Global vulnerability management depends on one core principle: timely disclosure.
But new research into China’s dual vulnerability databases — China National Vulnerability Database (CNVD) and China National Vulnerability Database of Information Security (CNNVD) — reveals a different disclosure timeline than what Western defenders see via National Vulnerability Database (NVD) and **MITRE Corporation’s CVE program.
This dual structure creates informational asymmetry, where vulnerabilities may appear in Chinese databases months before they are fully documented in international CVE systems.
For enterprise security teams, this introduces a dangerous exposure window:
Attackers may already be exploiting vulnerabilities that defenders don’t yet see in their primary intelligence feeds.
In this deep dive, we’ll explore:
- How CNVD and CNNVD differ from CVE/NVD
- What disclosure delays mean for enterprise risk
- Real examples, including Microsoft OneDrive DLL hijacking
- Strategic implications for global vulnerability management
- How security teams can adapt
Understanding China’s Dual Vulnerability Ecosystem
China maintains two major vulnerability tracking systems:
1️⃣ CNNVD
Operated under state oversight and largely aligned with the global CVE system.
- Often mirrors MITRE CVE entries
- Tracks internationally recognized vulnerabilities
- Serves a centralized national registry function
2️⃣ CNVD
Operates with more independence and frequently publishes:
- Unique vulnerability entries
- Non-CVE-mapped disclosures
- Different severity assessments
- Independent timelines


4
While both databases have scaled significantly in volume, the key finding isn’t growth.
It’s latency.
The Core Risk: Informational Asymmetry
The primary attack vector here is not a technical exploit.
It’s timing.
When a vulnerability appears in CNVD months before it is reflected in CVE/NVD:
- Western defenders lack official identifiers
- SIEM detection rules may not exist
- Patch prioritization workflows are not triggered
- Threat hunting queries may not be written
This creates what researchers describe as a “blind exposure window.”
Attackers aware of these early disclosures can:
- Weaponize the flaw
- Target global enterprises
- Operate undetected during the disclosure gap
Case Study: Microsoft OneDrive DLL Hijacking
A Microsoft OneDrive DLL hijacking vulnerability was cataloged in Chinese systems before a comparable CVE entry appeared internationally.
This lag allowed potential exploitation before global patch cycles and security advisories reacted.
Similar reference points include:
- CVE-2021-40444 (MSHTML RCE)
- CVE-2024-33698
In some cases:
- CNVD entries resemble existing CVEs
- Others remain “shadow vulnerabilities” with no direct mapping
This creates discrepancies in severity scoring and response urgency.
Strategic Disclosure Delays

4
Research comparing publication timestamps shows:
- Delays between vulnerability submission and public release
- “Arcs” of latency exceeding one week — sometimes far longer
- High-severity flaws withheld from broader disclosure
This delay effectively turns vulnerability data into:
A strategic national security asset rather than a universally shared security resource.
For global enterprises, the impact is clear:
No public CVE = No enterprise patch prioritization trigger.
The “Shadow Vulnerability” Inventory
A significant percentage of CNVD entries:
- Do not immediately map to a CVE
- Use independent identifiers
- Assign differing severity levels
This results in:
- Divergent risk scoring across regions
- Detection engineering gaps
- Incomplete threat intelligence feeds
Security teams relying exclusively on NVD may miss early warning signals.
Enterprise Impact Analysis
| Impact Area | Risk Level | Description |
|---|---|---|
| Patch Prioritization | High | Delayed remediation workflows |
| Threat Detection | High | Missing IOCs & detection signatures |
| Global Risk Visibility | Medium-High | Partial vulnerability intelligence |
| Compliance Reporting | Medium | Inconsistent severity scoring |
For multinational organizations, this creates governance complexity:
- Which vulnerability timeline do you follow?
- How do you reconcile severity differences?
- How do you handle non-CVE identifiers?
