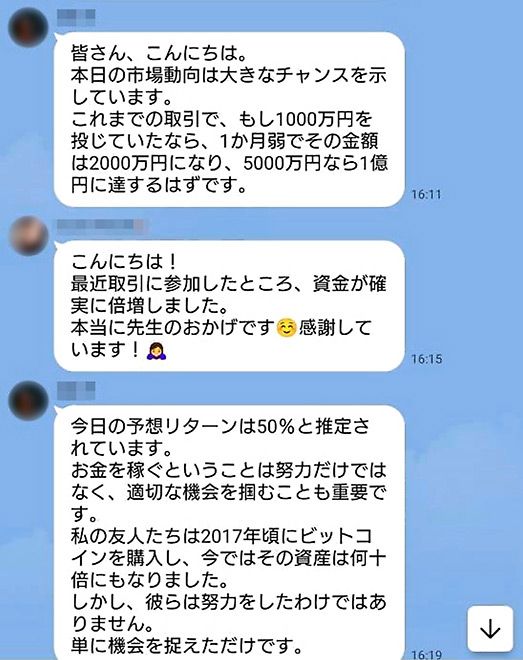
With a heavy focus on Japan, individual victims have reportedly lost up to ¥10 million in a single scheme.
Unlike traditional crypto scams that rely solely on social engineering, this campaign industrializes deception. It combines:
- Fake social media ads
- AI-driven chat engagement
- QR-code redirection
- Large-scale domain rotation
- Automated infrastructure
For CISOs, fraud analysts, threat intelligence teams, and fintech leaders, this operation represents a dangerous evolution in financially motivated cybercrime.
In this deep dive, we’ll analyze:
- How the hybrid malvertising + pig butchering model works
- The automation layer enabling scale
- The infrastructure and domain generation tactics
- Risk and financial impact
- Defensive measures for enterprises and individuals
What Is This Cryptocurrency Scam?
This campaign is a hybrid crypto fraud operation that merges:
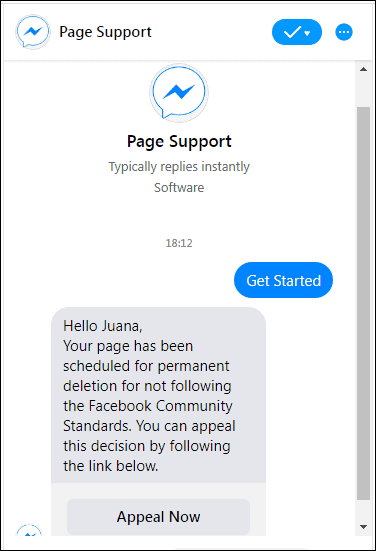
- Malvertising – malicious advertisements placed on legitimate platforms
- Pig butchering scams – long-term social engineering to extract increasing investments
The innovation lies in combining broad digital reach with psychological manipulation.
The result: highly convincing investment fraud at scale.
How the Attack Chain Works
Stage 1: Malvertising on Social Platforms
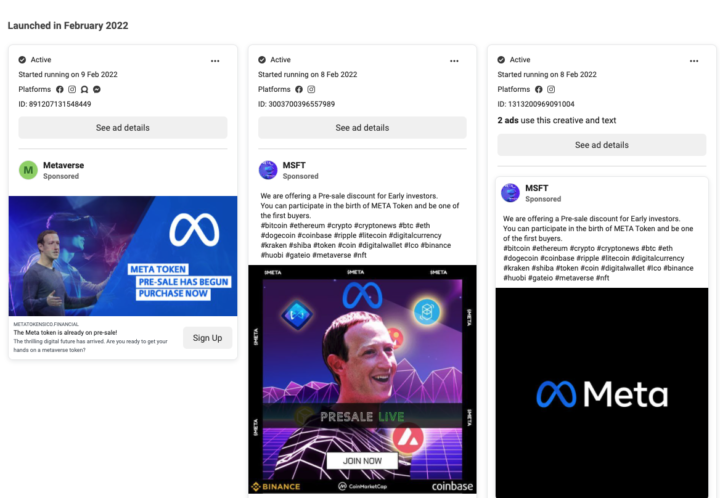

4
The attack begins with fake advertisements placed on platforms such as:
The ads typically:
- Impersonate well-known financial experts
- Promote “AI-driven” trading algorithms
- Promise exclusive, limited-access investment programs
- Display fake testimonials
These ads are polished and professionally designed, lowering suspicion.
Stage 2: Redirection to Fraudulent Investment Portals
After clicking the ad, victims are redirected to a fraudulent “lure” website designed to resemble a legitimate crypto trading platform.
