Modern data pipelines power everything from fraud detection systems to healthcare analytics. But what happens when a trusted automation engine becomes the weak link?
The newly disclosed Apache NiFi authorization bypass vulnerability (CVE-2026-25903) exposes organizations to privilege escalation risks within their data flow environments. Affecting versions 1.1.0 through 2.7.2, this high-severity flaw allows lower-privileged users to modify restricted components — undermining carefully designed access control boundaries.
For CISOs, SOC teams, and DevOps leaders, this is more than a patching advisory. It’s a reminder that authorization design flaws can silently erode zero trust principles inside critical data infrastructure.
In this deep-dive, you’ll learn:
- What CVE-2026-25903 is and how it works
- Why authorization bypass vulnerabilities are dangerous
- Real-world attack implications
- Compliance and regulatory risks
- Mitigation strategies aligned with NIST and Zero Trust models
Understanding Apache NiFi and Restricted Components
4
What Is Apache NiFi?
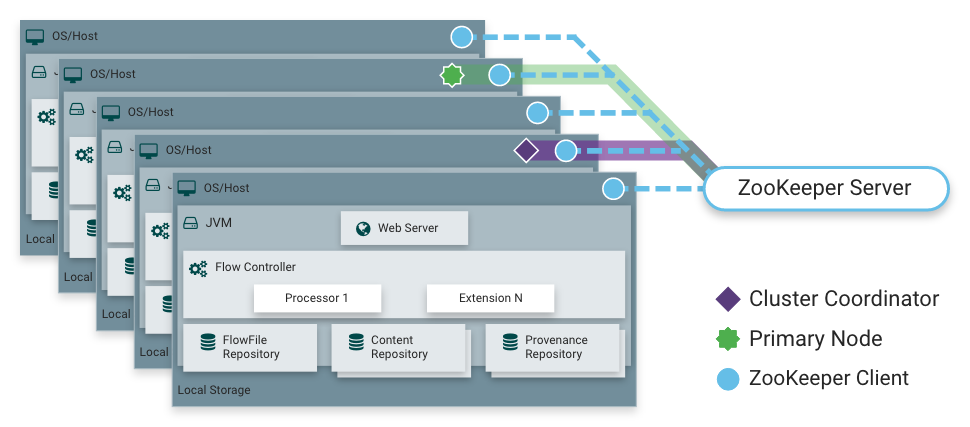
Apache NiFi is an open-source data flow automation platform designed to:
- Collect and ingest data
- Transform and route data
- Automate complex workflows
- Manage high-volume streaming pipelines
It is widely deployed in:
- Financial services
- Healthcare systems
- Government infrastructure
- Cloud-native DevOps pipelines
Given its central role in data orchestration, security misconfigurations in NiFi can have systemic impact.
What Are Restricted Components?
Within NiFi, certain processors and controller services are annotated as “Restricted.”
These components:
- Can execute system-level commands
- Access sensitive files or credentials
- Interact with external systems
- Modify critical processing logic
To protect environments, NiFi enforces additional privileges before users can:
- Add restricted components
- Modify their configurations
This is where CVE-2026-25903 becomes critical.
What Is CVE-2026-25903?
| CVE ID | Description | Affected Versions | Severity |
|---|---|---|---|
| CVE-2026-25903 | Missing authorization checks allow low-privileged users to modify restricted components | 1.1.0–2.7.2 | High |
The vulnerability stems from missing authorization validation during configuration updates of restricted extension components.
The Core Issue
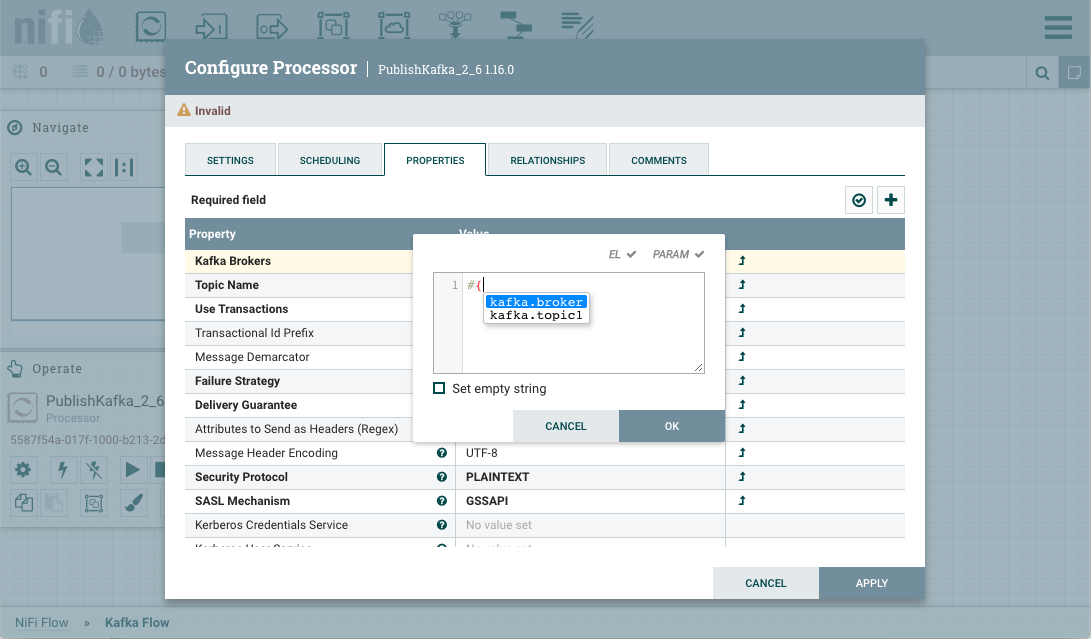
Although restricted components required elevated privileges to be added to the data flow, the framework failed to enforce the same checks when:
Updating configuration properties of those components.