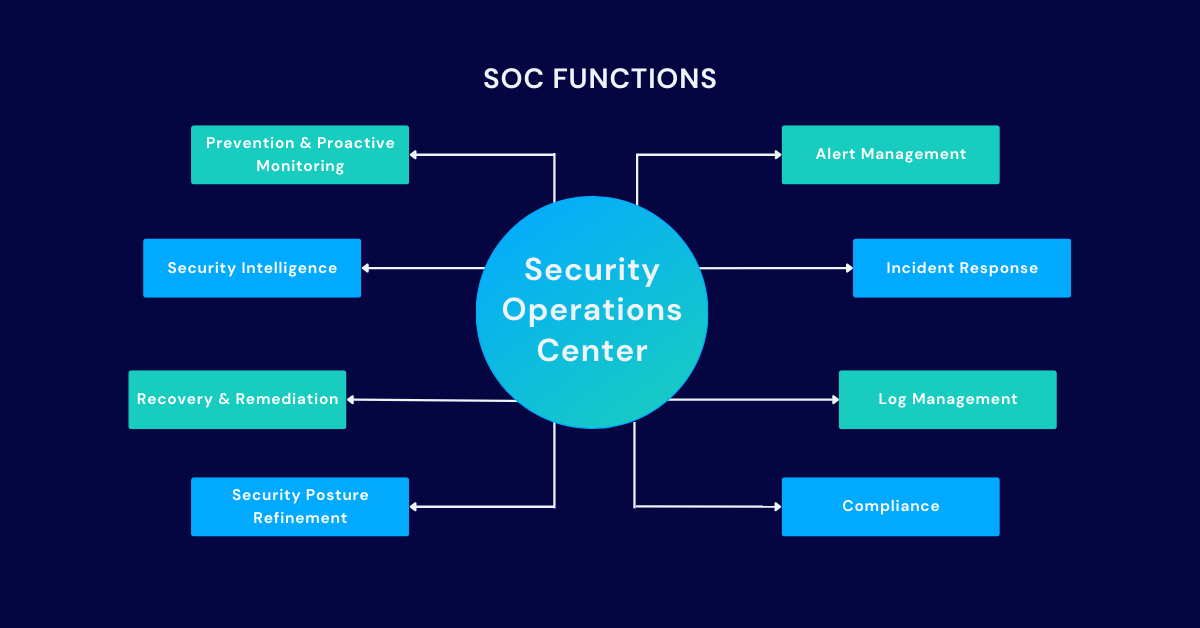
Why This Matters for CISA, SOC & DevSecOps Teams
Modern vulnerability management workflows rely heavily on:
- CVE identifiers
- NVD severity scores (CVSS)
- KEV catalog inclusion
- Automated ticketing systems
If a vulnerability does not appear in CVE:
- Automation breaks
- Risk dashboards remain green
- Security posture appears falsely stable
Attackers thrive in these gaps.
Defensive Recommendations
1️⃣ Expand Threat Intelligence Sources
Incorporate:
- CNVD feeds
- CNNVD data
- Regional advisories
Do not rely solely on NVD enrichment pipelines.
2️⃣ Implement Intelligence Correlation
Use tooling to:
- Cross-map CNVD entries to internal software inventories
- Flag non-CVE vulnerabilities
- Track independent severity ratings
3️⃣ Adopt an “Early Signal” Framework
Treat foreign database disclosures as:
- Early warning indicators
- Pre-CVE intelligence
- Threat hunting triggers
4️⃣ Strengthen Detection Engineering
Because delayed disclosure often hides:
- Indicators of Compromise (IOCs)
- Exploit patterns
- Initial infection vectors
SOC teams should proactively hunt based on:
- Behavioral anomalies
- Unusual DLL loads
- Suspicious OneDrive process chains
FAQs
1. What is CNVD?
China National Vulnerability Database, which tracks vulnerabilities independently from CVE in many cases.
2. How does CNNVD differ from CNVD?
CNNVD more closely mirrors MITRE’s CVE list, while CNVD often publishes unique entries and independent timelines.
3. Why are disclosure delays dangerous?
They create a window where attackers may exploit vulnerabilities before defenders receive official CVE data.
4. Are these vulnerabilities only relevant to China?
No. Software like Microsoft OneDrive is globally deployed, meaning exploitation risk is international.
5. How should enterprises respond?
Broaden vulnerability intelligence sources and correlate non-CVE entries with internal asset inventories.
Conclusion
The divergence between CNVD, CNNVD, and CVE/NVD is more than an academic observation.
It highlights a new strategic dimension of cybersecurity:
Vulnerability disclosure timing can shape the threat landscape.
For enterprise security leaders, the lesson is clear:
- Expand intelligence beyond traditional Western feeds
- Monitor foreign vulnerability databases
- Treat early disclosures as actionable intelligence
In a world where attackers exploit milliseconds,
a months-long disclosure delay is not a gap.
It’s an opportunity.
