A new and highly sophisticated JackFix attack—an evolution of the known ClickFix malware technique—is targeting users through fake adult websites and malvertising campaigns. Security researchers warn that this threat uses a fake Windows Update screen to hijack the victim’s browser and trick them into running malicious commands that initiate a multistage malware infection.
Malvertising Lures Users Into Fake Adult Sites
The campaign begins with attackers cloning popular adult platforms such as xHamster and Pornhub. These counterfeit sites are often promoted through shady ad networks, a common vector for modern malvertising attacks.
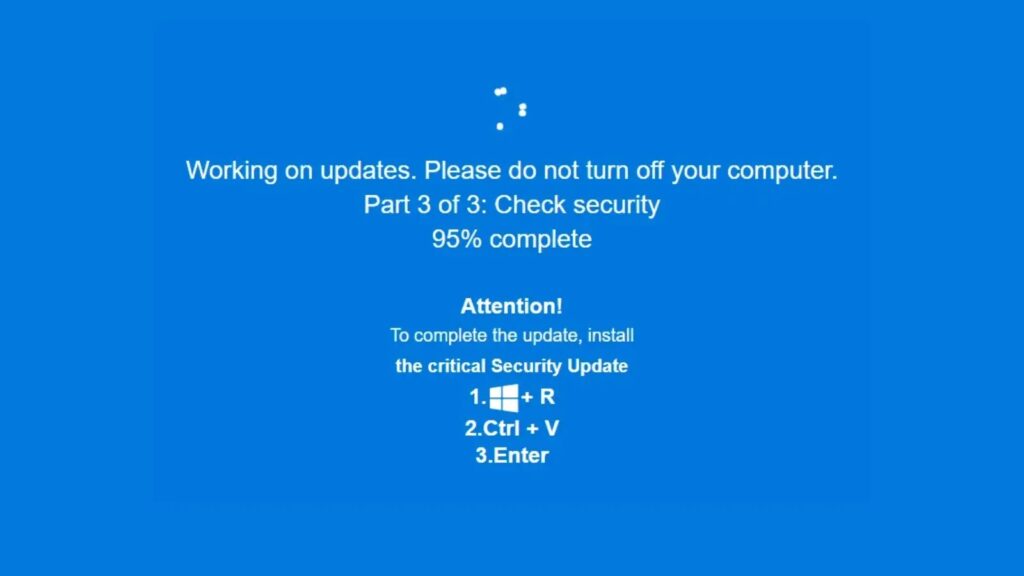
Once a user clicks on one of these fake websites, the JackFix infection chain is triggered. The malicious webpage instantly forces the browser into full-screen mode and displays a convincing “Critical Windows Security Update” prompt. The fake interface features:
- Windows-style blue security screens
- Progress bars and update animations
- Disabling of escape keys like Esc and F11
- A fullscreen overlay that blocks normal browser controls
This screen-hijacking attack creates psychological pressure, combining the urgency of a security update with the embarrassment of being caught on adult content—leading many victims to comply without hesitation.
Screen Locking With Realistic Windows Update Prompts
The overlay mimics legitimate Windows update behaviors, making it appear as though the operating system has triggered a mandatory patch. Although the fake update screen cannot fully block all browser escape methods, it is convincing enough to trap less-savvy users.
This tactic resembles older screen-locker malware, but with far more advanced obfuscation, automation, and social-engineering elements—making it harder for users to realize they are interacting with a phishing page instead of Windows itself.
Advanced Obfuscation and Redirection Techniques
The JackFix malware campaign uses multiple layers of obfuscation to avoid detection:
1. Obfuscated Commands and Payloads
The attackers hide not only the malware payloads but also the commands used to execute the ClickFix sequence. This helps the attack bypass common endpoint protection tools.
2. Smart URL Redirection
Malicious URLs used in the attack behave differently depending on how they are accessed:
- Direct access redirects users to legitimate sites such as Google or Steam
- PowerShell-invoked access delivers the true malware payload
This technique evades automated scanners like VirusTotal and helps the campaign remain undetected for longer periods.
Multistage Attack Chain: From Fake Update to Full Malware Drop
Once a user follows the on-screen instructions and executes the provided commands, the infection begins:
- mshta.exe launches as the initial loader
- mshta spawns a PowerShell downloader
- The downloader floods the user with UAC prompts, making the system nearly unusable
- Upon gaining admin privileges, the script unleashes a massive multistage malware payload
Researchers describe this as a “spray-and-prey” malware strategy, where a single compromise can drop up to eight different malware variants simultaneously.
Payloads Include Multiple Info-Stealers and RATs
The JackFix campaign deploys several high-risk malware strains, including:
- Rhadamanthys stealer
- Vidar 2.0
- RedLine stealer
- Amadey botnet client
- Various loaders and Remote Access Trojans (RATs)
This shotgun-style infection ensures that even if some payloads are blocked, others will succeed—significantly increasing the risk of:
- Credential theft
- Cryptocurrency wallet compromise
- Browser data exposure
- Long-term remote access by attackers
A High-Risk, Rapidly Evolving Cyber Threat
Security researchers warn that the JackFix attack represents a dangerous fusion of psychological manipulation, screen-locking techniques, obfuscation, and multi-payload delivery. The combination of fake Windows updates, adult-site lures, and PowerShell-based execution makes this campaign both stealthy and highly effective.
As the malware continues to evolve, users and organizations must remain vigilant and ensure protections are updated to detect emerging fake Windows update scams, malvertising threats, and browser-based social engineering attacks.