Key characteristics include:
- Professional UI/UX design
- Fabricated performance dashboards
- Fake profit metrics
- Testimonials and success stories
The next step is critical.
Victims are prompted to scan a QR code to join a “private investment guidance” group on messaging apps such as:
- LINE
- KakaoTalk
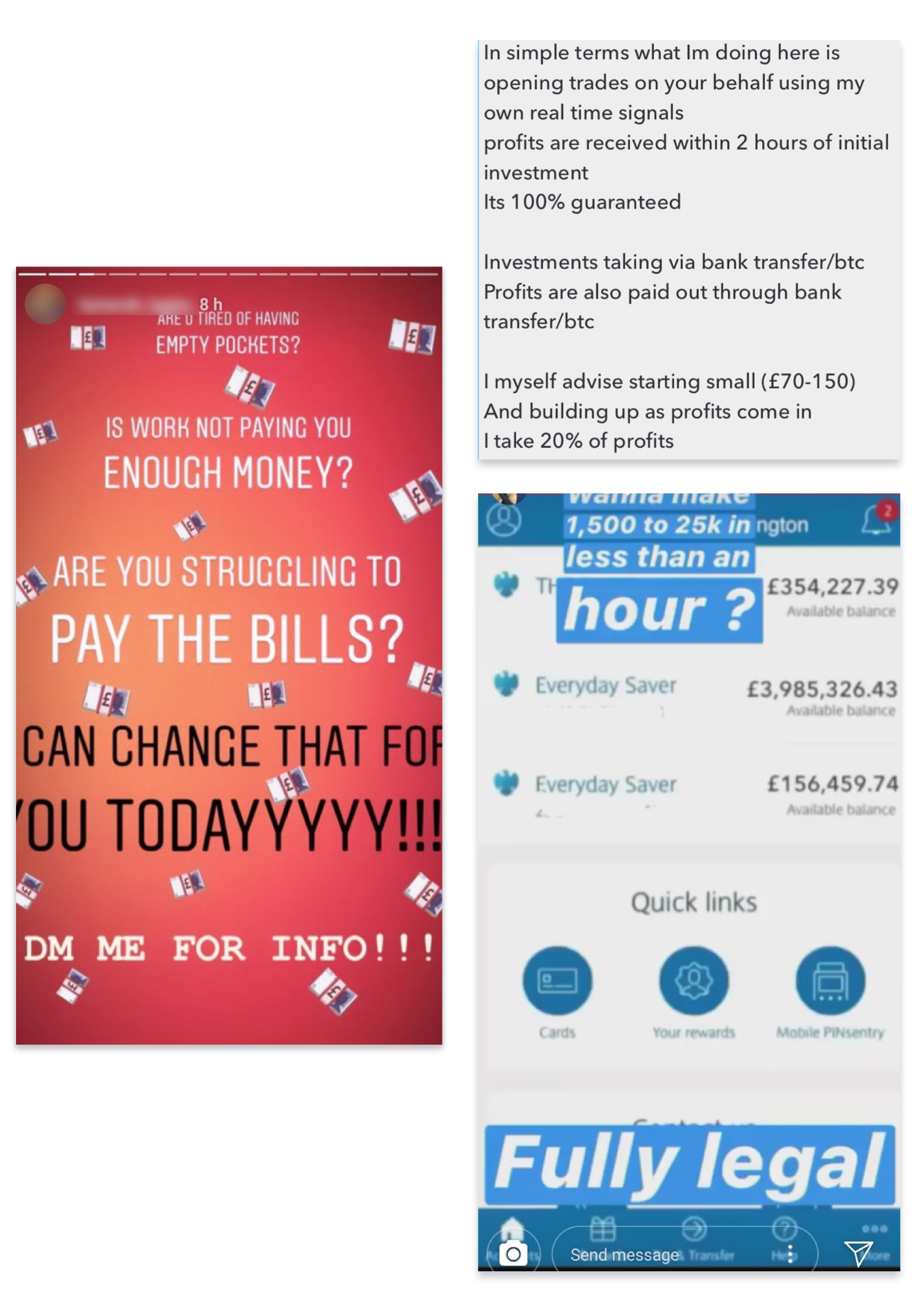
Stage 3: AI-Driven Social Engineering (Pig Butchering)

4
Once inside the chat group, the manipulation phase begins.
Unlike traditional pig butchering scams run by human operators, this campaign appears heavily automated.