In simple terms:
- A privileged user adds a restricted processor.
- A lower-privileged user later edits its configuration.
- No proper authorization check blocks the modification.
This creates an authorization bypass condition.
How the Authorization Bypass Works
Step-by-Step Exploitation Scenario
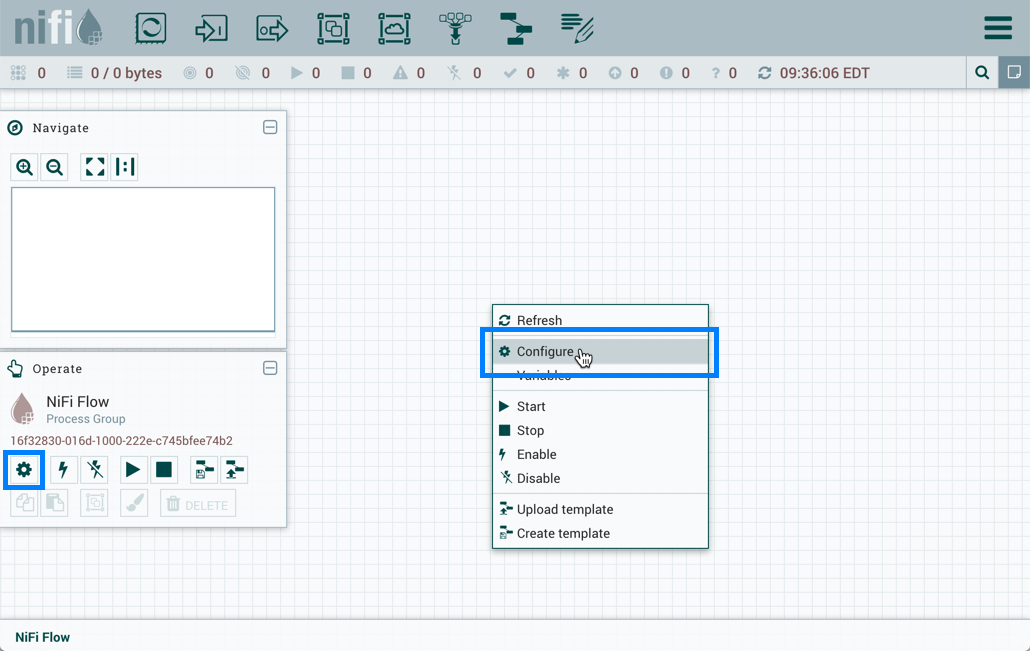
- A trusted admin deploys a restricted component.
- A user with limited permissions accesses the workflow.
- The user modifies processor configuration settings.
- NiFi fails to validate the restricted privilege requirement.
- Malicious logic or unsafe commands are introduced.
Why This Is Dangerous
Restricted processors may:
- Execute shell commands
- Interact with databases
- Send data to external endpoints
- Trigger downstream automation
An attacker could:
- Redirect sensitive data streams
- Insert malicious transformation logic
- Disable validation controls
- Trigger command execution pathways
This effectively undermines role-based access control (RBAC) principles.
Risk Impact Analysis
1. Privilege Escalation
While not a traditional system-level privilege escalation, it enables workflow-level privilege abuse, which can be just as dangerous in data-centric environments.
2. Data Integrity Compromise
Tampering with processors can:
- Alter transaction data
- Modify audit logs
- Manipulate compliance reporting streams
For regulated industries, this is severe.
3. Data Exfiltration
Attackers could modify routing logic to:
- Forward sensitive data externally
- Create shadow pipelines
- Insert covert data export mechanisms
4. Compliance Violations
This vulnerability directly affects:
- NIST SP 800-53 AC controls (Access Control)
- ISO/IEC 27001 Annex A.9
- SOC 2 Logical Access Requirements
- HIPAA Security Rule (if PHI pipelines are involved)
Failure to enforce authorization boundaries could result in:
- Audit findings
- Regulatory penalties
- Legal exposure
Real-World Enterprise Scenarios
Scenario 1: Financial Services
A restricted processor performs transaction validation before settlement.
