In 2025 alone, more than 6,200 adversarial domain name cases were recorded, contributing to a 68% … Digital Squatting Attacks: How Lookalike Domains Steal CredentialsRead more
Latest News
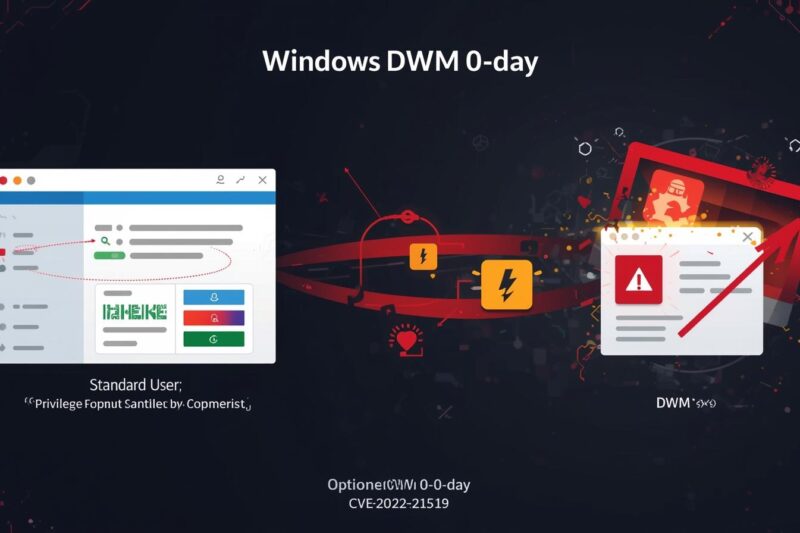
Desktop Window Manager 0-Day CVE-2026-21519 Enables Privilege Escalation
Microsoft has released urgent security updates for a critical zero-day vulnerability in the Desktop Window Manager … Desktop Window Manager 0-Day CVE-2026-21519 Enables Privilege EscalationRead more
Microsoft Word 0-day Vulnerability CVE-2026-21514 Actively Exploited in the Wild
A critical zero-day vulnerability in Microsoft Word, tracked as CVE-2026-21514, has been actively exploited in the … Microsoft Word 0-day Vulnerability CVE-2026-21514 Actively Exploited in the WildRead more
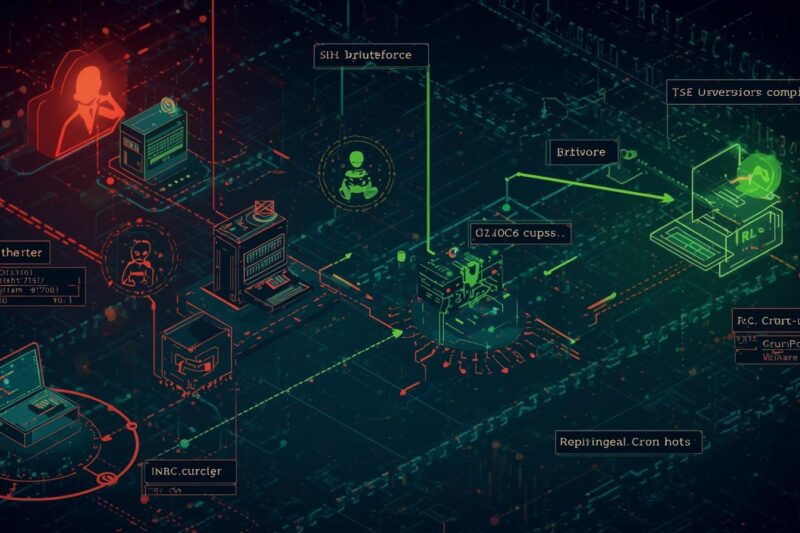
Legacy IRC Botnet SSHStalker Automates SSH Attacks to Compromise Linux Hosts
A new Linux botnet campaign, dubbed SSHStalker, has been uncovered exploiting weak SSH credentials to compromise … Legacy IRC Botnet SSHStalker Automates SSH Attacks to Compromise Linux HostsRead more
Urgent: Fiber v2 UUID Flaw Enables Session Hijacks & CSRF
A critical vulnerability has been discovered in Fiber v2, a widely used Go web framework, that … Urgent: Fiber v2 UUID Flaw Enables Session Hijacks & CSRFRead more
BQTLock & GREENBLOOD Ransomware Target Organizations to Encrypt and Exfiltrate Data
Two sophisticated ransomware families, BQTLock and GREENBLOOD, are redefining modern ransomware threats. Unlike traditional ransomware attacks … BQTLock & GREENBLOOD Ransomware Target Organizations to Encrypt and Exfiltrate DataRead more
Beware: macOS AMOS Stealer Hits Users via AI and Google Ads
A sophisticated social engineering campaign is targeting Mac users by combining the trustworthiness of AI platforms … Beware: macOS AMOS Stealer Hits Users via AI and Google AdsRead more
Critical SandboxJS Vulnerability Enables Remote Host Takeover
A critical sandbox escape vulnerability has been discovered in SandboxJS, a popular JavaScript library used to … Critical SandboxJS Vulnerability Enables Remote Host TakeoverRead more
Prometei Botnet Targets Windows Servers to Deploy Malware
The Prometei botnet, active since 2016, has emerged as a sophisticated threat targeting Windows Server systems. … Prometei Botnet Targets Windows Servers to Deploy MalwareRead more
Massive Spike in Exploitation of Ivanti EPMM CVE-2026-1281
On February 9, 2026, Shadowserver scans detected over 28,300 unique IP addresses attempting to exploit CVE-2026-1281, … Massive Spike in Exploitation of Ivanti EPMM CVE-2026-1281Read more