Indicators include:
- Instant 24/7 responses
- Seamless language switching
- Scripted but natural conversational flow
- Coordinated group engagement
Victims are encouraged to:
- Make a small initial investment
- Observe fake “high returns” in a controlled dashboard
- Increase deposits significantly
Eventually, when the victim attempts withdrawal:
- A “release fee” or “tax” is demanded
- Additional payments are requested
- Communication stops
The funds are gone.
Automation & Infrastructure at Scale
This campaign is not small-scale fraud.
It leverages Registered Domain Generation Algorithms (RDGAs) to produce thousands of new domains rapidly.
Why RDGAs Matter
- Rapid domain rotation evades blocklists
- Lookalike names enhance legitimacy
- Large domain clusters complicate takedown efforts
Over 23,000 domains have been linked to this ecosystem, with disproportionate activity observed in Japan.
Signs of AI-Assisted Operations


4
Security researchers identified characteristics suggesting automation:
- Continuous chat activity
- No delay in responses
- Highly consistent messaging tone
- Infrastructure shared across multiple campaigns
This indicates a fraud-as-a-service model, enabling multiple threat actors to operate simultaneously using the same backend systems.
Why This Campaign Is So Effective
1. Platform Trust Abuse
Victims trust ads displayed on major social networks.
2. Psychological Grooming
Pig butchering scams rely on:
- Trust building
- Emotional engagement
- Gradual financial escalation
3. AI Scalability
Automation removes labor constraints, allowing:
- Global targeting
- Multilingual engagement
- 24/7 victim interaction
4. Crypto Irreversibility
Cryptocurrency transactions:
- Are difficult to reverse
- Bypass traditional fraud detection systems
- Often lack consumer protections
Financial & Business Impact
| Impact Area | Risk Level | Description |
|---|---|---|
| Individual Financial Loss | Severe | Up to ¥10 million per victim |
| Brand Impersonation Damage | High | Abuse of financial expert reputations |
| Platform Trust Erosion | High | Reduced trust in social ads |
| AML Compliance Concerns | Medium | Potential regulatory scrutiny |
For financial institutions and crypto exchanges, this raises concerns about:
- Anti-Money Laundering (AML) monitoring
- Transaction anomaly detection
- Cross-border fraud tracing
Common Red Flags
🚩 Guaranteed returns
🚩 “AI-powered secret algorithm” claims
🚩 Urgent investment deadlines
🚩 QR codes leading to chat apps
🚩 Withdrawal fees
🚩 Requests for additional deposits to unlock funds
Defensive Recommendations
For Individuals
- Verify official accounts before trusting financial ads
- Avoid scanning QR codes from unverified sources
- Never transfer cryptocurrency to strangers met in chat groups
- Be skeptical of unrealistic returns
For Enterprises & Security Teams
1. Monitor Suspicious Domains
- Implement DNS threat intelligence feeds
- Track RDGA-like patterns
2. Strengthen Brand Protection
- Monitor impersonation domains
- Collaborate with registrars for takedown
3. Enhance Fraud Detection
- Monitor large outbound crypto transfers
- Flag new wallet interactions
- Deploy behavioral anomaly detection
4. Improve User Education
- Awareness campaigns about pig butchering tactics
- Warning banners for crypto-related ads
FAQs
1. What is a pig butchering crypto scam?
A long-term investment fraud where scammers build trust before persuading victims to invest increasing amounts of money.
2. How does malvertising contribute to crypto scams?
Malicious ads redirect users to fraudulent investment sites that initiate the social engineering process.
3. Why is Japan heavily targeted?
Researchers observed a disproportionate number of malicious domain queries originating from Japan.
4. What is an RDGA?
A Registered Domain Generation Algorithm automatically creates thousands of domains to evade detection and blocking.
5. Are AI bots being used in these scams?
Evidence suggests automated chat systems are engaging victims to scale operations efficiently.
6. Can victims recover funds?
Cryptocurrency recovery is difficult. Immediate reporting to exchanges and law enforcement improves chances but does not guarantee recovery.
Conclusion
This cryptocurrency scam targeting Asia represents the industrialization of financial fraud.
By merging:
- Malvertising reach
- AI-driven pig butchering
- Automated domain generation
- Crypto payment channels
Threat actors have created a scalable, high-yield fraud engine.
For security leaders, this is a warning:
AI is not only transforming defense — it’s transforming fraud.
Now is the time to:
- Strengthen domain monitoring
- Improve fraud detection systems
- Educate users on crypto investment scams
- Collaborate across industry for intelligence sharing
In cryptocurrency markets, trust moves money.
And attackers are exploiting that trust at scale.