A malicious user:
- Modifies validation thresholds
- Allows fraudulent transactions
- Bypasses compliance checks
Impact: Financial fraud + regulatory scrutiny.
Scenario 2: Healthcare Data Pipelines
A restricted component encrypts PHI before transmission.
A low-privileged insider:
- Alters encryption configuration
- Weakens cryptographic parameters
- Sends unencrypted data
Impact: HIPAA breach, reputational damage.
Scenario 3: Cloud DevOps Automation
NiFi triggers CI/CD automation via system commands.
An attacker:
- Modifies execution parameters
- Injects malicious scripts
- Compromises build pipelines
Impact: Supply chain attack vector.
Why This Vulnerability Matters in Zero Trust Architectures
Zero Trust security is built on:
- Explicit verification
- Least privilege
- Continuous authorization validation
CVE-2026-25903 violates:
“Never trust, always verify.”
Even after privilege gating during component creation, NiFi failed to verify privileges during updates — exposing a trust gap in the authorization lifecycle.
MITRE ATT&CK Mapping
The vulnerability aligns with potential tactics such as:
- Privilege Escalation
- Persistence
- Exfiltration
- Defense Evasion
Specifically:
- Abuse of access control mechanisms
- Modify application configuration
- Command execution via trusted components
How Apache Addressed the Issue
The flaw was responsibly reported by security researcher David Handermann.
The fix was implemented in:
Apache NiFi version 2.8.0
The update ensures:
- Proper authorization checks on restricted component updates
- Consistent enforcement of privilege boundaries
- Stronger validation in the authorization model
Organizations running 1.1.0–2.7.2 must upgrade immediately.
Mitigation & Best Practices
Immediate Actions
- Upgrade to NiFi 2.8.0 or later
- Audit restricted component usage
- Review RBAC configurations
- Enable detailed audit logging
Strengthen Authorization Controls
Implement:
- Principle of Least Privilege (PoLP)
- Segregation of duties
- Multi-factor authentication for privileged roles
- Periodic access reviews
Continuous Monitoring
SOC teams should:
- Monitor configuration changes
- Alert on restricted processor modifications
- Log and review workflow edits
- Correlate NiFi logs with SIEM tools
Hardened Configuration Checklist
- Disable unused processors
- Restrict shell execution processors
- Validate outbound connections
- Isolate NiFi in segmented network zones
- Apply zero trust network access (ZTNA)
Common Misconceptions
“We Don’t Use Restricted Components”
If restricted components exist in your instance, even if added by admins, they remain exploitable until patched.
“We Don’t Separate Privilege Levels”
Environments without distinct privilege levels may see reduced exposure — but this is not a security best practice.
Lack of RBAC separation increases overall risk.
“It’s Not Remote Code Execution”
True — but configuration-level abuse can indirectly enable execution pathways.
Workflow-level manipulation can be equally impactful.
Frequently Asked Questions (FAQs)
1. What is CVE-2026-25903?
CVE-2026-25903 is a high-severity authorization bypass vulnerability in Apache NiFi that allows low-privileged users to modify restricted components.
2. Which NiFi versions are affected?
Versions 1.1.0 through 2.7.2 are vulnerable. The issue is fixed in 2.8.0.
3. Can this lead to remote code execution?
Not directly, but attackers may modify processors that execute commands, potentially enabling indirect command execution.
4. Is this exploitable remotely?
Exploitation requires authenticated access with limited privileges.
5. How serious is this vulnerability?
High severity. It impacts authorization boundaries, data integrity, and potentially compliance obligations.
6. How can organizations prevent similar issues?
- Enforce strict RBAC
- Conduct regular authorization audits
- Adopt Zero Trust principles
- Monitor configuration changes
Strategic Security Takeaways
Authorization flaws are often more dangerous than injection flaws because they undermine trust at the architecture level.
CVE-2026-25903 highlights:
- The importance of lifecycle-based authorization checks
- The risk of assuming one-time privilege validation is sufficient
- The need for defense-in-depth in automation platforms
For organizations relying on Apache NiFi for mission-critical pipelines, patching is non-negotiable.
Conclusion
The Apache NiFi authorization bypass vulnerability (CVE-2026-25903) is a stark reminder that security controls must be enforced consistently across every action — not just at creation time.
While not a traditional remote exploit, the impact on data integrity, workflow trust, and compliance posture makes this a high-priority remediation item.
If your organization:
- Handles regulated data
- Uses restricted processors
- Relies on automated pipelines
You should:
- Upgrade immediately
- Audit configurations
- Strengthen authorization governance
Now is the time to reassess your data flow security model and ensure it aligns with Zero Trust principles.